Executive Summary
The Bashi Corridor serves as the technical “Sentinel” for the Wall of Attrition within the First Island Chain. This assessment audits the high-fidelity Intelligence Interdiction Zone (IIZ) established through the clandestine “Sense-Share-Contribute” framework. By integrating Underwater Domain Awareness (UDA) and the multi-national “Acoustic Handshake,” Allied forces have achieved subsurface transparency that negates the PRC’s “Quiet” submarine advantages. However, the report identifies critical fragilities in centralized data-fusion hubs susceptible to “Flash-Dark” interdiction and the emergence of a “Surveillance Void” in the Sulu-Celebes Seas, currently being exploited by hybridized non-state actors like ASG and ISEA.
3 Key Takeaways
- The Acoustic Handshake: The transition from siloed national intelligence to a horizontal, real-time sharing architecture between Tokyo, Taipei, and Manila has reduced the targeting window to a sub-15 minute SSL.
- Centralized Fragility: The reliance on high-density data-fusion hubs creates a “single point of failure” for cyber-kinetic Flash-Dark strikes, requiring an immediate move toward decentralized edge-computing.
- The Southern Leak: The hyper-focus on the Bashi IIZ has inadvertently created a low-resolution “Surveillance Void” in the south, enabling the hybridization of regional terror groups mimicking state-level Grey Zone tactics.
High-Fidelity Intelligence Interdiction Zones (IIZ)
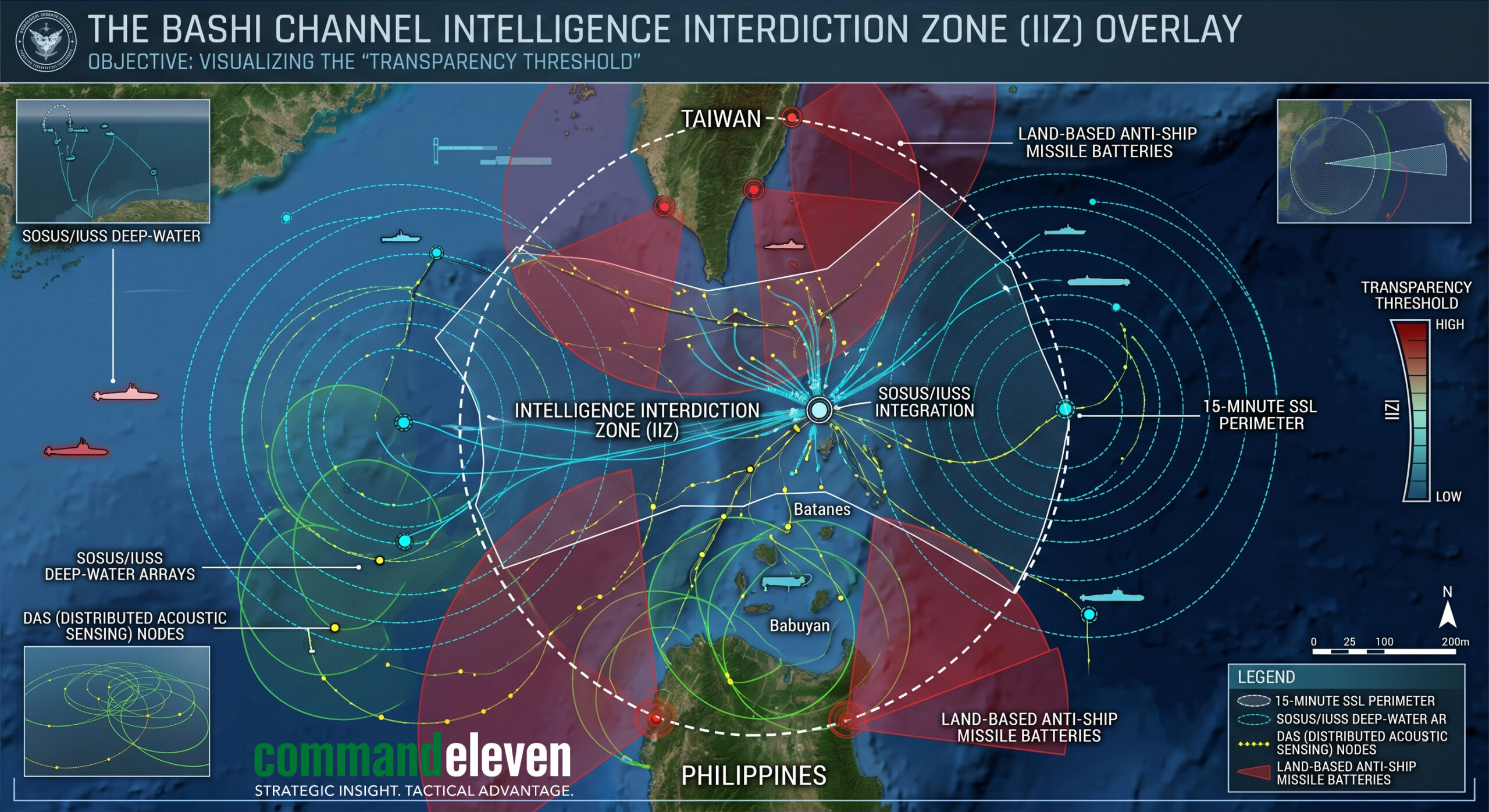
In the 2026 battlespace, the concept of “surveillance” has been superseded by the Intelligence Interdiction Zone (IIZ). An IIZ is defined as a geographically defined theater where sensory density – across acoustic, electronic, and multi-spectral domains – reaches a “Transparency Threshold.” In these zones, the objective is not merely to observe, but to achieve a Confidence Score (Cs) high enough to trigger a kinetic coordinate within the 15-minute Sensor-to-Shooter Latency (SSL) window.
The Transparent Battlespace
The Bashi Corridor IIZ negates the traditional advantage of “Grey Zone” stealth. By saturating the channel with overlapping sensor grids, Allied forces remove the adversary’s ability to move undetected. This is the “Hyper-Integrated” battlespace, where AI-driven correlation engines manage over 1,000 simultaneous tracks, filtering civilian noise to expose kinetic intent.
Global Parallels and Precedents
To understand the efficacy of the Bashi IIZ, one must examine its doctrinal predecessors:
- The GIUK Gap (Cold War): The original template for undersea interdiction. The U.S. and UK utilized the Greenland-Iceland-UK gap to trap Soviet submarines using the legacy SOSUS arrays.
- The Strait of Hormuz (2024-2025): The evolution of drone-noising. The IRGC-QF attempted to “noise” the strait with thousands of small craft; Western forces responded with “Blink-mode” detection, identifying high-threat vectors within the swarm.
- The Bashi Channel (2026): Unlike its predecessors, the Bashi IIZ is a “Multi-Domain Plug.” It does not just track submarines; it correlates subsurface acoustics with SAR (Synthetic Aperture Radar) and SIGINT to identify “Shadow” militia vessels attempting to mask PLAN egress.
The Clandestine “Sense-Share-Contribute” Framework
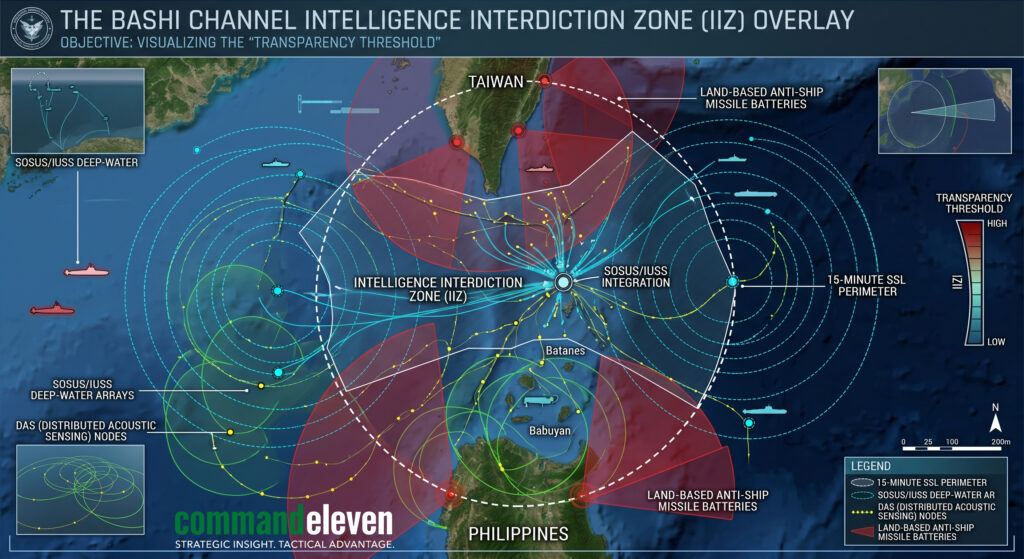
The success of the Bashi IIZ relies on a radical departure from legacy intelligence protocols. The 2026 “Sense-Share-Contribute” framework was born out of the catastrophic latency failures of the early 2020s.
The Legacy Failure: “Siloed Intelligence”
Prior to 2026, Allied intelligence operated under a “Vertical” model. Information gathered by a Japanese submarine or a U.S. P-8 Poseidon was filtered through national classification offices and diplomatic channels. This created a 48-to-72 hour latency. In a conflict where PRC “Flash-Invasion” protocols operate on a 6-to-12 hour window, siloed intelligence was functionally useless. It provided a “History of the Battle” rather than a “Targeting Solution.”
The 2026 Shift: Horizontal Integration
The current framework is built on three horizontal pillars designed for machine-speed synchronization:
- Sense: Thousands of autonomous nodes – ranging from Distributed Acoustic Sensing (DAS) cables on the seabed to loitering ISR drones – feed raw, un-vetted data directly into a shared regional mesh.
- Share: National classification boundaries are bypassed for “Operational Handshake” partners (Taipei, Tokyo, Manila, Washington). The data is accessible in real-time, allowing a Philippine missile battery to see the same “Target Suggestion” as a Japanese destroyer.
- Contribute: Each partner adds a unique, localized vector that the others cannot provide:
- Manila provides the littoral HUMINT and “Stay-Behind” eyes-on-target.
- Taipei provides the high-density coastal SIGINT and “Blink-Mode” radar.
- Tokyo provides the deep-water acoustic hydrophones and high-altitude satellite relay.
The Rationale for Clandestine Execution
This framework remains clandestine to protect the “Acoustic Handshake” signatures. If the specific frequencies and correlation algorithms used to identify PLAN SSNs were exposed, the PRC could engineer “Acoustic Decoys” to noise the IIZ. By maintaining a clandestine “Sense-Share-Contribute” architecture, the Allies ensure that the Bashi Corridor remains a digital noose that the adversary cannot see until they have already been assigned a Cs.
Underwater Domain Awareness (UDA) – The New Frontline
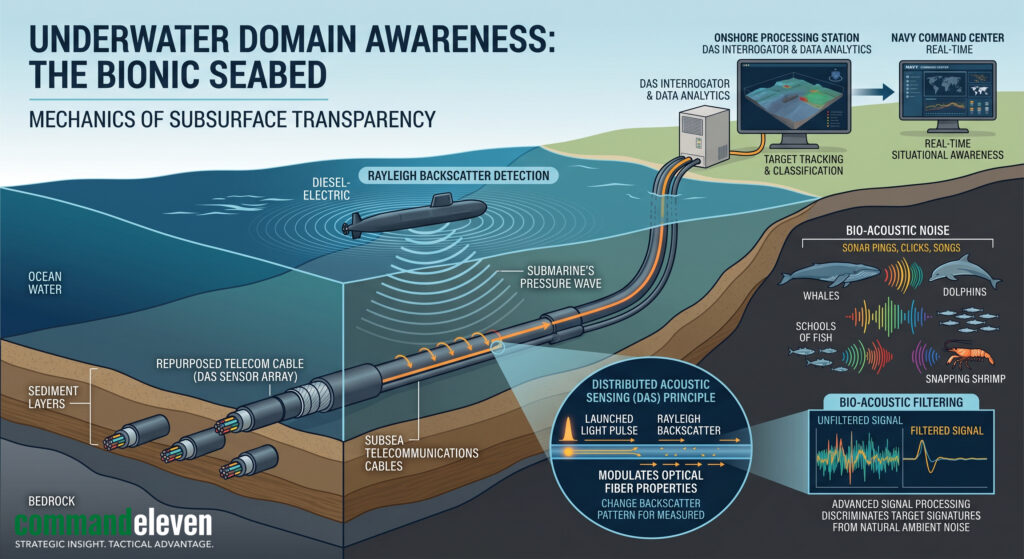
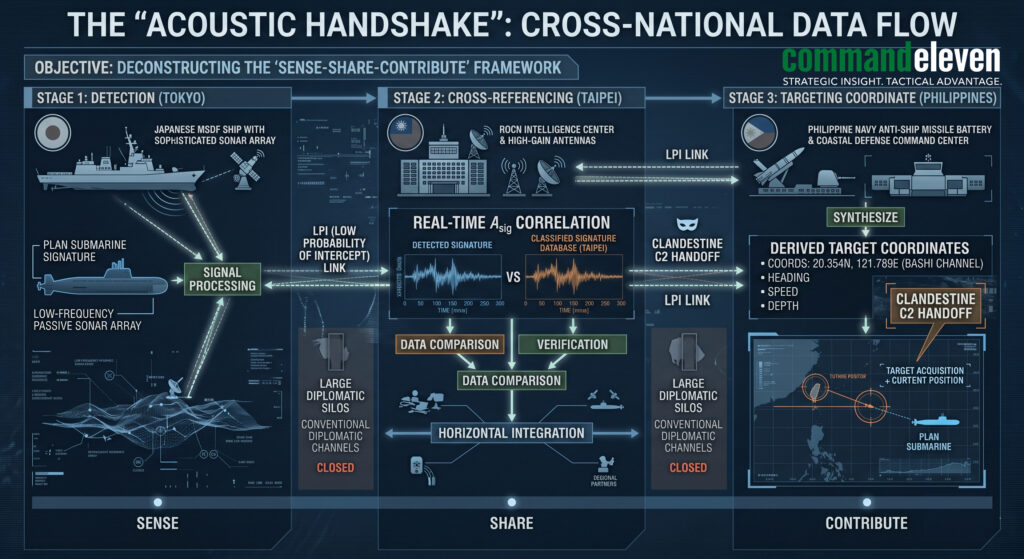
In the legacy era of maritime warfare, the subsurface was treated as a “blind domain,” where detection was periodic and reliant on the proximity of a high-end acoustic platform. In 2026, this has been replaced by Underwater Domain Awareness (UDA). UDA is defined as the total, persistent transparency of the subsurface environment – an “unblinking eye” that operates from the seabed to the surface.
Defining the UDA Architecture
UDA is not a single sensor but a multi-layered ecosystem. It integrates physical, biological, and digital data to create a real-time map of every object moving through the Bashi Corridor. For the Allied “Handshake” partners, UDA provides the “Ground Truth” required to neutralize the PRC’s quietest assets.
- The Bionic Seabed: The foundation of UDA is the repurposing of existing subsea telecommunications cables into Distributed Acoustic Sensing (DAS) arrays. By injecting laser pulses into these fiber-optic cables and measuring the minute “backscatter” caused by the pressure waves of a passing submarine, the seabed itself becomes a continuous, thousands-of-miles-long hydrophone.
- Thermocline Mapping: Submarines historically utilized “shadow zones” – layers of water with varying temperatures and salinity that refract sonar waves – to hide from surface detection. Modern UDA nodes utilize autonomous gliders that constantly “profile” the water column, feeding real-time thermocline data into the correlation engine. This allows the HTF (Hybrid Targeting Fusion) to “see through” the refraction.
Acoustic Fingerprinting (Asig) and Bio-Acoustics
The primary challenge of UDA is the sheer volume of “Noise” in the Bashi Channel, ranging from seismic activity to massive biological migrations.
- AI-Driven Filtering: The UDA system utilizes neural networks to filter out biological noise (e.g., snapping shrimp or whale vocalizations). Once the “natural” noise is stripped away, the system isolates mechanical signatures.
- The Asig Match: Every PLAN vessel has a unique Acoustic Fingerprint (Asig). This includes the specific frequency of its gearbox, the “blade rate” of its propeller, and even the unique flow of water over its hull. When a signature is detected, it is cross-referenced against the shared database. If a match is found, the target is instantly promoted from “Unidentified” to a Kinetic Coordinate.
Tracking the “Quiet” Threat: SSNs and UUVs
UDA is specifically tuned to detect the PRC’s newer, quieter platforms, such as the Type 093B SSN and autonomous gliders.
- Wake Detection: Even if a submarine is “acoustically silent,” it still displaces water. UDA nodes utilize high-frequency active pings to detect the “Turbulent Wake” left behind by a passing hull—a physical signature that cannot be masked by traditional stealth coatings.
- Magnetic Anomaly Detection (MAD): Dispersed drone swarms equipped with miniaturized MAD sensors patrol the upper layers of the Bashi Channel, detecting the minute distortions in the Earth’s magnetic field caused by a large metallic hull.
Strategic Utility: The Subsurface “Plug”
By establishing UDA in the Bashi Channel, the Allies have effectively “plugged” the primary egress point for the PLAN. A submarine can no longer hope to “slip through” the First Island Chain unnoticed. Within the UDA environment, the subsurface is no longer a sanctuary for the adversary; it is a high-risk corridor where every turn is tracked, correlated, and assigned a Cs.
Architecture Fragility – The “Flash-Dark” Interdiction
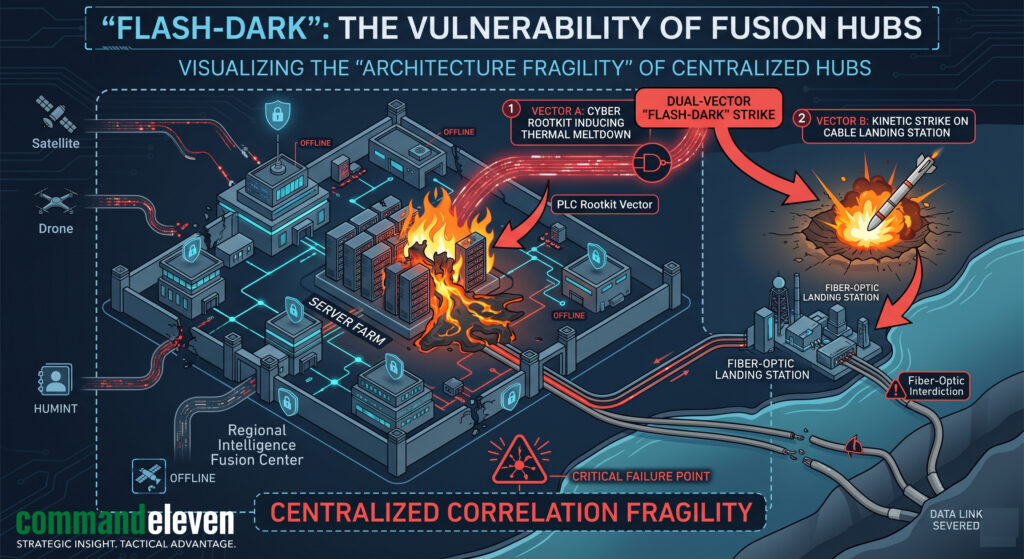
While the “Sense-Share-Contribute” framework and UDA (Underwater Domain Awareness) provide an unprecedented level of transparency, they have introduced a systemic vulnerability: Centralized Correlation Fragility. The efficiency of the Bashi IIZ relies on high-density data-fusion hubs where disparate sensor streams are synthesized into a single targeting solution. In the 2026 battlespace, these hubs have become the primary targets for “Flash-Dark” cyber-kinetic interdiction.
The Vulnerability of the Nexus
Despite the dispersal of the “Sense” nodes (drones, hydrophones, and littoral eyes), the “Share” and “Contribute” functions remain dependent on a limited number of high-capacity processing centers located in Okinawa, Luzon, and Taipei. These hubs are the “brains” of the Acoustic Handshake. If these centers are compromised, the Allied forces are blinded – not because the sensors are dead, but because the data can no longer be correlated.
The “Flash-Dark” Threat Profile
A “Flash-Dark” event is a synchronized, multi-vector strike designed to sever the Bashi digital noose in the opening minutes of a conflict. It utilizes two primary vectors:
- The Cyber Vector (HMI and PLC Sabotage):
- Adversary groups have moved beyond simple data theft to Industrial Control System (ICS) sabotage.
- PLC Rootkits: By targeting the Programmable Logic Controllers (PLCs) that manage the industrial cooling systems of these massive server farms, the adversary can induce a physical thermal meltdown.
- HMI Ghosting: As analyzed in our Cyber-Kinetic Convergence article, operators may see “Normal” operating parameters on their Human-Machine Interface (HMI) while the hardware is being physically destroyed.
- The Kinetic Vector (Cable and Landing Interdiction):
- The Bashi IIZ is physically tethered to the seabed. The landing stations where subsea fiber-optic cables transition to the terrestrial mesh are high-value, static targets.
- Hypersonic Decapitation: A synchronized strike using hypersonic glide vehicles can neutralize these landing stations with such velocity that no “Failover” to satellite links can occur before the PLAN egresses the channel.
The Impact: Reversion to “Siloed Intelligence”
When a “Flash-Dark” event successfully severs the Handshake, the Allied response undergoes a Strategic Degression. Partners are forced to revert to the legacy “Siloed” model.
- Loss of Correlation: Without the fusion hub, a Japanese hydrophone detection cannot be cross-referenced with a Taiwanese SIGINT spike.
- The “Noise” Victory: The adversary wins simply by re-introducing “Noise” into the battlespace. In the darkness of the “Flash-Dark” window, the PRC can execute a “Flash-Invasion” or a mass subsurface egress while the Allies are busy troubleshooting their internal connectivity.
Mitigation: The 72/48 Hardening Protocol
To counter this fragility, CommandEleven advocates for the 72/48 Hardening Protocol specifically for MDA nodes.
- Decentralized Fusion: Moving from large server farms to “Edge-Computing” nodes distributed across the First Island Chain.
- Hardware Truth: Implementing analog, hard-wired kill-switches and manual cooling overrides that cannot be accessed via the digital network.
- Triple-Redundant Handshakes: Establishing non-fiber-optic backup links – such as laser-based satellite crosslinks – that can maintain the “Sense-Share-Contribute” framework even if the subsea cables are severed.
The “Surveillance Void” and Non-State Opportunism
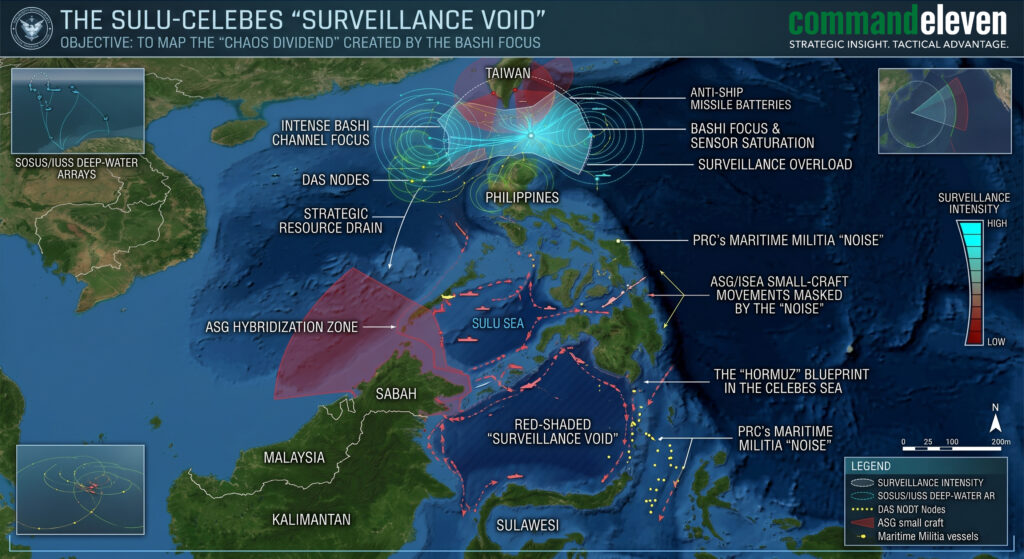
The hyper-fixation on the Bashi Channel Intelligence Interdiction Zone (IIZ) has created a localized “Surveillance Void” in the peripheral archipelagic waters of Southeast Asia. To achieve the 15-minute SSL (Sensor-to-Shooter Latency) required to counter a peer-state adversary, Allied forces have consolidated over 80% of their regional Maritime Domain Awareness (MDA) bandwidth. This resource migration has left the Sulu and Celebes Seas in a state of “strategic darkness,” providing a high-entropy environment for non-state actors to hybridize and expand.
The Resource Drain and the “Dark” Corridor
Monitoring a state-level actor like the PRC requires “High-Resolution” intelligence – satellite persistence, deep-water acoustic arrays, and dedicated SIGINT (Signals Intelligence) hubs. Because these assets are limited, the “Southern Anchor” of the First Island Chain is being held at the expense of archipelagic internal security.
- TNI-AL and Philippine Navy Displacement: As regional navies prioritize the “Kinetic Gates” (Sunda, Lombok, and Bashi), the “Tri-Border Area” between Mindanao, Sabah, and North Kalimantan has become a “Low-Priority” zone.
- The Resulting Void: This area, historically difficult to govern, has regressed into a corridor where non-state movements can occur with minimal risk of state-level interdiction.
ASG and ISEA: The Hybridization Dividend
The Abu Sayyaf Group (ASG) and the Islamic State East Asia (ISEA) are the primary beneficiaries of this “Surveillance Void.” They are no longer operating as isolated jungle insurgents; they are evolving into Maritime Hybrid Threats.
- Utilizing the “Shadow Fleet” Noise: PRC “Shadow” vessels frequently transit near these waters to noise the battlespace. ASG militants are utilizing these larger, non-compliant flotillas as “Radar Shields,” masking their high-speed small-craft movements within the clutter of the maritime militia.
- Technical Acquisition: Intelligence indicates that ASG/ISEA clusters have acquired Commercial Off-The-Shelf (COTS) underwater scooters and LPI (Low Probability of Intercept) communication gear. They are mimicking the “Quiet” transit protocols they observe from state-level actors in the Bashi Channel.
The “Hormuz” Blueprint in the Celebes Sea
We assess with High Confidence that regional terror groups are attempting to replicate the Houthi “Triple Lock” model.
- Localized Interdiction: By utilizing IRGC-provided One-Way Attack (OWA) drones, the ASG is moving to enforce “Localized Tolls” on regional shipping.
- The Strategic Paradox: While Allied “Exquisite” platforms are hunting for high-end PRC submarines in the Bashi Channel, low-cost insurgent drones are threatening the “Soft Underbelly” of the regional supply chain in the Sulu Sea.
The Insurgency-State Symbiosis
There is increasing evidence of a “Symbiotic Opportunism” between Beijing’s Grey Zone actors and regional militants.
- Plausible Deniability Outsourcing: By providing “Passive Intelligence” or hardware to regional insurgent groups, the PRC can trigger a secondary crisis in the Sulu-Celebes Seas. This forces the U.S. and its partners to divert assets away from the Bashi “Plug” to manage a humanitarian or piracy crisis, effectively “un-plugging” the gate through distraction.
Conclusion – Hardening the MDA Perimeter
The Bashi Channel IIZ is a technical masterpiece of 2026 intelligence integration, but it remains a logistical and structural liability. The “Acoustic Handshake” and UDA provide the transparency needed to survive the Strategic Gap, but they do not solve the underlying problem of Resource Depletion.
- Decentralize the Handshake: We must transition from centralized fusion hubs to “Edge-Computing” nodes to survive the “Flash-Dark” threat.
- Close the Void: MDA cannot be a zero-sum game. Allied forces must integrate low-cost, “Attritable” sensor swarms (UAVs and USVs) into the Sulu-Celebes Seas to ensure that the “Gate” in the north does not create a sanctuary in the south.
- Final Assessment: In the Multi-Domain Battlespace, security is only as strong as its quietest corridor. If the West secures the Bashi Channel but loses the Sulu Sea to a hybridized insurgency, the First Island Chain has not been fortified – it has merely been rerouted.