Executive Summary: The 15-Minute Kill Chain
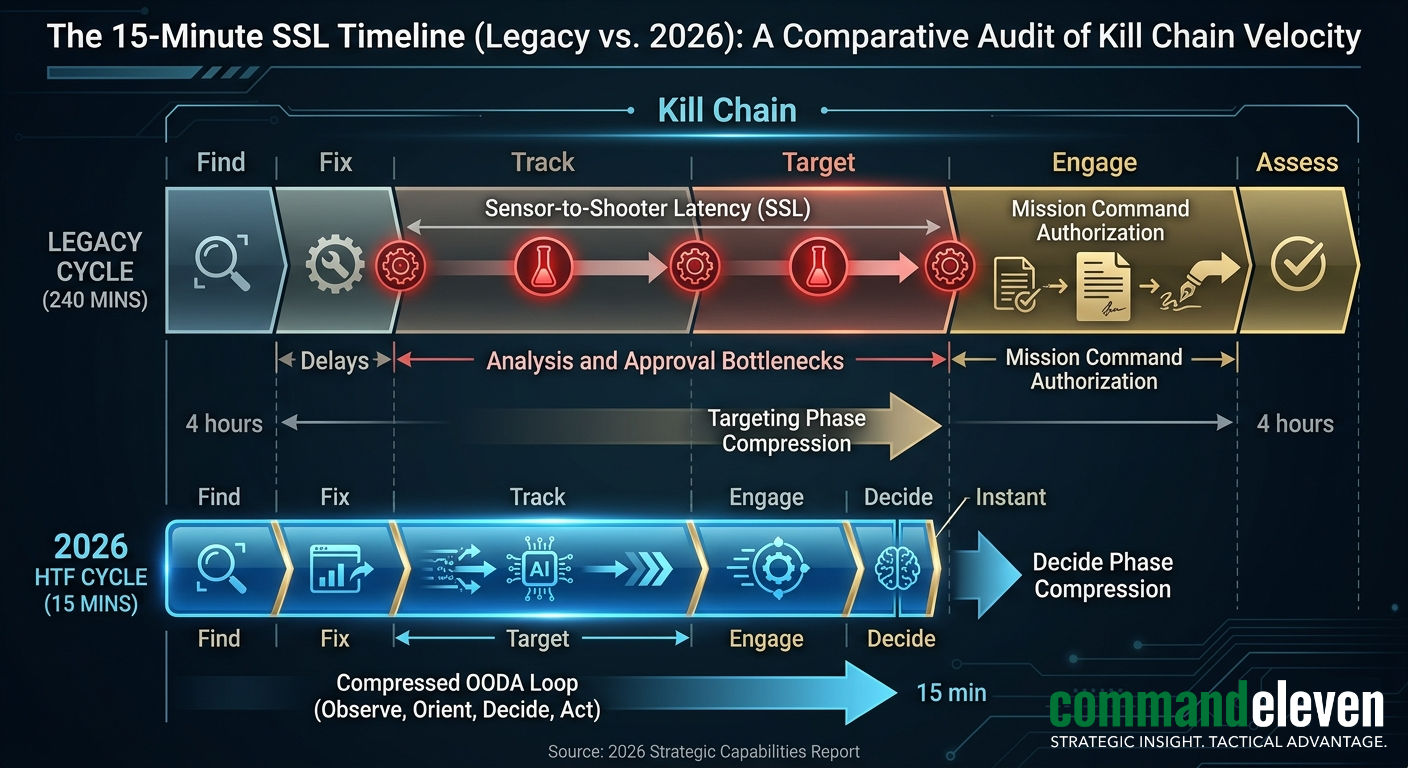
In the 2026 multi-domain environment, the traditional intelligence cycle – Planning, Collection, Processing, Analysis, Dissemination – is functionally obsolete for kinetic operations. The Unified Threat Matrix (UTM) now demands a “Live” intelligence posture. This analysis defines the Hybrid Targeting Fusion (HTF) model, which integrates global Open-Source Intelligence (OSINT) scraping with localized, high-fidelity Human Intelligence (HUMINT). The goal is a Sensor-to-Shooter Latency (SSL) of under 15 minutes, allowing for the engagement of fleeting, “Blink-mode” targets within the Mosaic Defense architecture.
Key Takeaways
- Sensor-to-Shooter Latency (SSL) must be under 15 minutes to counter “Blink-mode” assets.
- OSINT provides the geospatial cue; HUMINT provides the Ground-Truth (PID).
- HTF turns the “Noise” of the Mosaic Defense into a high-confidence targeting signal.
The Mathematical Reality of Latency
SSL is defined by the equation
SSL = Tc + Tp + Ta + Td + Te
where:
- Tc – (Collection): Raw data acquisition (SAR, AIS, SBM signal).
- Tp – (Processing): AI-driven normalization and noise reduction.
- Ta – (Analysis): Cross-domain correlation (OSINT + HUMINT).
- Td – (Decision): Mission Command authorization.
- Te – (Execution): Time-of-flight for the kinetic asset.
In legacy systems, Ta and Td represented 80% of the timeline. The HTF Model utilizes machine-speed correlation to compress these variables, targeting a systemic SSL reduction of 90%.
The Technical Evolution of the Sensor-to-Shooter Cycle
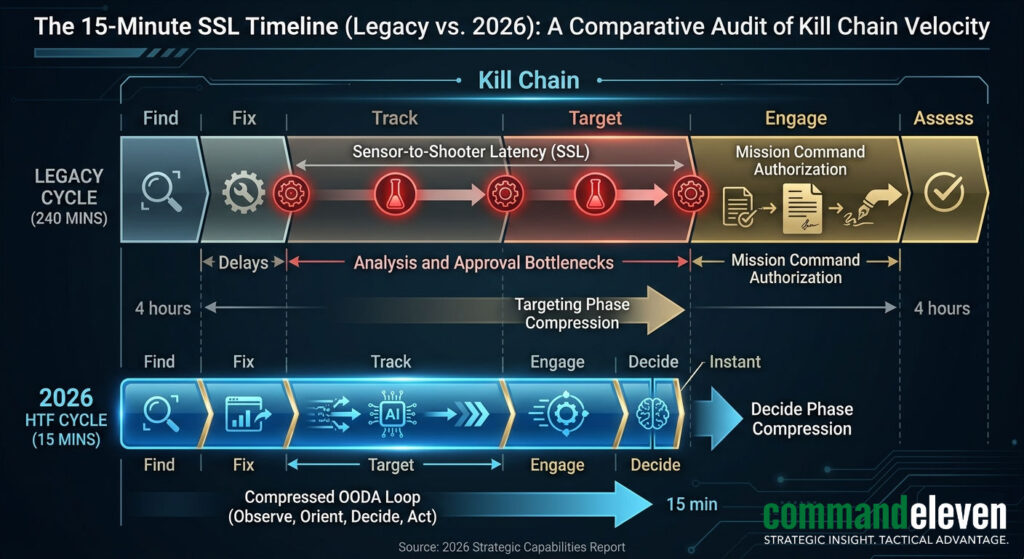
Historically, the “Kill Chain” was a linear progression. In the Multi-Domain Battlespace (MDB) of 2026, this has been replaced by a Targeting Mesh. The objective is to reduce Sensor-to-Shooter Latency (SSL) to under 15 minutes—the “Golden Window” before a mobile Mosaic Defense node can displace.
The OSINT Layer: Algorithmic Saliency and Digital Scraping
Modern OSINT is the “Wide-Area Surveillance” of the digital age. It provides the initial Target Cue that triggers the rest of the mesh.
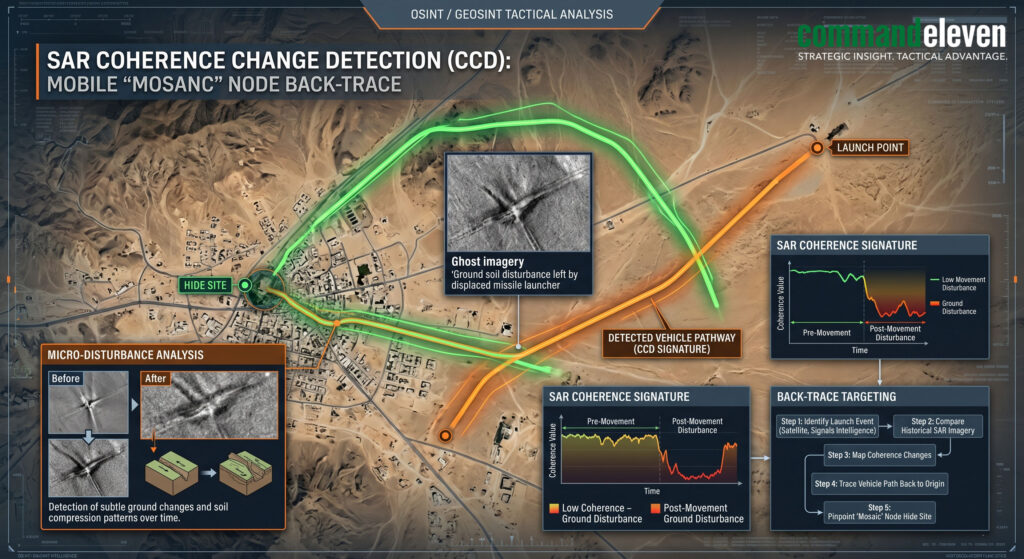
Geospatial SAR Anomaly Detection
We no longer rely on optical satellites, which are negated by the Levant’s weather patterns or Iranian smoke-screening.
- SAR Coherence Change Detection (CCD): By comparing two SAR images taken hours apart, our algorithms identify “Micro-Disturbances” in the soil. This detects where a Khordad-15 launcher was parked, even if it has moved, allowing us to back-trace its “Hide Site.”
- RF Mapping: Scraping unencrypted commercial frequencies to identify localized “Blinks” in cellular density, which often correlate with the arrival of a mobile C2 unit.
Narrative Pre-Positioning as a Kinetic Lead
Adversaries often execute a Cognitive Vector (CI) strike immediately prior to a kinetic one.
- The Bot-Spike Indicator: When bot-networks begin amplifying “Engineered Distrust” regarding a specific U.S. or IDF logistics hub, it is categorized as a Kinetic Precursor. The HTF model automatically cues SAR assets to that location, anticipating a Distributed Strike.
The HUMINT Layer: The “Stay-Behind” Mesh (SBM)
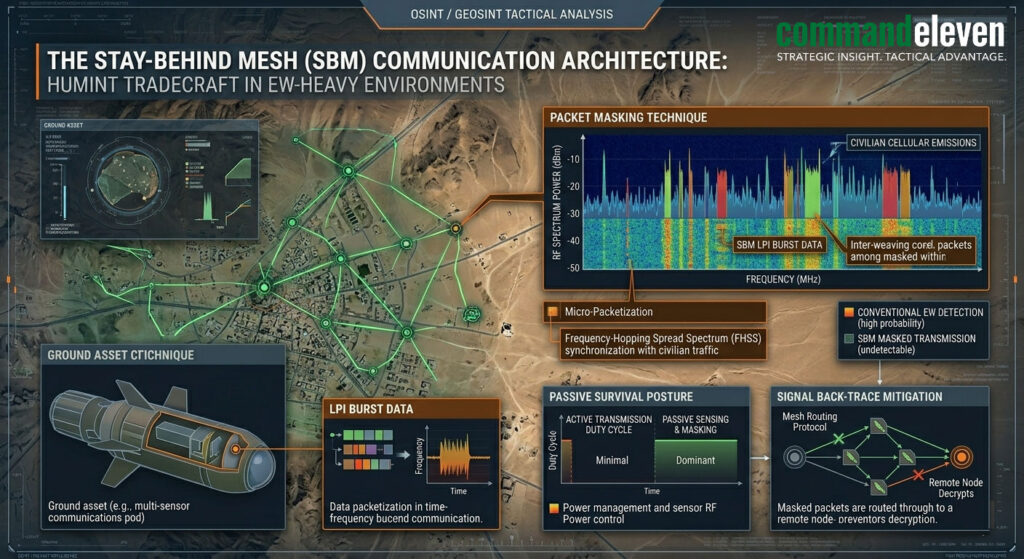
In an era of digital decoys and “Target Noising,” HUMINT is the final arbiter of Ground Truth.
Tradecraft in the “Silent-Listen” Environment
Our SBM nodes operate under a Passive Survival Posture.
- Low-Probability of Intercept (LPI) Comms: SBM assets utilize SDRs (Software-Defined Radios) to transmit 5-millisecond “Burst Data” packets. These are timed to coincide with civilian cellular “pings,” making them invisible to Western-standard SIGINT or adversarial EW.
- The PID Protocol: OSINT can identify a “Launcher-Shaped Object.” The HUMINT node provides Positive Identification (PID) – confirming if the object is a 3D-printed inflatable decoy or a functional kinetic asset.
Battle Damage Assessment (BDA) 2.0
Traditional BDA relies on post-strike satellite imagery. In 2026, the SBM provides Immediate BDA.
- Functional vs. Physical Destruction: A drone may hit a launcher, but if the “Succession Protocol” allows the secondary C2 to take over, the threat remains. Only ground-truth HUMINT can verify the cessation of the “Heartbeat Signal” at the tactical edge.
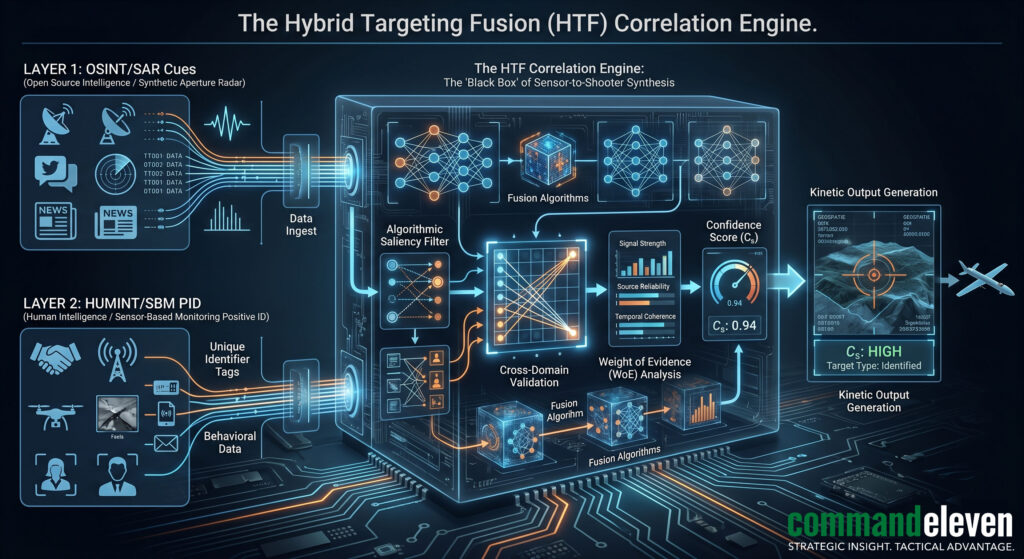
The HTF Model: Integrating the Fusion
The integration of these two disparate vectors occurs within the Technical Hub through a process of Cross-Domain Correlation.
Automated Target Weighting
The HTF engine assigns a Confidence Score (Cs) to every potential target.
- A SAR anomaly alone may yield a Cs of 0.4.
- When cross-referenced with a bot-spike in that sector, Cs rises to 0.6.
- A “Confirm” burst from an SBM node pushes Cs to 0.95, triggering an Automatic Target Suggestion (ATS) to the nearest kinetic asset (e.g., an F-35 or a LUCAS drone).
Countering the “Blink-Mode” Engagement
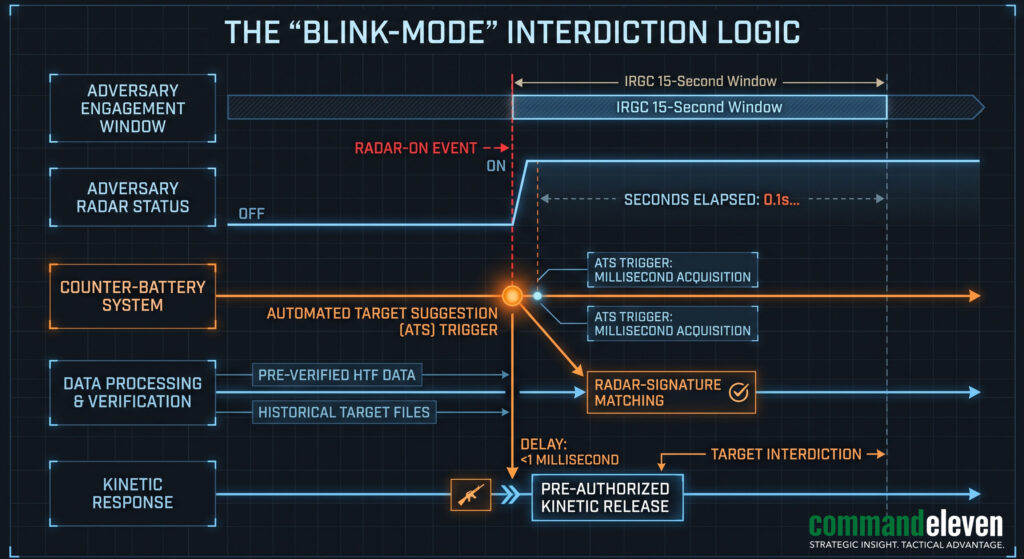
The IRGC’s 15-second window is designed to beat the “Human” decision cycle. The HTF model beats the “Blink” by pre-authorizing strikes on nodes that reach a Cs of 0.9, allowing the kinetic asset to fire the moment the launcher activates its radar.
The Correlation Engine
The HTF model utilizes a “Weight of Evidence” approach:
- Level 1 (OSINT Trigger): An automated SAR scan identifies a mobile launcher signature.
- Level 2 (HUMINT Verification): A localized SBM node provides an encrypted “Confirm” signal via the mesh-network.
- Level 3 (Kinetic Execution): Targeting coordinates are fed directly into the PGM (Precision-Guided Munition) or the LUCAS OWA drone interface.
Targeting Efficiency: This fusion reduces the SSL from the legacy 4-hour window to a clinical 12-minute window, essential for countering the IRGC’s 15-second “Blink-mode” engagement window.
Implementation: The 180-Day Intelligence Hardening

For institutional clients, integrating into the HTF mesh is a three-phase process:
- Sensor Integration (Days 1–60): Linking corporate CCTV and OSINT feeds into the UTM.
- Protocol Training (Days 61–120): Training security personnel on the “Heartbeat” and OOB verification.
- Active Mesh Participation (Days 121–180): Transitioning to a “Live” BDA posture where the client’s own data helps refine the regional Cs.
Operationalizing Mission Command in Intelligence
Real-time targeting requires the decentralization of the “Decide” phase of the OODA loop.
- Decentralized Authorization: Targeting officers at the tactical edge are empowered to execute strikes based on the HTF “Confirm” signal without waiting for HQ sign-off.
- The 72/48 Hardening Context: In the 72 hours leading up to a “Flash-Dark” or kinetic surge, the HTF model shifts to its “Aggressive Capture” state, increasing the frequency of SAR scans and SBM heartbeat signals.
Conclusion: The Clinical Edge
In 2026, air superiority and maritime dominance are secondary to Information Superiority. The side that can fuse OSINT and HUMINT with the highest velocity and lowest latency controls the kinetic outcome. CommandEleven’s HTF model is the blueprint for moving beyond the “Fog of War” and into the “Clinical Strike” era.
CommandEleven Red Team Assessment: We anticipate that the first major “HTF-led” neutralization of an Axis “Triple Lock” node will occur in the Southern Red Sea corridor by early May. Institutional clients must ensure their logistics fleets are integrated into the Unified Threat Matrix (UTM) to benefit from this real-time targeting buffer.