OPERATIONAL ARCHITECTURE // INTEL PROTOCOLS // METHODOLOGY
ANALYTICAL METHODOLOGY & SOURCE VALIDATION //
Home » About CommandEleven » Analytical Methodology
The CommandEleven Engine //
The CommandEleven Engine is a proprietary analytical framework designed to convert raw data into actionable intelligence. To ensure the highest levels of objectivity, every assessment published by CommandEleven is subjected to a rigorous evaluation process based on the Admiralty Code. This dual-metric system rates both the reliability of the source and the credibility of the information provided.
THE INTELLIGENCE ENGINE //
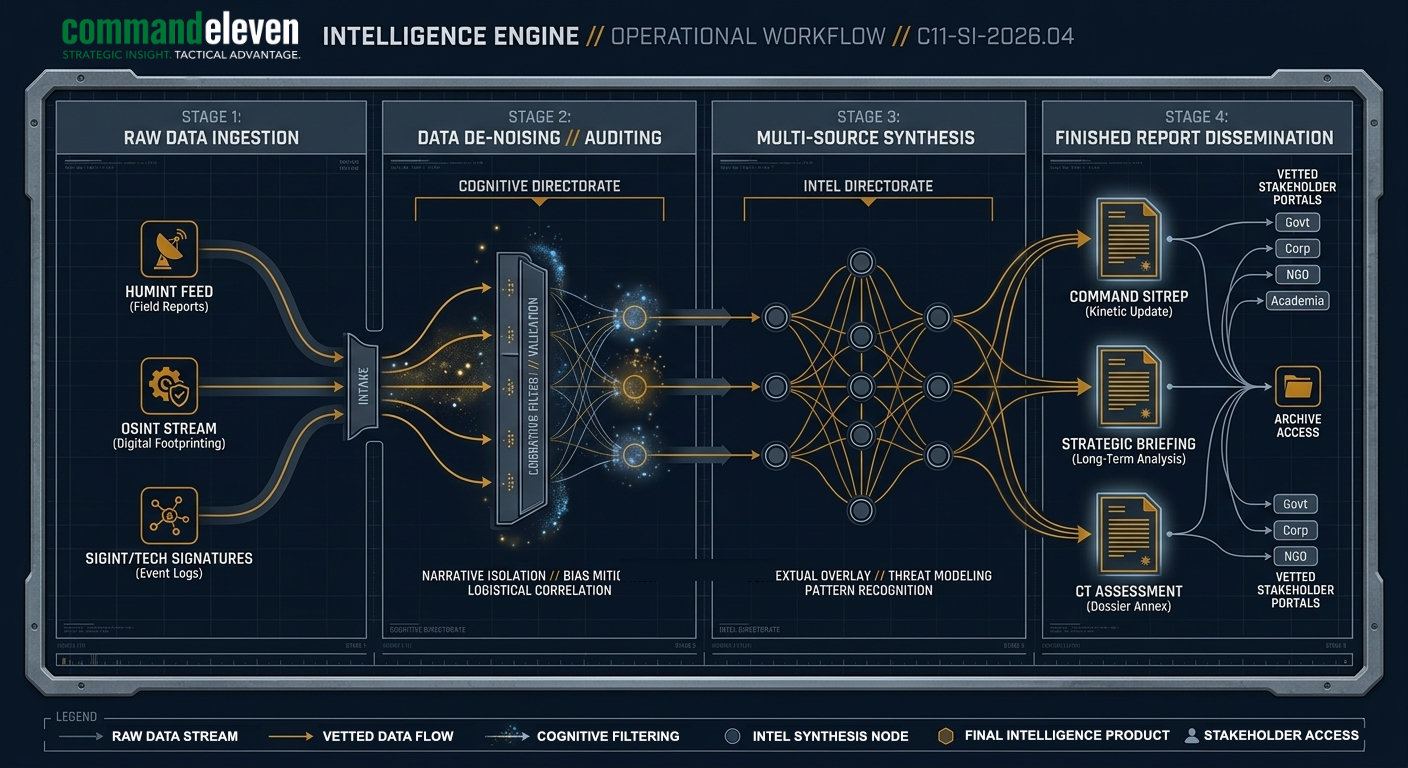
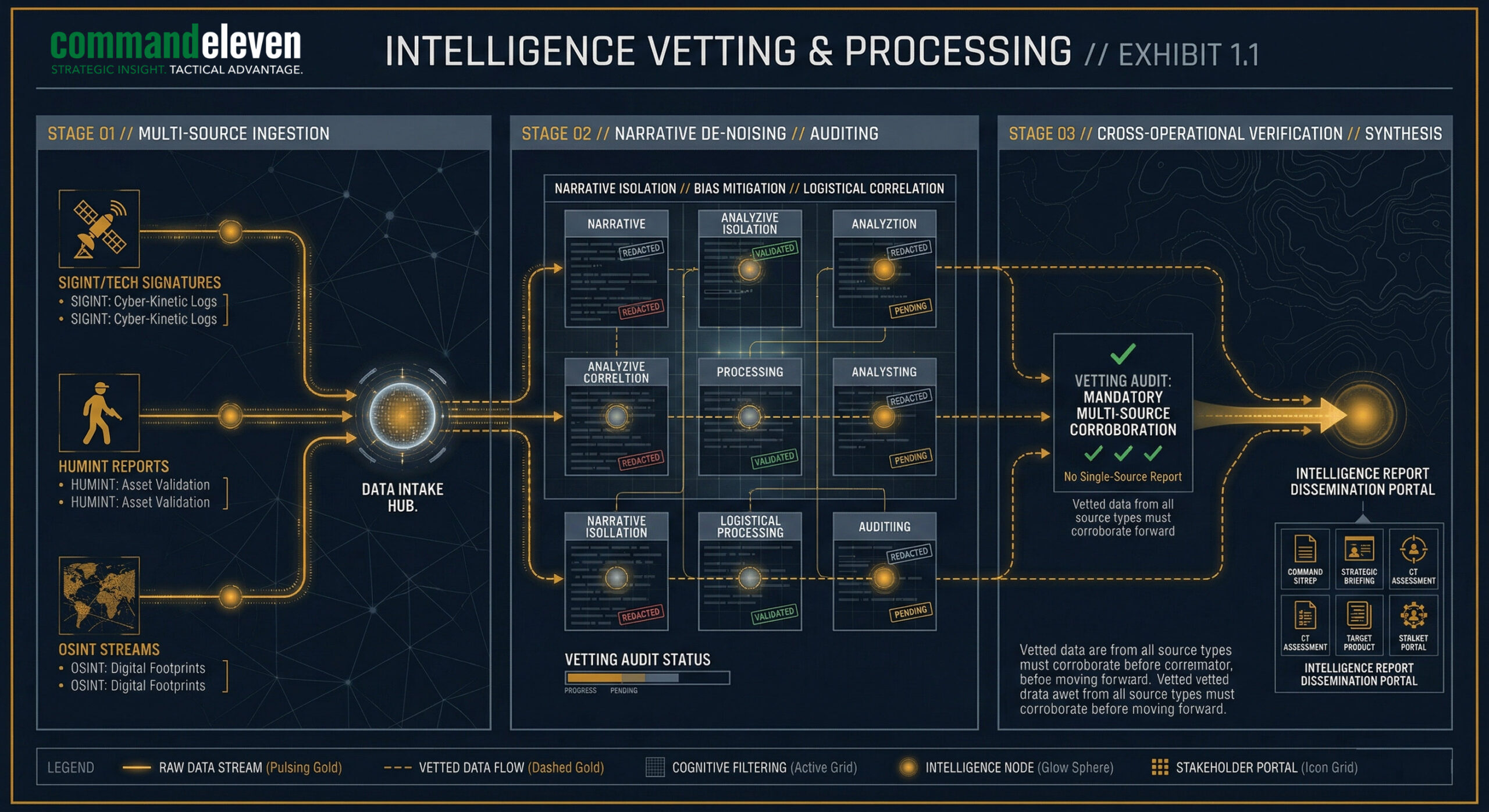
Every briefing is the result of a systematic, four-stage synthesis engine designed to move raw theater noise into actionable intelligence.
MULTI-DOMAIN INGESTION //
Raw data is harvested across three distinct layers:
HUMINT: Proprietary ground assets and professional military/security contacts.
OSINT: Advanced digital footprinting, satellite imagery, and public-record monitoring.
SIGINT/TECH: Technical signatures and cyber-kinetic event logs.
NARRATIVE DE-NOISING //
The Cognitive Division audits all incoming data to identify and isolate:
Manufactured narratives from state and non-state actors.
Cognitive influence operations targeting the information environment.
Institutional and regional biases that may skew data interpretation.
CROSS-OPERATIONAL VERIFICATION //
Mandatory multi-source corroboration. CommandEleven protocols strictly prohibit the publication of single-source intelligence.
A report is only cleared for final synthesis once it has been validated by an independent secondary stream.
STRATEGIC DISSEMINATION //
The Intelligence Division applies geopolitical context to the verified data.
The final output – SitRep, Strategic Briefing, or Assessment – is released to vetted stakeholders with clinical, kinetic-focused accuracy.
THE VETTING MATRIX //
SOURCE RELIABILITY (S-RANK) //
Source Reliability evaluates the history and provenance of the entity providing the data. We categorize sources on an alpha scale from A to F.
Rating | Description | Definition |
A | Completely Reliable | No doubt of authenticity, trustworthiness, or competence. History of high-accuracy reporting. |
B | Usually Reliable | Minor doubt. History of mostly valid information; most reports have been confirmed. |
C | Fairly Reliable | Doubt of authenticity or trustworthiness. Some history of valid information. |
D | Not Usually Reliable | Significant doubt. History of sporadic or invalid information. |
E | Unreliable | Lacking in authenticity, trustworthiness, and competence. History of invalid information. |
F | Reliability Unknown | New source or insufficient history to establish a reliability baseline. |
INFORMATION CREDIBILITY (C-RANK) //
Information Credibility evaluates the data itself, independent of the source, by cross-referencing it with existing intelligence and known regional patterns.
Rating | Description | Definition |
1 | Confirmed | Confirmed by other independent and reliable sources; logical and consistent with other info. |
2 | Probably True | Not confirmed, but consistent with other information on the subject. |
3 | Possibly True | Not confirmed; reasonably logical in light of other information but not confirmed. |
4 | Doubtful | Not confirmed; possible but not logical; no other information on the subject. |
5 | Improbable | Not confirmed; not logical; contradicted by other information on the subject. |
6 | Cannot Be Judged | No basis exists for evaluating the validity of the information. |
analytical
Tradecraft //
Beyond the SR/IC ratings, CommandEleven analysts utilize several Structured Analytical Techniques (SATs) to mitigate cognitive bias:
- Analysis of Competing Hypotheses (ACH): We weigh multiple explanations for an event to avoid “mirror imaging” or “premature closure.”
- Red Teaming: We intentionally challenge our own assessments by adopting the perspective of the adversary to identify vulnerabilities in our logic.
- Indicator Monitoring: We track specific regional “tripwires” (economic, kinetic, or cyber) that signal a shift in threat levels.
Operational Infrastructure & Regional Expertise //
CommandEleven operates from the epicenter of global kinetic activity, providing a unique vantage point that remote analysts cannot replicate. Our assessments are grounded in a sophisticated collection infrastructure.
The HUMINT Network
At the core of our “Engine” is a robust Human Intelligence (HUMINT) network comprising over 400+ proprietary assets.
- Recruitment & Vetting: Every asset is recruited, vetted, and trained internally by CommandEleven to ensure operational security and reporting integrity.
- Ground Truth: This network provides real-time “Ground Truth” from the world’s most volatile conflict zones, allowing us to bypass the noise of mainstream media and state-sponsored narratives.
SIGINT & Technical Collection
To augment our human intelligence, CommandEleven maintains dedicated Signals Intelligence (SIGINT) capabilities. By monitoring regional communication vectors and digital signatures, we identify shifts in militant logistics and intent before they manifest as kinetic actions.
The “Conflict Zone” Advantage
Headquartered within the world’s largest active conflict zone, our analysts possess an inherent understanding of the socio-political and tribal nuances that drive regional instability. This proximity allows for:
- Immediate Verification: Rapid cross-referencing of emerging events.
- Pattern Recognition: Identifying subtle “atmospheric” shifts in high-threat environments.
- Operational Vetting: The ability to physically verify data points that remain opaque to satellite or remote collection.
Specialized Areas of Responsibility (AOR) //
While our methodology is global, our primary expertise is concentrated in regions where the convergence of state and non-state actors creates the highest risk to global security:
- The Sahel Region: Monitoring the expansion of transnational militant franchises.
- Indian Subcontinent: Detailed tracking of TTP, the Taliban, and regional proxy networks.
- The Middle East: Specialized focus on Iranian cyber-kinetic capabilities and maritime threat vectors.
VETTING AND VALIDATION //
INSTITUTIONAL GUARANTEE //
All CommandEleven reports are subject to continuous longitudinal review.
If subsequent theater developments contradict previous assessments, a Revision Annex is issued to ensure the accuracy of the archive.
