OPERATIONAL ARCHITECTURE // DIVISION // INTEL
COGNITIVE OPERATIONS DIVISION //
Home » Services » Cognitive Operations » Cognitive Division – Operational Architecture
MANDATE //
The mapping, deconstruction, and neutralization of psychological influence and narrative infiltration.
Narrative Deconstruction //
Technical identification of the origins, trajectories, and intent behind hostile information operations.
Human Terrain Mapping //
Analyzing societal shifts and psychological stressors within a theater to predict non-kinetic instability.
Informational Defense //
Strategic frameworks to maintain institutional narrative integrity against asymmetric influence.
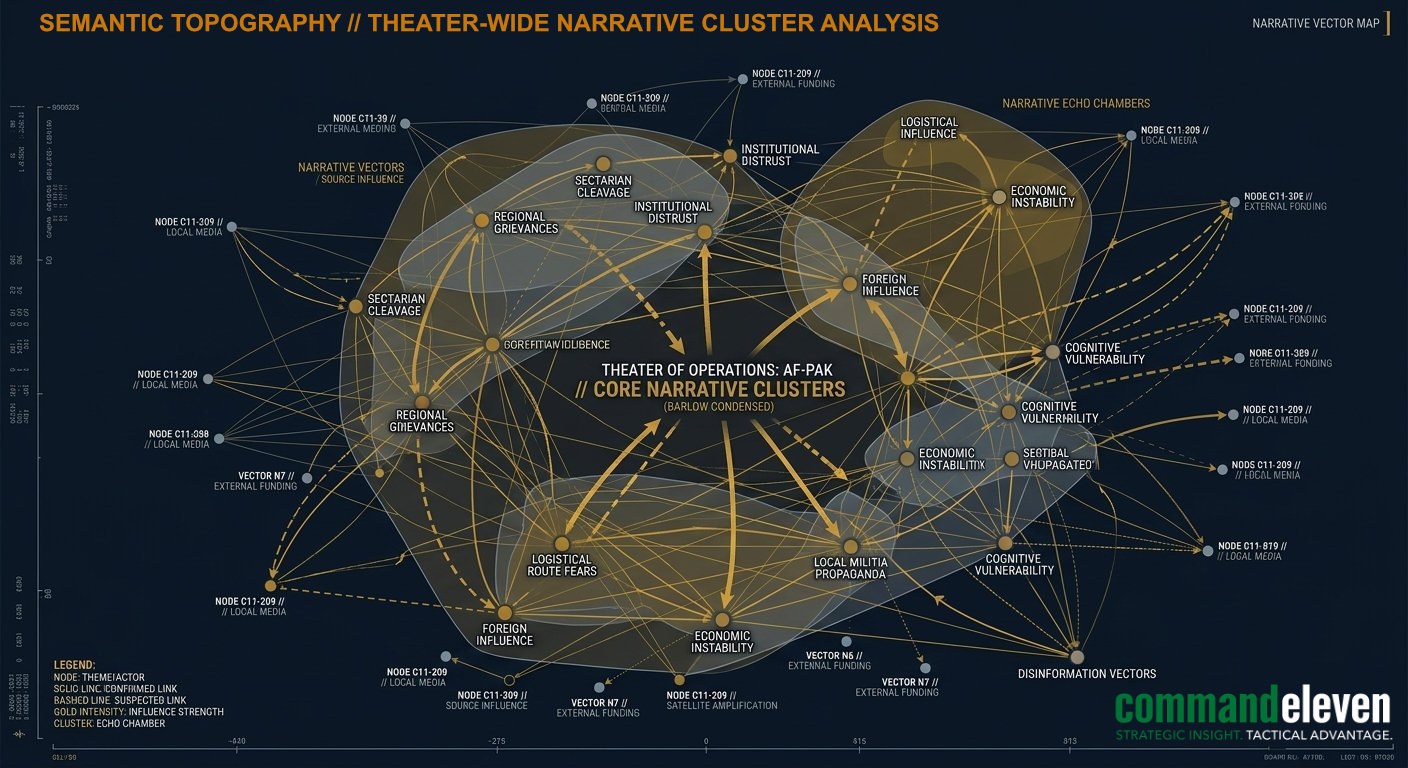
SEMANTIC TOPOGRAPHY // THEATER-WIDE NARRATIVE CLUSTER ANALYSIS
SEMANTIC SYNTHESIS //
The Cognitive Operations Division operates at the intersection of psychology and data science. We utilize a Semantic Synthesis framework to identify the weaponization of language and the engineering of perception.
INFILTRATION VULNERABILITY AUDITING //
Identifying demographic or institutional segments susceptible to narrative shift. We map the “psychological terrain” to find where foreign or asymmetric influence is most likely to take root.
ORIGIN TRACKING //
Utilizing technical signatures to trace narrative vectors back to their source. This identifies whether an emerging trend is an organic societal shift or a manufactured information operation.
NARRATIVE NEUTRALIZATION //
Developing counter-measures that do not simply “debunk” but rather “de-escalate” hostile influence by addressing the underlying psychological stressors driving the narrative.
COGNITIVE BRIEFS //
Cognitive Warfare by Foreign Actors: Nation-State Infiltration
An intelligence analysis of foreign cognitive warfare strategies, evaluating mass biometric data harvesting, algorithmic manipulation, deepfake deployment, and influencer co-optation.
Chinese Cyber-Attacks Against Western Critical Infrastructure
An intelligence analysis of offensive cyber doctrines, evaluating SOHO proxy networks, operational technology pre-positioning, and supply chain interception.
Chinese Information Warfare Strategies: Integrated Cognitive Control
An intelligence analysis of Chinese information operations, evaluating commercial platform data harvesting, subsea telecom interception, and the Three Warfares doctrine.
Russian Information Warfare Strategies: Computational Propaganda Matrix
An intelligence analysis of Russian information operations, evaluating automated bot infrastructures, generative deepfake obfuscation, and reflexive control doctrine.
The Fractured Levant: Shadow Economies and Banking Collapse
An intelligence analysis detailing the systemic collapse of Levantine sovereign banking, informal hawala networks, digital asset layering, and the co-optation of state fiscal infrastructure.
Iran’s Distributed Manufacturing Model: Asymmetric Proliferation
An intelligence analysis of decentralized defense industrial architectures, evaluating modular weapon kits, global supply chain exploitation, and proxy assembly protocols.
