Continuation of The ISKP Wildcard Intelligence Assessment
Executive Summary
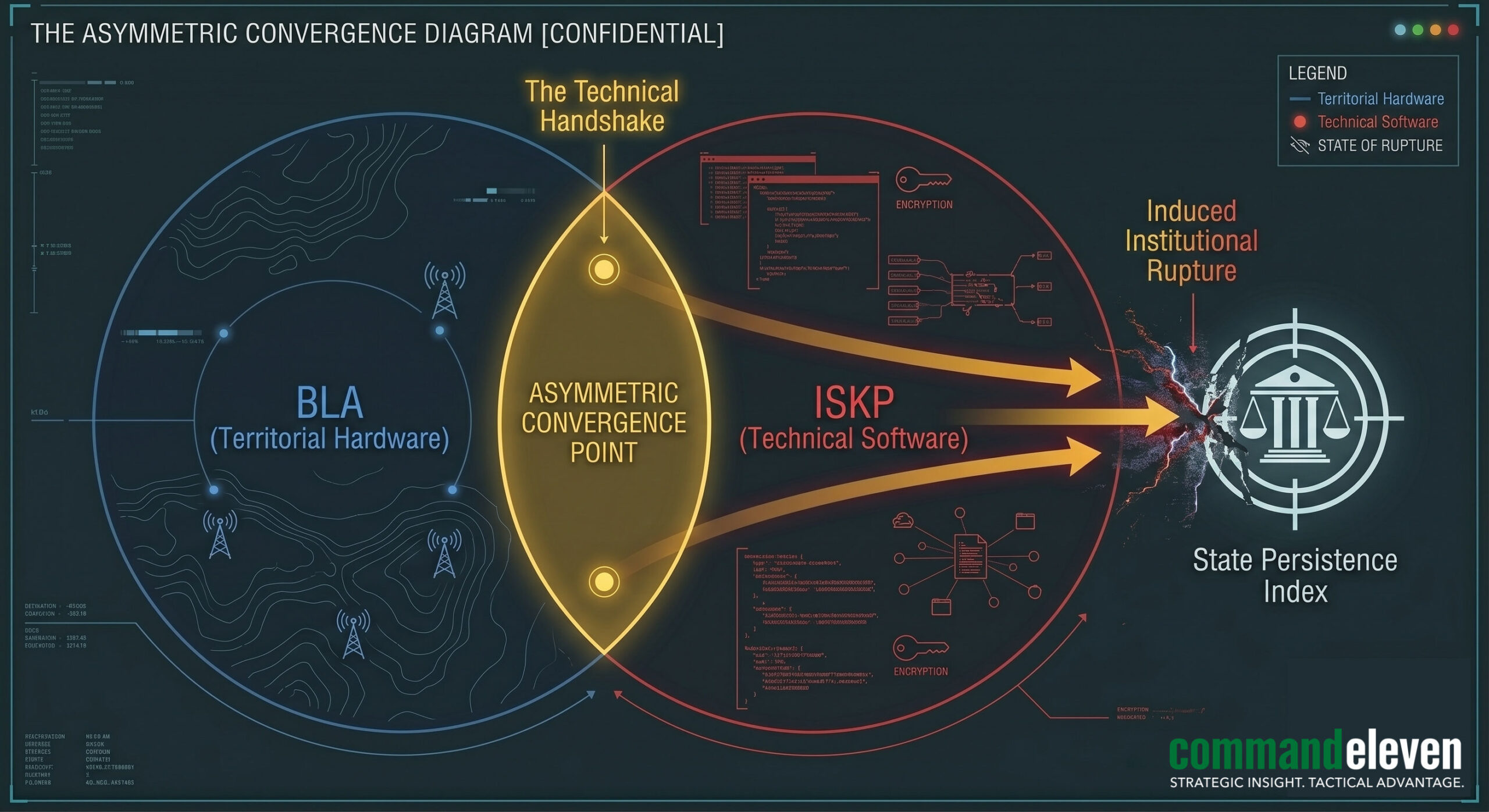
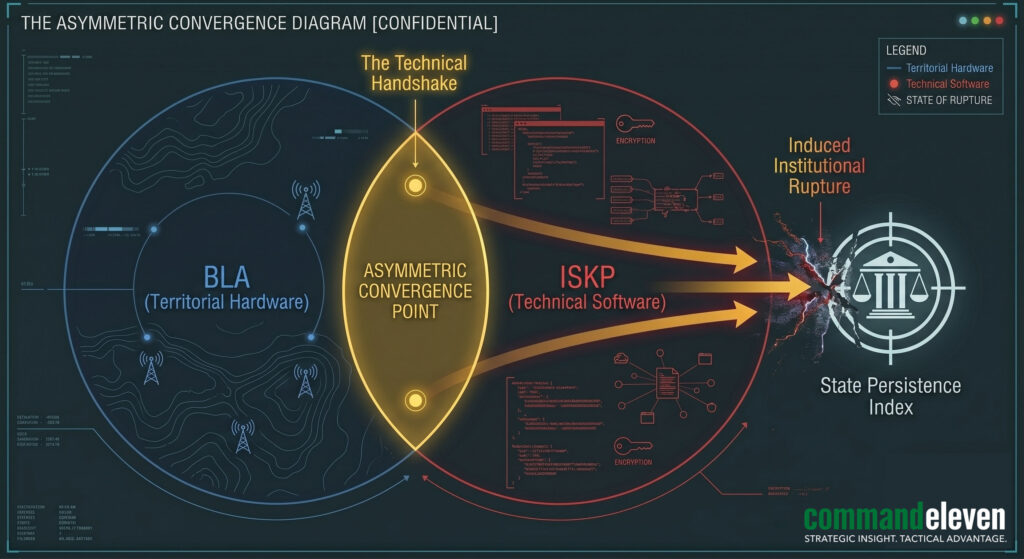
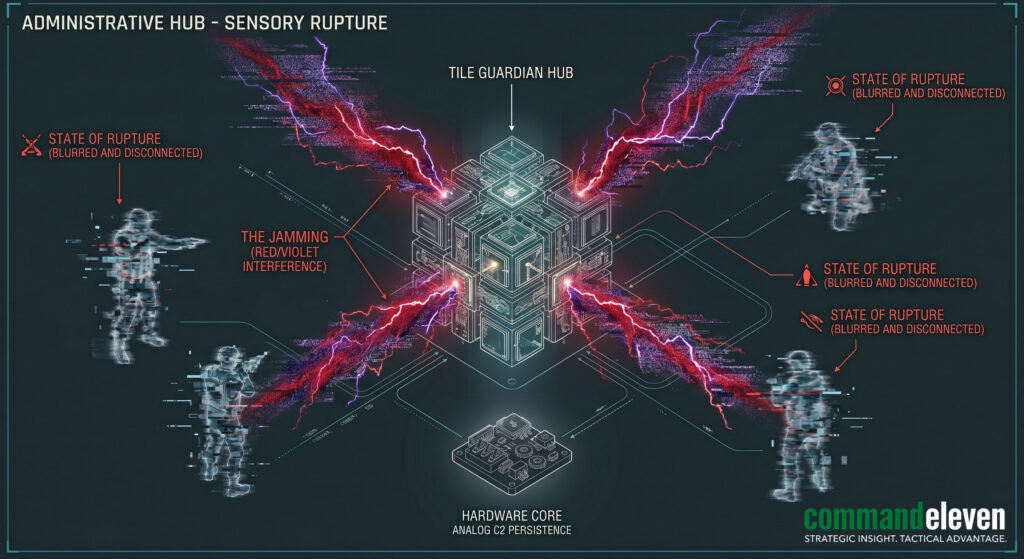
The Intelligence Deep-Dive (C11-2026-IDD-01) deconstructs the mechanical convergence of ethno-nationalist (BLA) and religious-extremist (ISKP) actors. This “Technical Handshake” marks a departure from ideological friction toward a commodified logistical ecosystem. ISKP functions as the high-velocity “Software” provider – delivering encrypted IED triggers, UAV weaponization protocols, and metadata sanitization – while the BLA provides the “Hardware” in the form of geographic safe-passage and local facilitation corridors (N-40/N-5). Recent field data, including a coordinated signal-jamming strike against a kinetic team, confirms that this Triad convergence explicitly targets the state’s Persistence Index (PI) by inducing Sensory Rupture. Neutralizing this threat requires an immediate shift to Analog C2 Hardening and the proactive disruption of these logistical handshake nodes through the Mosaic Defense.
3 Key Takeaways
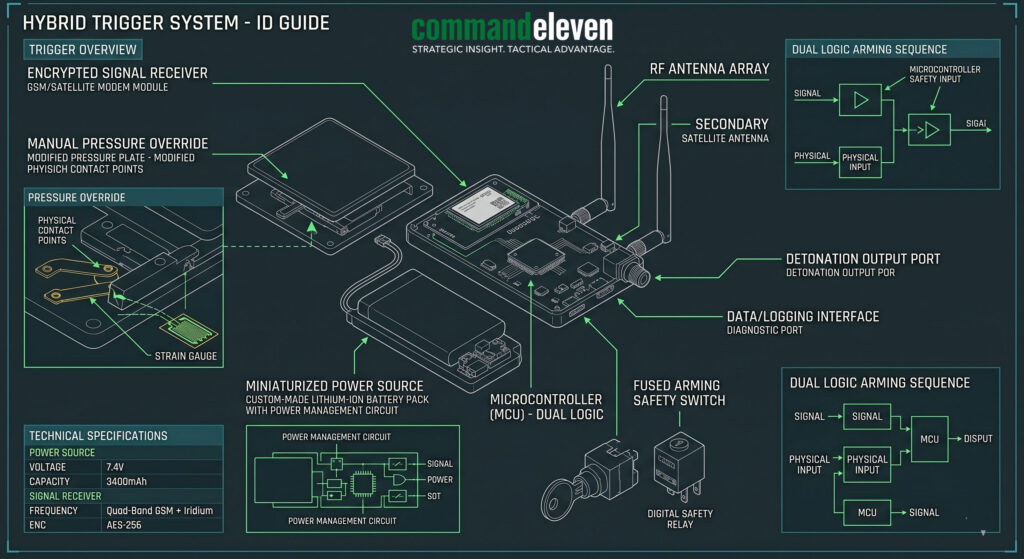
- Technological Force-Multipliers: The BLA has evolved from low-grade sabotage to sophisticated urban maneuvers through the direct infusion of ISKP hardware, specifically hybrid GSM/Pressure IED triggers and portable signal-interdiction systems.
- Corridor Sanitization: Shared nodes in Nushki and Mastung serve as technical exchange points where Afghan-trained ISKP specialists integrate with BLA urban cells, bypassing standard state interdiction.
- The Signal Jamming Threat: The targeting of state communication hubs is a deliberate strategy to force “Flash-Dark” conditions under insurgent control, highlighting the terminal vulnerability of digital-only command structures.
Tactical Facilitation Corridors
The convergence of the BLA and ISKP is not merely an alliance of convenience; it is a geographic necessity predicated on the N-40/N-5 Triangulation. Intelligence audits confirm the establishment of “Sanitized Corridors” where logistics are commodified to ensure regional disruption.
The N-40/N-5 Triangulation
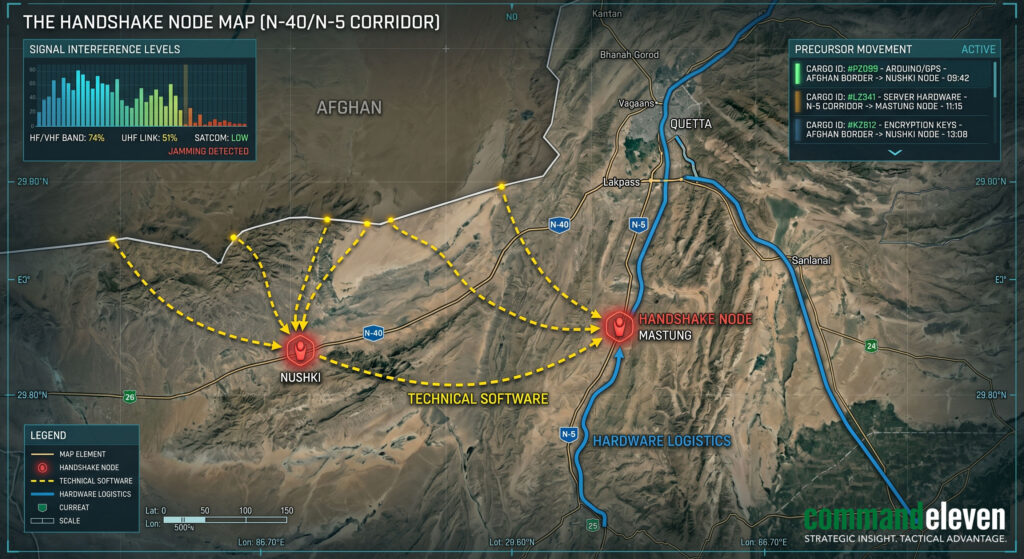
Insurgent logistics rely on the intersection of the N-40 (Quetta-Taftan) and N-5 (Karachi-Peshawar) highways.
- The Handshake Nodes: Specific locations such as Nushki and Mastung serve as the primary “Logistical Handshake” points. Here, ISKP cadres infiltrating from Afghan “Finishing Schools” (specifically from the Spin Boldak and Shorawak sectors) integrate with BLA urban strike cells.
- Corridor Sanitization: The BLA utilizes its deep knowledge of the rugged Balochistan terrain to provide “Hardware” protection – safe houses and manual navigation through mountain passes – for ISKP technical specialists. In return, these corridors are used to move high-grade precursors and encrypted hardware into the southern administrative hubs.
Cross-Border Human Capital Flow
The movement of personnel follows a distinct “Software/Hardware” exchange.
- ISKP Technical Flow: Technical bureaus move from the Nangarhar and Kunar regions into Balochistan via the Chagai-Nushki corridor.
- BLA Logistical Flow: Local BLA cells facilitate the “Last-Mile” delivery of these specialists into urban centers like Quetta and Karachi, where they initiate the Second-Stage Infection of existing radicalization pools.
Hardware Exchange: Advanced IED & Kinetic Systems
The most critical element of the BLA/ISKP Handshake is the physical exchange of “Force Multiplying” technology. This hardware is designed to target the state’s Persistence Index (PI) by inducing maximum institutional rupture.
ISKP Technical Infusion: The Trigger Handshake
Post-blast audits from recent kinetic events in the N-40 corridor reveal a sophisticated technical signature previously unique to ISKP technical bureaus in Afghanistan.
- Hybrid Trigger Systems: The exchange of pressure-plate/GSM hybrid triggers. These systems allow for remote detonation via encrypted mobile signals while maintaining a physical “fail-safe” mechanism, making them highly effective against state convoy jammers.
- Miniaturization of Precursors: ISKP has provided the BLA with the “Software” (chemistry and assembly manuals) to create high-explosive yields from commercially available precursors, effectively bypassing standard state interdiction of military-grade explosives.
UAV & Signal Interdiction Systems
The “Handshake” has extended into the aerial and electronic domains.
- Commercial Drone Weaponization: Intelligence suggests a shared acquisition program for commercial-grade UAVs. ISKP provides the technical “Software” to weaponize these drones with small-diameter payloads, while the BLA provides the “Hardware” (launch sites and local terrain cover) to target Tile Guardian analog C2 points.
- Signal Jamming: The delivery of low-cost, portable signal interdiction hardware used to disrupt the state’s Analog C2 Hubs during a “Flash-Dark” event, attempting to force a total Sensory Rupture.
The “Force Multiplier” Kinetic Doctrine
The BLA has transitioned from traditional low-grade sabotage to high-velocity, coordinated urban maneuvers.
- Synchronized Strikes: The adoption of ISKP’s “Multi-Point” strike doctrine, where a diversionary attack is used to draw state resources away from a primary administrative target.
- Targeting the Persistence Index: The focus has shifted from killing personnel to destroying Hardware Truth anchors – burning manual ledgers, destroying Resource Silos, and assassinating Tile Guardians to prove the state’s administrative fragility.
Software & Cognitive Synchronization
The “Handshake” is not limited to physical payloads; it has evolved into a unified digital ecosystem designed to protect the Triad’s communication and accelerate the “Software Update” (indoctrination) of recruits.
Encrypted Communication Handshakes
Adversaries have moved beyond commercial messaging apps to a customized, decentralized “Shadow Network.”
- Custom Matrix/Session Servers: Intelligence confirms the use of self-hosted, air-gapped Matrix and Session servers located in the Afghan “Finishing Schools.” These servers provide the “Software” infrastructure for BLA and ISKP leadership to coordinate multi-front operations with near-zero metadata footprints.
- Metadata Sanitization: The exchange of technical protocols for “Metadata Sanitization,” ensuring that even if a signal is intercepted, the geographic origin (the Hardware Truth) of the sender remains masked.
Narrative Synchronization: The “Silent Echo” Accelerator
The BLA and ISKP have synchronized their cognitive warfare to induce a regional Sensory Rupture.
- Amplified Grievance: ISKP’s global digital infrastructure is being used to amplify BLA ethno-nationalist grievances. By framing local issues in a global “Resistance” context, they attract a wider pool of recruits from the Madrassa Pipeline.
- Second-Stage Infection: BLA recruitment pools are being “Infected” with ISKP’s high-velocity radicalization software. This has shortened the 45-Day Terminal Window in the south, as recruits are moved through the cognitive phases using ISKP’s optimized digital indoctrination modules.
Operational Interdiction Strategies
Neutralizing the BLA/ISKP Handshake requires a pivot from kinetic pursuit to Logistical De-coupling. We must break the physical and digital bridges that allow these groups to synchronize.
Targeting the “Handshake Nodes”
Utilizing the Mosaic Defense, Tile Guardians must focus on the logistical “Points of Convergence.”
- Logistical Friction Induction: Increasing the Conflict Premium specifically for the Triad. By using Hardware Tokens and Stigmergic Verification for state-vetted trade, we make it mechanically harder and more expensive for “Unvetted” (insurgent) logistics to move along the N-5 and N-40.
- Node Hardening: Deploying localized signal-monitoring teams to detect the specific technical signatures of the BLA/ISKP custom servers. Once a “Handshake Node” (safe house or facilitator) is identified, it is isolated through a localized 72/48 Protocol to prevent data-purging.
Hardware Truth Deep-Audits
Physics-based inspections must focus on the specialized technical components exchanged in the “Handshake.”
- Trigger Interdiction: TGs must train local inspection teams to identify the hybrid GSM/Pressure triggers. These are often disguised as commercial electronics or automotive parts.
- Signal Jamming Counter-Measures: Hardening the Analog C2 Hubs.
- Action: Transitioning to frequency-hopping HF radio and physical wire-line backups for critical Tile-to-Tile handshakes.
- Objective: Ensuring that an ISKP-led signal jam only affects the “Digital Mirage” while the Hardware Truth of state coordination remains persistent.
Exploiting “Software Incompatibility”
The state must induce internal friction between the BLA’s nationalist goals and ISKP’s global objectives.
- Narrative Sabotage: Exposing the “Imperialist” nature of ISKP’s global mandate to BLA cadres. By highlighting how ISKP utilizes BLA fighters as “Disposable Hardware” for global optics, the state can degrade the trust required for the “Handshake.”
- Digital Decoy Ops: Flooding the adversary’s shadow servers with synthetic data to trigger “Institutional Rupture” within their own C2 structure.
Neutralizing the Convergence
The “Technical Handshake” between the BLA and ISKP represents the most significant evolution in regional asymmetric warfare since 2001. By commodifying logistics and technical “Software,” these groups have moved beyond ideological constraints to form a Unified Kinetic Ecosystem.
The Fallacy of the Singular Threat
The 2026 Audit confirms that treating the BLA as a nationalist insurgency and ISKP as a religious-extremist entity is a strategic failure. In the Hardware Truth of the battlespace, they are a singular, networked threat. The BLA provides the terrain and local “Hardware,” while ISKP provides the high-velocity tactical “Software.”
Persistence as the Counter-Measure
Against an adversary that utilizes Tactical Multiplicity, the state cannot rely on kinetic pursuit alone. The only viable counter is the Mosaic Defense.
- Hardening the Analog Core: The recent signal jamming against our kinetic teams proves that digital dependency is a terminal vulnerability. The transition to frequency-hopping Analog C2 and physical, physics-based verification is no longer a doctrinal option; it is an operational mandate.
- Winning the 45-Day Window: By providing superior Logistical Oxygen and economic utility, the state must out-administer the Triad. If the state’s “Hardware” is more persistent and reliable than the insurgent’s “Software,” the community will naturally de-couple from the “Handshake.”
Final Assessment
The BLA/ISKP Handshake is designed to induce Institutional Rupture. It succeeds only when the state retreats into centralized, digital-only silos. By empowering the Tile Guardian and operationalizing the 72/48 Protocol, the state restores the Persistence Index and proves that the “Silent Echo” has no vacancy in a functioning, physics-led administration.