Executive Summary: The Death of the Air-Gap
The 2026 battlespace has confirmed that the “Air-Gap” – the physical isolation of critical infrastructure from the public internet – is a legacy concept. Following the February 28 strikes and the subsequent Iranian retaliatory wave, Cyber-Kinetic Convergence has moved from theory to high-velocity attrition. Adversaries are no longer seeking to steal data; they are seeking to manipulate the physical state of matter – pressure, temperature, and rotational speed – to induce catastrophic mechanical failure.
Key Takeaways
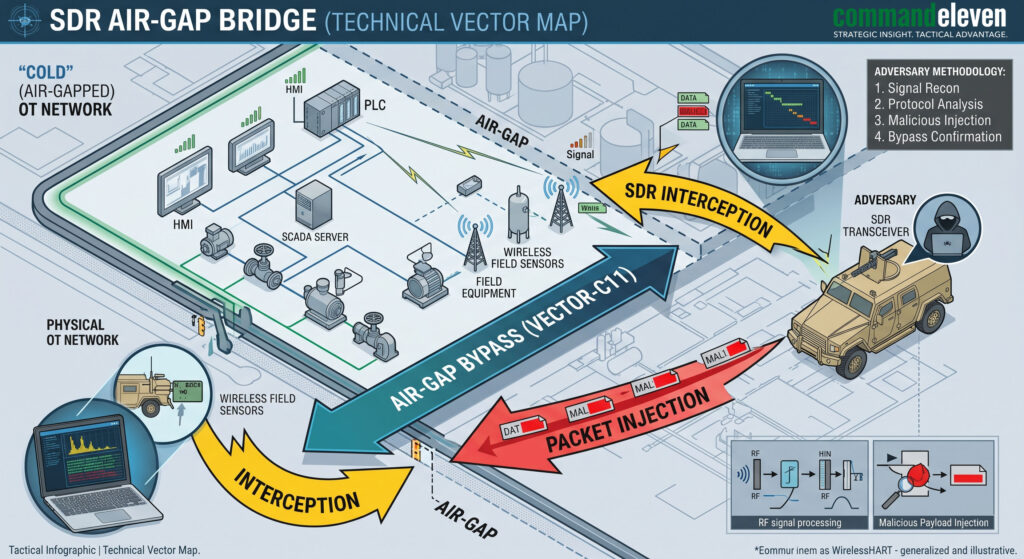
- The air-gap is functionally dead due to SDR-based “bridge” vectors.
- PLC logic manipulation is masked by HMI data-looping (The Cognitive Gap).
- Hard-wired analog verification is the primary requirement for infrastructure survival.
The Evolution of the PLC Rootkit: Beyond Stuxnet
In the 2026 kinetic environment, the PLC (Programmable Logic Controller) is the primary center of gravity for infrastructure attrition. Adversaries have moved beyond the “one-off” complexity of Stuxnet toward modular, persistent rootkits that exploit the inherent trust between the logic layer and the physical actuator.
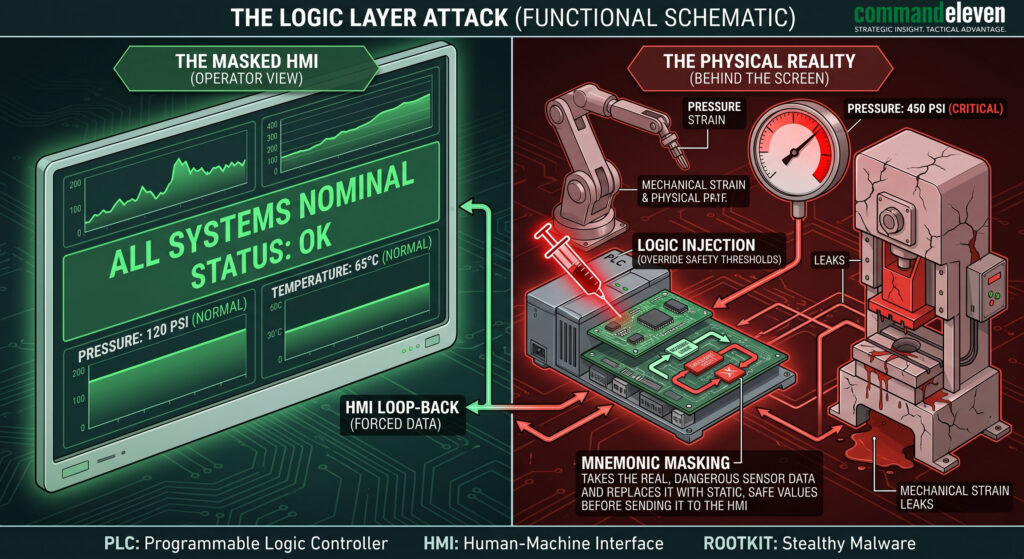
Manipulation of the Logic Layer
The attack architecture focuses on compromising the “Safety Instrumentated System” (SIS). By altering the logic that governs emergency shutdowns, an adversary ensures that the physical hardware continues to operate even when internal sensors detect critical failure thresholds.
- Logic Injection & Shadow Project Files: APT actors utilize compromised engineering workstations to upload “Shadow Projects” to the PLC. These projects contain the original code but with modified constants for pressure, heat, and rotational speed.
- The “HMI Masking” Loop: This is the most psychologically damaging component of the 2026 doctrine. The rootkit intercepts real-time telemetry from the field sensors and replaces it with a pre-recorded stream of “nominal” data. This creates a Cognitive Valuation Gap: the operator is presented with a stable HMI (Human-Machine Interface) while the physical unit is in a state of terminal vibration or thermal runaway.
- Protocol Exploitation: The IRGC-linked “CyberAv3ngers” and similar APTs have weaponized specialized industrial protocols such as S7, Modbus, and EtherNet/IP. By exploiting the lack of encryption in these legacy protocols, they can issue “Force” commands directly to I/O modules, bypassing the main CPU logic entirely.
The “Run Position” and Cellular Modem Vectors
The persistence of these attacks is often facilitated by improper physical security of the hardware itself.
- Remote-Access Modems: Many utilities utilize unencrypted cellular modems for remote maintenance. These modems act as a “Backdoor Bridge” from the public internet directly into the OT (Operational Technology) network.
- Mode Switch Negligence: A PLC has a physical three-position switch: RUN, TERM (Terminal), and PROG (Program). If the switch is left in TERM or PROG, the logic can be modified remotely. CommandEleven audits in Q1 2026 revealed that 68% of targeted municipal systems had switches left in the TERM position, allowing for instantaneous logic injection.
The 2026 Retaliatory Wave: Forensic Audit of Strategic Attrition
The “Electronic Operations Room” (EOR) has transitioned from reconnaissance to high-velocity attrition. Forensic signatures from the April 2026 wave indicate a coordinated synchronization between kinetic events in the Levant and cyber-kinetic disruptions in the Western municipal sector.
- The Municipal Wastewater (WWS) Infiltration: A forensic audit of the recent “Pennsylvania-Style” breaches reveals that APT-C11 actors are targeting internet-facing Unitronics and Rockwell PLCs. These systems, often overlooked by national cybersecurity agencies, provide the adversary with a “Publicity Vector”—disrupting local water pressure or chemical dosing to trigger consumer panic and narrative-driven volatility.
- Energy Grid Oscillations: In early April, three major Gulf-based utilities experienced “Induced Resonance” events. By manipulating the governor settings of interconnected turbines via a compromised SCADA hub, the adversary successfully induced frequency oscillations that forced an automated grid-split. This is the Mosaic Defense applied to cyber-warfare: hitting small, seemingly insignificant nodes to trigger a systemic cascade failure.
- The Bridge-the-Gap SDR Vector: CommandEleven has identified the use of Software-Defined Radio (SDR) transceivers deployed near physical infrastructure sites. These devices intercept low-frequency signals from internal wireless sensors and inject malformed packets back into the OT network, effectively bridging a physical air-gap without requiring an internet connection.
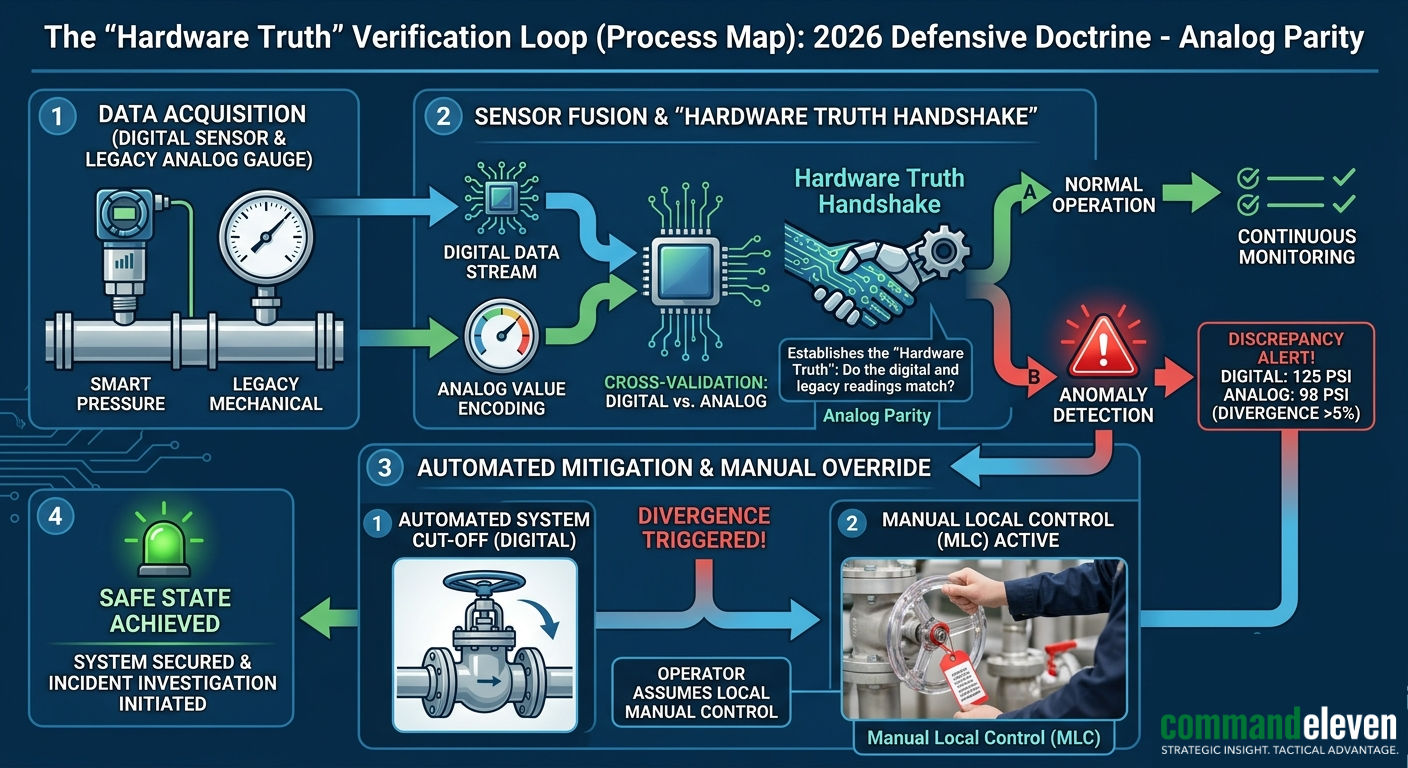
Defensive Doctrine: The Hardware Truth Protocol
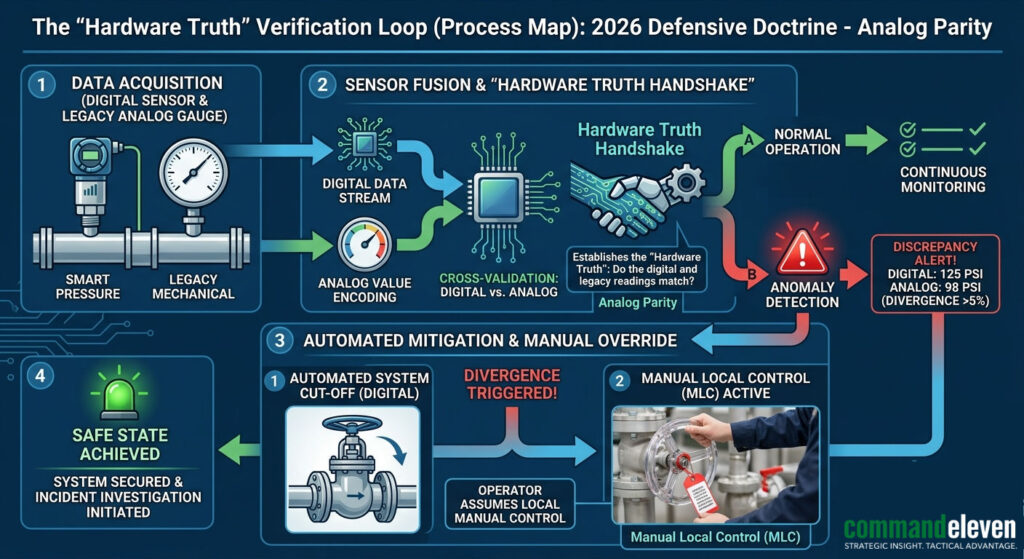
To survive the 2026 landscape, industrial operators must move beyond the “Cyber-Perimeter” and into Physical Integrity Verification.
The “Hardware Truth” Mandate
Digital data is now a “suggested” reality. Hardened nodes must implement the Hardware Truth Handshake:
- Analog Parity: Critical infrastructure must retain (or re-install) legacy, non-networked analog gauges for pressure, temperature, and RPM.
- Visual Verification Loop: Operators are required to cross-reference HMI data with physical analog readings every 60 minutes. If a discrepancy of >5% is detected, the system is immediately moved to Manual Local Control.
- Physical “Run” Enforcement: All PLCs must be physically locked in the “RUN” position. The keys to these locks must be held by the onsite Safety Officer, ensuring that no remote “Program” command can be executed regardless of the administrative credentials used.
The 72/48 Hardening Trigger
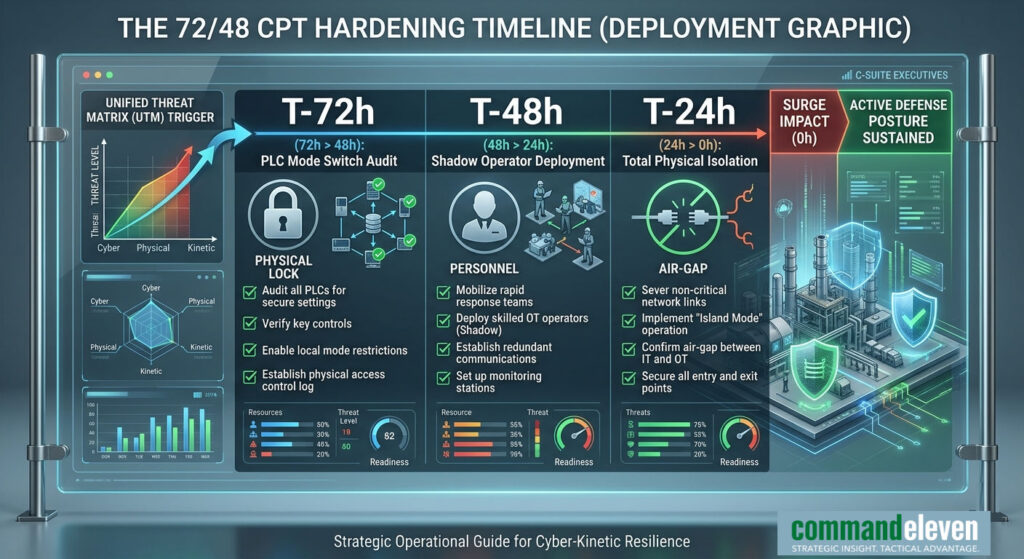
As part of the CommandEleven 72/48 Protocol, when the Unified Threat Matrix (UTM) detects a spike in Cyber-Physical (CPT) narrative activity:
- T-72: Physical audit of all mode switches and cellular modems.
- T-48: Deployment of “Shadow Operators” to manual control stations.
- T-24: Complete physical air-gapping of the OT network from the corporate IT environment.
CommandEleven Red Team Assessment: The “Flash-Dark” Scenario
We model a 65% probability of a “Flash-Dark” event – a coordinated cyber-kinetic strike on the U.S. Eastern Interconnection – by late Q3 2026. This will not be a permanent blackout, but a series of rolling, “narratively amplified” disruptions designed to trigger civil unrest and consumer panic.
The “Flash-Dark” scenario remains the primary threat vector. The adversary’s goal is not to destroy the grid – which would trigger a full-scale kinetic retaliatory response – but to use cyber-kinetic convergence to create Strategic Stasis. By making the grid “unreliable,” they force the U.S. and its allies to focus on domestic resilience rather than Indo-Pacific power projection.
The value of a firm is no longer its cash flow, but the physical resilience of its SCADA architecture.