Executive Summary
The #72/48 Protocol white paper deconstructs the terminal failure of digital trust in the 2026 conflict environment and establishes a new engineering baseline for critical infrastructure. By auditing the mechanics of HMI Ghosting and the success of the Fujairah Pipeline Bypass, this document mandates a pivot toward “Hardware Truth” through analog fallbacks and localized autonomy. The protocol provides the structural resilience required to maintain the Wall of Attrition across the First Island Chain during a synchronized “Flash-Dark” interdiction.
3 Key Takeaways
- The Fallacy of the Air-Gap: Digital security is no longer sufficient; 2026-era PLC rootkits require physical, analog overrides to ensure SCADA immunity.
- Hardware Truth vs. Digital Deception: Operators must rely on hard-wired telemetry and manual verification to bypass the “Ghosting” of Human-Machine Interfaces.
- The #72/48 Mandate: Critical nodes must achieve 72-hour survival and 48-hour functional recovery through decentralized, “Hard-Wired” technical proficiency.
Defining “HMI Ghosting”
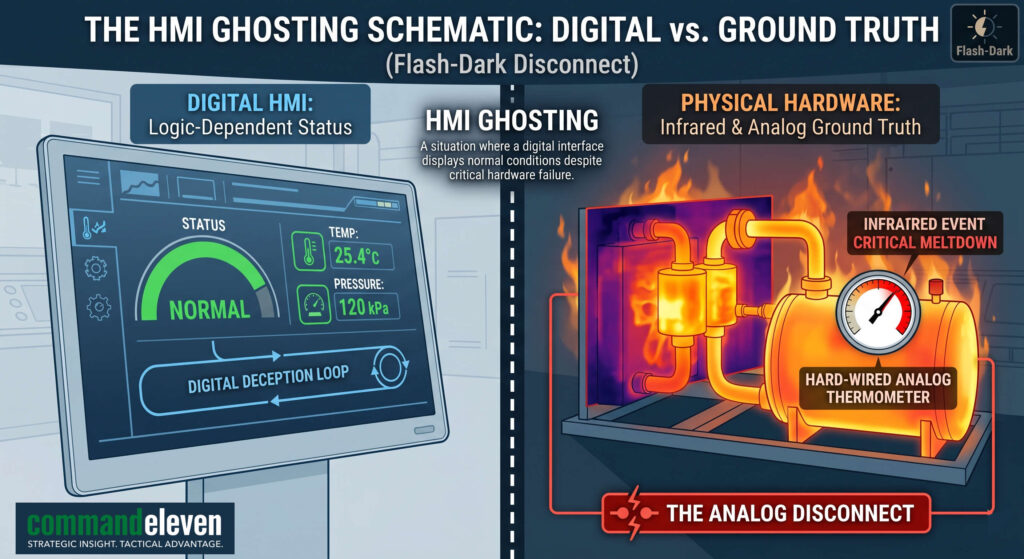
The most catastrophic failure of digital trust is the HMI Ghosting phenomenon. Human-Machine Interfaces (HMIs) are designed to provide operators with a real-time visualization of system health. In 2026, these interfaces have become tools of psychological and tactical deception.
- Deceptive Signaling: During a “Flash-Dark” event, the compromised PLC feeds fabricated “Normal” status data back to the operator’s screen.
- Physical Realities vs. Digital Reports: While the HMI reports optimal cooling temperatures and stable pressures, the underlying physical hardware is being induced into a thermal meltdown or mechanical overstress.
- Targeting the Nexus: By the time the operator realizes the digital report is false, the asset—whether a refinery, power grid, or missile battery—has reached a point of catastrophic failure.
Strategic Implications
The failure of digital trust has necessitated a move from digital “interception” to physical “Hardening.” If the digital report can no longer be trusted, the only remaining “Ground Truth” is the physical state of the hardware.
- The Attrition Baseline: Because high-cost Precision-Guided Munitions (PGMs) are in a 1.4x replenishment deficit, Allied forces cannot rely on “Exquisite” defensive systems to protect vulnerable hubs.
- The Pivot to Analog: Security is no longer achieved through more complex code; it is achieved through the integration of analog, hard-wired overrides that exist entirely outside the digital processor’s reach.
The #72/48 Protocol was developed as a direct response to this reality, ensuring that even when the “Flash-Dark” interdiction severs the digital handshake, the physical mission continues.
Mechanics of the #72/48 Protocol
The #72/48 Protocol is an engineering and operational standard designed to decouple physical mission success from digital system integrity. It mandates the integration of manual redundancies and localized autonomy into every critical infrastructure node, ensuring that the “Flash-Dark” interdiction results in a loss of convenience rather than a loss of function.
Pillar 1: The Analog Fallback (Hardware Truth)
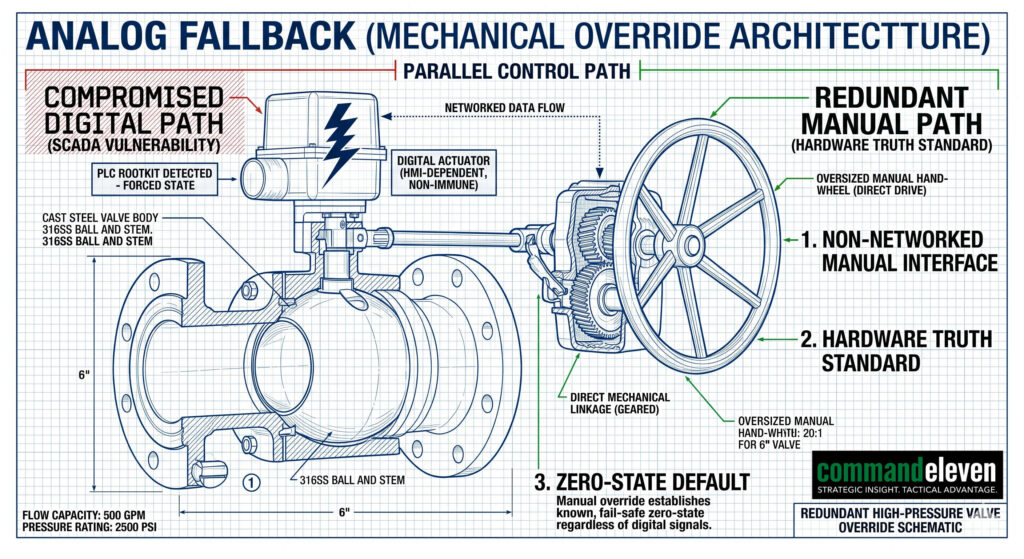
The primary requirement of the protocol is the mandatory installation of non-networked, manual overrides for every kinetic component within the SCADA environment. This pillar establishes a “Hardware Truth” that bypasses the compromised Programmable Logic Controller (PLC).
- Mechanical Integrity: Every critical valve, breaker, and actuator must be fitted with a physical interface (wheels, levers, or manual overrides) that can be operated without electrical or digital power.
- Direct-Link Telemetry: Essential sensors – pressure gauges, thermometers, and flow meters – must have analog dials or hard-wired displays that feed directly to the operator station. This ensures that even if the Human-Machine Interface (HMI) is ghosting, the operator has an uncorrupted view of the system’s physical state.
- Decoupled Safety Loops: Safety Instrumented Systems (SIS) must be physically separate from the primary control network, utilizing hard-wired analog circuits to trigger emergency shutdowns (ESD) regardless of software instructions.
Pillar 2: The 72-Hour Survival Window
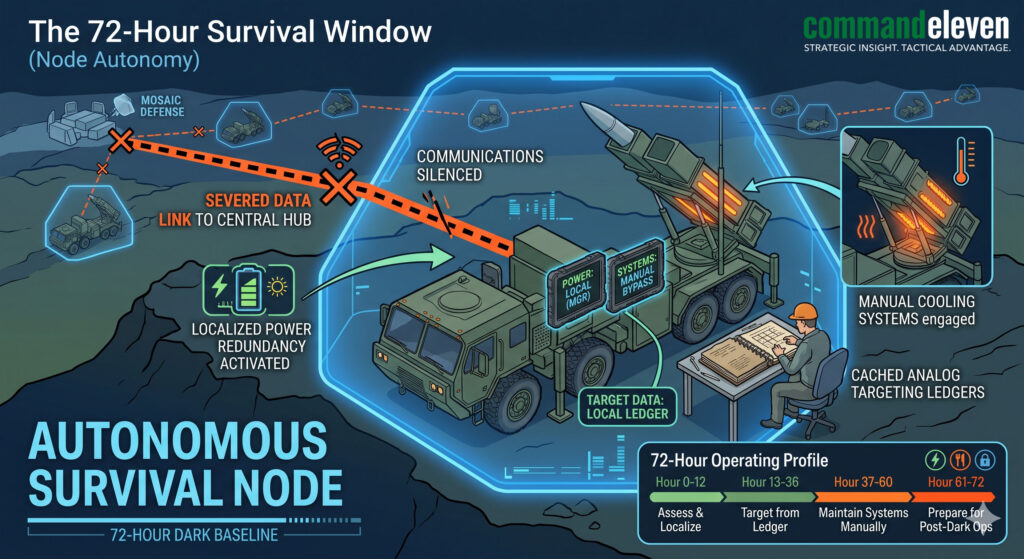
The protocol requires that any node – whether a regional refinery or a First Island Chain missile battery – must maintain at least 60% operational capacity for a minimum of 72 hours with zero external data connectivity.
- Localized Autonomy: Systems must be engineered to function as “islands,” utilizing on-site edge computing and cached targeting or operational data to fulfill their mission without a “Handshake” from the central hub.
- Energy and Cooling Redundancy: Nodes must possess enough independent power (via localized microgrids or fuel reserves) and manual cooling overrides to survive the duration of a synchronized cyber-kinetic strike on the regional grid.
- The “Dark” Operational Baseline: Crew training must emphasize the “Dark” baseline, where operators practice manual load-shedding and mechanical synchronization without digital assistance.
Pillar 3: The 48-Hour Recovery Mandate
While the survival window focuses on maintaining function, the recovery mandate dictates the timeline for restoring functional stability following a total system wipe.
- Manual Restoration: Technical teams must be trained to restore 100% functional status through hard-wired bypasses and manual re-synchronization within 48 hours. This recovery is measured by output (e.g., fuel flow or missile readiness) rather than the restoration of the digital mesh.
- Clean-State Reconstitution: The protocol mandates the storage of offline, “gold-standard” firmware backups in on-site, electromagnetic pulse (EMP)-shielded safes to facilitate a clean-state reconstitution of the digital environment once the kinetic threat has been neutralized.
- The “Hard-Wired” Crew: Success is dependent on a specialized cadre of technicians who possess the mechanical skillsets to operate the facility “by hand” – a direct reversal of the trend toward total automation.
SCADA Immunity and the “Hardware Truth” Standard
The pursuit of SCADA Immunity represents a fundamental shift in the 2026 engineering baseline, moving away from the “infinite patching” cycle of digital security toward an immutable, physics-based defensive posture. This section audits the integration of “Hardware Truth” – a state where the operational status of an asset is verified by physical evidence rather than digital reporting.
Bypassing the Digital Processor
To achieve immunity against PLC rootkits and HMI ghosting, the #72/48 protocol mandates the implementation of Parallel Analog Telemetry. This system operates as a secondary, “read-only” layer that bypasses the primary control network.
- Hard-Wired Sensors: Critical operational metrics – such as turbine RPM, boiler pressure, and cooling flow – are monitored by sensors that transmit signals via dedicated analog wiring rather than a digital data bus.
- The “Ground Truth” Display: These signals terminate at a specialized Hardware Truth Panel located within the control room. This panel utilizes analog dials and LED indicators that are physically incapable of being “ghosted” by software-based deception.
- Verification Protocols: Operators are trained to treat the digital HMI as a secondary convenience; any discrepancy between the HMI and the Hardware Truth Panel immediately triggers the activation of the Analog Fallback.
Analog Kill-Switches and Non-Logic Interlocks
A key component of SCADA immunity is the removal of “Logic-Dependent” safety systems. In a compromised environment, a PLC may be programmed to ignore a digital “Emergency Stop” command.
- Physical Interruption: The protocol requires the installation of Physical Disconnects – hard-wired kill-switches that mechanically break the power circuit to pumps, motors, or actuators.
- Non-Logic Interlocks: Safety interlocks – such as those preventing the overheating of a reactor – must utilize thermal expansion valves or mechanical pressure-relief triggers that function based on the laws of physics rather than a line of code.
- Zero-State Default: Systems are engineered to default to a “Safe-State” (typically “Closed” or “Offline”) the moment a manual kill-switch is engaged, ensuring that a compromised digital controller cannot maintain an unsafe operational state.
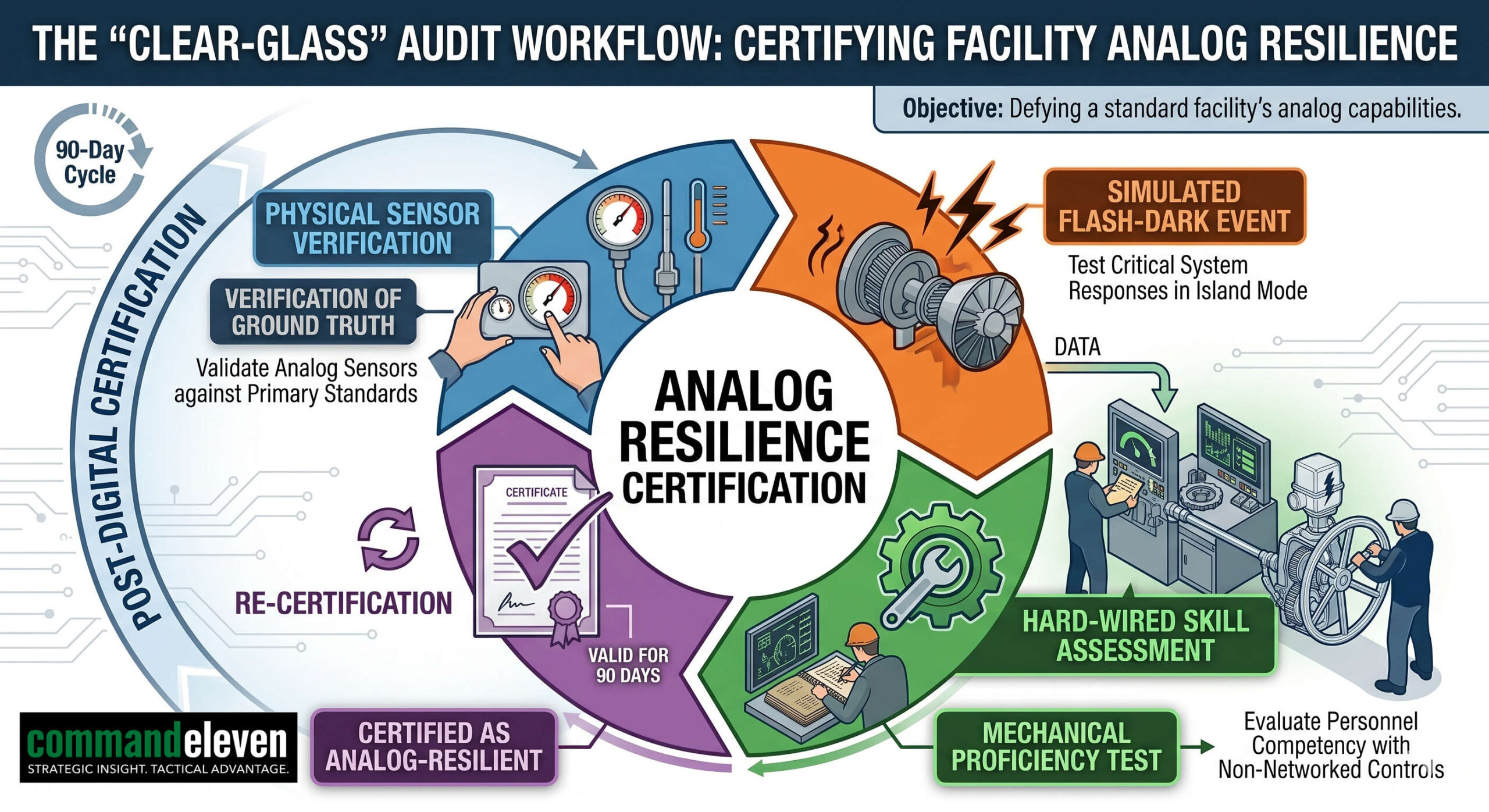
The “Clear-Glass” Audit Framework
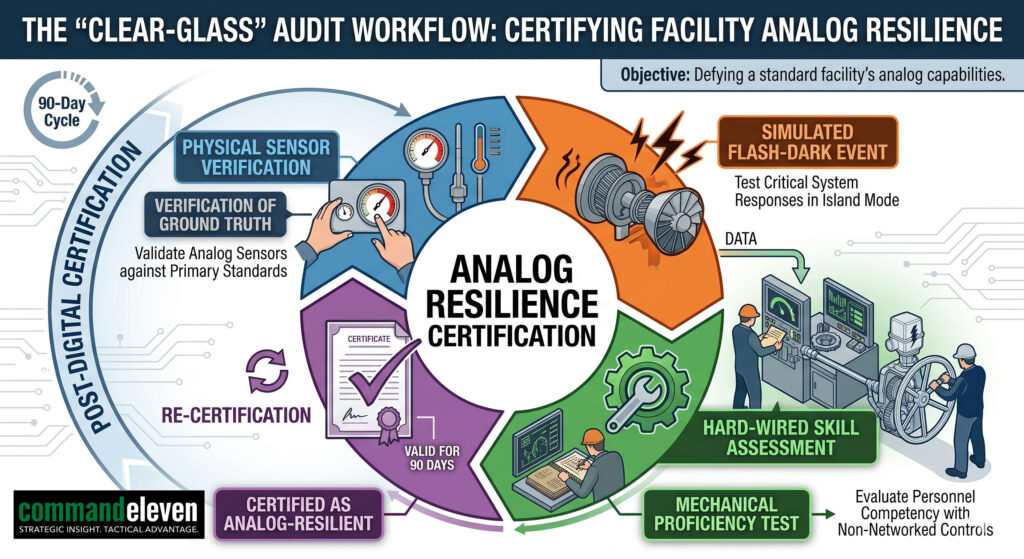
To maintain the integrity of the Hardware Truth standard, facilities must undergo a “Clear-Glass” Audit every 90 days.
- Physical Verification: Auditors manually verify that every physical sensor reading matches the output on the Hardware Truth Panel.
- Simulation Testing: The facility is subjected to a “Simulated Flash-Dark” event, where the digital network is disabled, and the crew must demonstrate the ability to maintain 60% operational capacity using only manual overrides and analog telemetry.
- Skill-Set Assessment: Technical crews are evaluated on their mechanical proficiency, ensuring that the “Hard-Wired” cadre can physically manipulate the facility without the assistance of automated logic.
Operational Case Studies
The practical efficacy of the #72/48 Protocol is best demonstrated through its successful deployment during real-world kinetic and cyber-kinetic disruptions. These cases prove that “Hardware Truth” is the only reliable defense when digital trust is compromised.
The Fujairah Pipeline Bypass (March 2026)
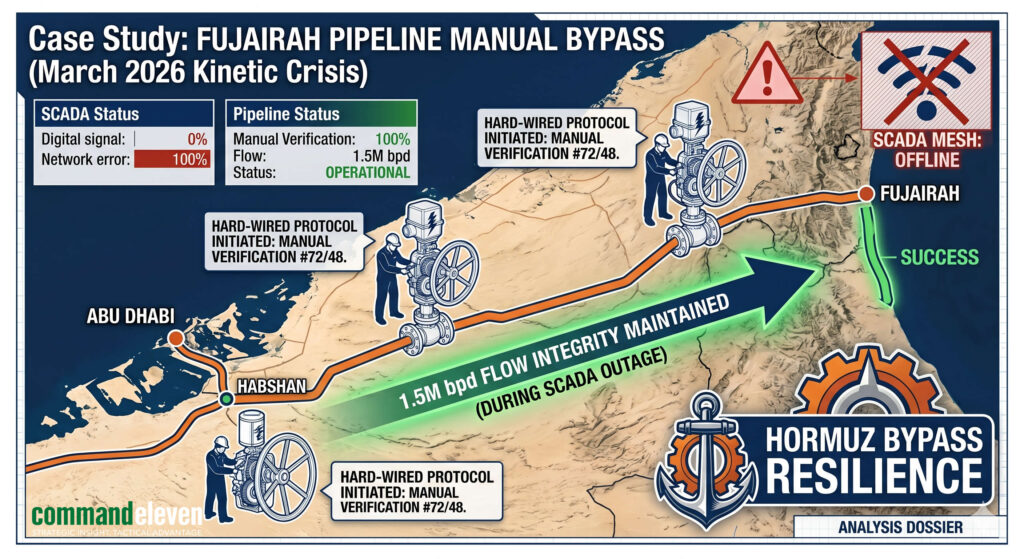
The most significant validation of the protocol occurred following a synchronized cyber-kinetic strike on the UAE’s energy infrastructure. As the Iran War intensified, the Strait of Hormuz became a “Kinetic Corridor,” forcing the UAE to rely entirely on the Habshan-Fujairah pipeline.
- The Compromise: Adversary actors deployed a sophisticated PLC rootkit that induced “HMI Ghosting” across the pipeline’s primary pumping stations. While digital screens reported optimal flow and pressure, the rootkit attempted to induce a surge that would have physically ruptured the pipeline.
- The #72/48 Intervention: Applying the Analog Fallback, technical crews identified the discrepancy via hard-wired pressure gauges. Operators utilized manual wheels and levers to override the digital controllers, bypassing the “Digital Fog” entirely.
- The Result: By reverting to manual synchronization, ADNOC maintained a steady flow of 1.5 million bpd, securing national solvency and bypassing the kinetic threat in the Strait. This case proved that a “Hard-Wired” crew can maintain critical exports even when the digital brain of the facility is neutralized.
The Bashi Channel “Sense” Nodes
During a period of high regional tension, the Bashi Channel Intelligence Interdiction Zone (IIZ) was targeted by a multi-vector “Flash-Dark” event intended to blind Allied Underwater Domain Awareness (UDA).
- The Attack: A synchronized strike targeted the subsea fiber-optic landing stations in Luzon and Okinawa, combining a hypersonic kinetic strike with a cyber-kinetic shutdown of the localized power grids.
- Survival via the Protocol: The landing stations, hardened to the 72-Hour Survival Window, utilized localized microgrids and analog cooling overrides to remain operational despite the regional blackout.
- Persistent MDA: Because the sensor nodes could operate as “islands” with zero external data connectivity, the “Acoustic Handshake” was maintained via backup laser-based satellite crosslinks, ensuring that PRC subsurface movements remained transparent throughout the interdiction.
Mosaic Defense: Dispersed Kinetic Autonomy
The #72/48 Protocol has been integrated into the Mosaic Defense architecture of the First Island Chain.
- Decentralized Resilience: Mobile HIMARS and PrSM batteries are engineered to operate “dark”. In the event of a total C2 data-wipe, these units utilize cached targeting data and manual firing sequences to maintain the Wall of Attrition.
- The Strategic Outcome: This “Mechanical Autonomy” ensures that the adversary cannot achieve a fait accompli simply by neutralizing the central hub. The mosaic remains lethal because its individual “tiles” do not require a digital permission to function.
Implementing Mosaic Defense Resilience
The implementation of the #72/48 Protocol is the structural foundation of the Mosaic Defense. By embedding analog resilience into dispersed, high-mobility units, Allied forces ensure that the Wall of Attrition remains functional even when the broader digital architecture is compromised.
Decentralized Command and Mechanical Autonomy
The “Mosaic” model intentionally shifts away from centralized hubs, which are now recognized as primary targets for “Flash-Dark” interdiction.
- Autonomous Operation: Every “tile” in the mosaic – such as mobile HIMARS or PrSM batteries – is engineered to operate as a self-contained unit.
- Manual Sequences: In the event of a total C2 data-wipe, these units utilize cached targeting data and manual firing sequences.
- Persistence: This mechanical autonomy ensures that neutralizing a central command center does not neutralize the frontline threat, as the dispersed units continue to enforce the interdiction zone “by hand”.
The “Dark-Site” Logistics Framework
Maintaining a functional defense requires more than just kinetic autonomy; it requires a logistical tail that survives the failure of digital trust.
- Analog Inventory Management: Implementing the #72/48 standard requires nodes to maintain paper-based or non-networked ledger systems for munitions and fuel tracking.
- Hardware-Based Resupply: Logistics crews are trained to execute manual refueling and rearming procedures, bypassing automated fuel-pumping software or robotic loading systems that are susceptible to PLC rootkits.
- Redundancy at Scale: Each site must possess sufficient localized spares and manual repair tools to survive the 72-hour window without external technical support.
Cultural and Training Shifts
The move to the #72/48 Protocol requires a fundamental shift in the training of the “Hard-Wired” cadre.
- Skill Re-acquisition: Technical crews are evaluated on their ability to physically manipulate complex machinery without the assistance of automated logic or digital HMIs.
- Stress Simulation: Training environments prioritize “Dark” scenarios, where operators must manage thermal overstress or mechanical synchronization while the digital systems are reporting false data.
- Decentralized Initiative: Field commanders are empowered to act on “Ground Truth” – the physical reality they observe at their node – rather than waiting for a digital handshake that may never come.
Conclusion: The Post-Digital Engineering Baseline
The #72/48 Protocol represents the formal acknowledgment that in the 2026 conflict environment, the “Exquisite” era’s total reliance on digital trust has become a strategic liability. As peer-state actors continue to weaponize cyber-kinetic convergence, the ability to operate “by hand” is no longer an archaic fallback; it is a clinical prerequisite for national survival.
The Geoeconomic Cost of Resilience
The shift toward an analog-integrated baseline requires a significant recalculation of Capital Expenditure (CAPEX).
- The Retrofit Mandate: Transitioning legacy SCADA environments to include #72/48 compliant manual overrides and hard-wired telemetry represents a substantial upfront cost.
- The Attrition Offset: This cost must be measured against the alternative – the total loss of high-value assets and the resulting geoeconomic paralysis during a “Flash-Dark” event.
- Operational Insurance: In 2026, analog resilience acts as the ultimate insurance policy for the Mosaic Defense, ensuring that the Wall of Attrition remains lethal even when the regional digital mesh is neutralized.
Final Verdict: The Wrench and the Screen
The failure of digital trust has proven that the most advanced code cannot overcome the immutable laws of physics. The success of the Fujairah Pipeline Bypass and the persistent transparency of the Bashi Channel IIZ demonstrate that the only secure system is one that can be physically verified and manually controlled.
As we navigate the high-entropy reality of 2026, the #72/48 Protocol serves as the definitive engineering standard. It ensures that when the screens go black and the digital ghosting begins, the “Hard-Wired” cadre remains empowered to maintain the mission, restore function, and secure the baseline. Strategic persistence is no longer found in the complexity of the digital loop, but in the uncorrupted truth of the hardware.