OPERATIONAL ARCHITECTURE // DIVISION // INTEL
INTELLIGENCE DIVISION //
Home » Services » Intelligence Analysis » Intel Division – Operational Architecture
MANDATE //
The systematic harvesting and synthesis of ground-truth data to eliminate strategic ambiguity.
HUMINT Management //
Oversight of deep-cover assets across the Middle East and South Asia.
Multi-Source Synthesis //
Integration of SIGINT and OSINT to validate field reports.
Pattern Analysis //
Identifying historical echoes in modern conflict precursors.
OPERATIONAL DOCTRINE //
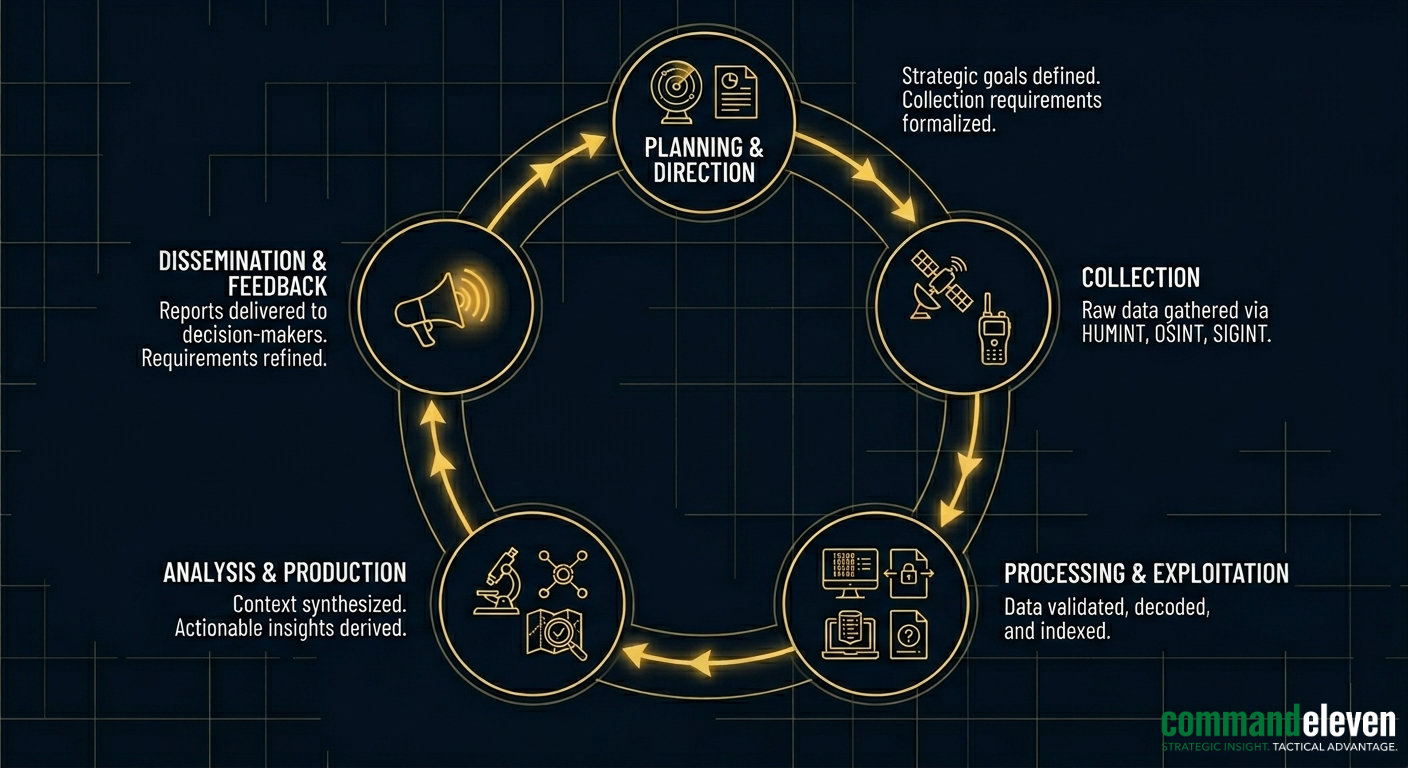
Intelligence Division assets prioritize the Validation Phase. Every data point harvested from the theater is subjected to a “Triple-Node Verification” process—cross-referencing HUMINT with technical signatures to ensure a zero-point margin of error before dissemination.
VALIDATION PROTOCOLS // OVERSIGHT
The Intel Division operates under a Zero-Point Margin of Error mandate.
Every data point harvested from the theater is subjected to the following Triple-Node Verification protocol before it is promoted to the Synthesis phase.
REDUNDANCY SCAN //
Raw HUMINT is cross-referenced against independent field assets within the same operational node. No single-source report is considered verified without a secondary, independent confirmation of the event or intelligence.
TECHNICAL CORRELATION //
Validated HUMINT is overlaid with available technical signatures, including OSINT (Open Source Intelligence) and SIGINT (Signal Intelligence) metadata. This ensures that the human reporting aligns with the digital and technical footprint of the theater.
TEMPORAL AUTHENTICATION //
Reports are analyzed for latency. Data is authenticated by its proximity to the event, ensuring that the information provided is not a legacy narrative but a real-time tactical specification.
OPERATIONAL REACH //

INTELLIGENCE BRIEFS //
The Haqqani/ISKP Technical Handshake
Deep-dive into the logistical and technical symbiosis between the Haqqani Network and ISKP. Analyzing the “Sanitization Gap,” state-grade hardware transfers, and leadership synchronization.
The TTP/ISKP Technical Handshake
A clinical intelligence audit of the Service-Level Agreement (SLA) between the TTP and ISKP. Analyzing hardware integration, thermal optics infusion, and the 18-day radicalization cycle in the Malakand/KP sectors.
The BLA/ISKP Technical Handshake
Analysis of the tactical convergence between BLA and ISKP, focusing on hardware exchange and shared facilitation corridors.
The 45-Day Terminal Window
An analysis of the 45-Day Terminal Window: the critical phase where strategic mobilization transitions into inevitable kinetic action.
The ISKP Wildcard – Intelligence Assessment on Asymmetric Convergence
Clinical audit of ISKP’s integration into the Afghan Triad (Taliban, Al-Qaeda, TTP). Analyzing the tactical multiplicity and shared logistics threatening regional sovereignty.
Counter-Terrorism Enforcement and the Credibility of Intelligence-Led Policing in Pakistan
Analysis of the Counter Terrorism Department’s operations in Pakistan, the implications for intelligence-led policing, and the intersection of extremist content regulation with media oversight.
