OPERATIONAL ARCHITECTURE // DIVISION // INTEL
INTELLIGENCE DIVISION //
Home » Services » Intelligence Analysis » Intel Division – Operational Architecture
MANDATE //
The systematic harvesting and synthesis of ground-truth data to eliminate strategic ambiguity.
HUMINT Management //
Oversight of deep-cover assets across the Middle East and South Asia.
Multi-Source Synthesis //
Integration of SIGINT and OSINT to validate field reports.
Pattern Analysis //
Identifying historical echoes in modern conflict precursors.
OPERATIONAL DOCTRINE //
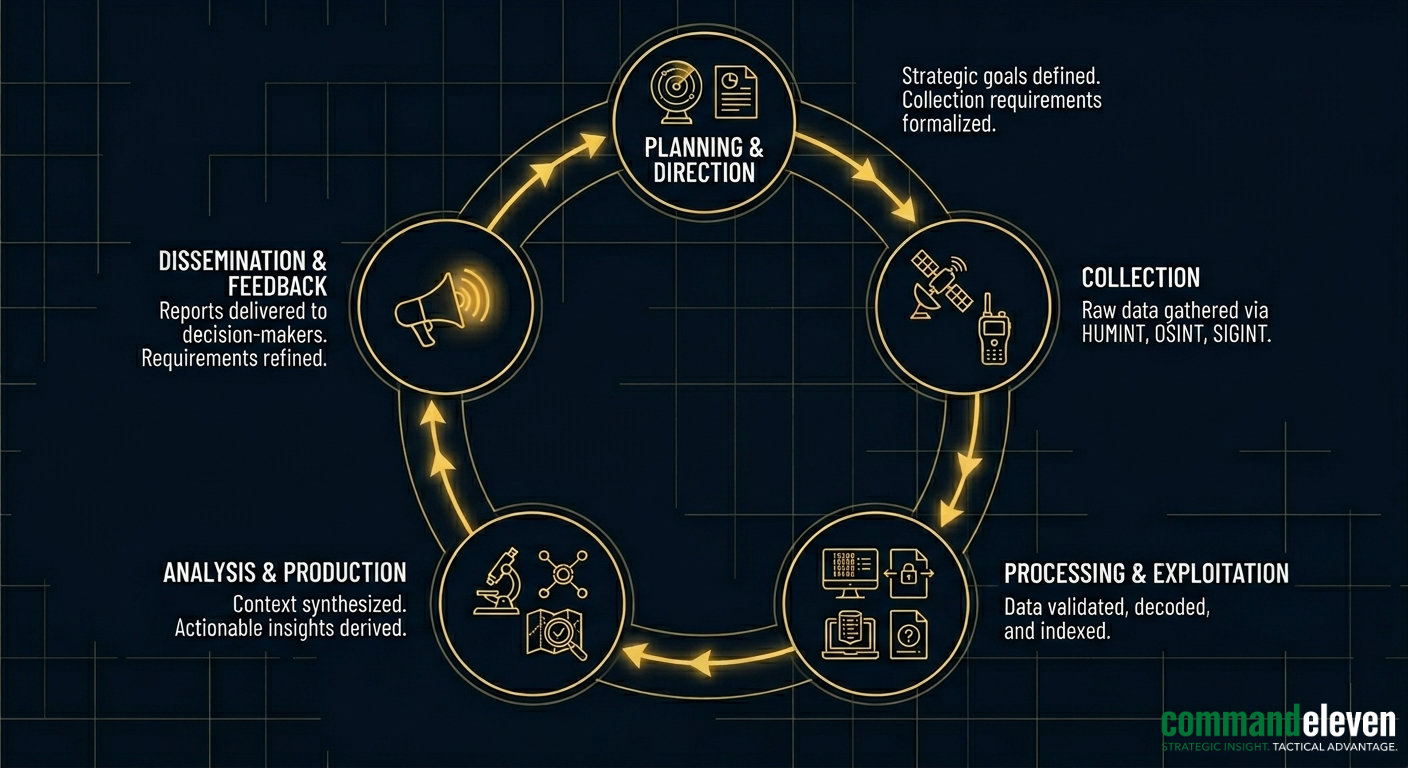
Intelligence Division assets prioritize the Validation Phase. Every data point harvested from the theater is subjected to a “Triple-Node Verification” process—cross-referencing HUMINT with technical signatures to ensure a zero-point margin of error before dissemination.
VALIDATION PROTOCOLS // OVERSIGHT
The Intel Division operates under a Zero-Point Margin of Error mandate.
Every data point harvested from the theater is subjected to the following Triple-Node Verification protocol before it is promoted to the Synthesis phase.
REDUNDANCY SCAN //
Raw HUMINT is cross-referenced against independent field assets within the same operational node. No single-source report is considered verified without a secondary, independent confirmation of the event or intelligence.
TECHNICAL CORRELATION //
Validated HUMINT is overlaid with available technical signatures, including OSINT (Open Source Intelligence) and SIGINT (Signal Intelligence) metadata. This ensures that the human reporting aligns with the digital and technical footprint of the theater.
TEMPORAL AUTHENTICATION //
Reports are analyzed for latency. Data is authenticated by its proximity to the event, ensuring that the information provided is not a legacy narrative but a real-time tactical specification.
OPERATIONAL REACH //

INTELLIGENCE BRIEFS //
Cognitive Warfare by Foreign Actors: Nation-State Infiltration
An intelligence analysis of foreign cognitive warfare strategies, evaluating mass biometric data harvesting, algorithmic manipulation, deepfake deployment, and influencer co-optation.
Chinese Cyber-Attacks Against Western Critical Infrastructure
An intelligence analysis of offensive cyber doctrines, evaluating SOHO proxy networks, operational technology pre-positioning, and supply chain interception.
Chinese Information Warfare Strategies: Integrated Cognitive Control
An intelligence analysis of Chinese information operations, evaluating commercial platform data harvesting, subsea telecom interception, and the Three Warfares doctrine.
Russian Information Warfare Strategies: Computational Propaganda Matrix
An intelligence analysis of Russian information operations, evaluating automated bot infrastructures, generative deepfake obfuscation, and reflexive control doctrine.
The Fractured Levant: Shadow Economies and Banking Collapse
An intelligence analysis detailing the systemic collapse of Levantine sovereign banking, informal hawala networks, digital asset layering, and the co-optation of state fiscal infrastructure.
Iran’s Distributed Manufacturing Model: Asymmetric Proliferation
An intelligence analysis of decentralized defense industrial architectures, evaluating modular weapon kits, global supply chain exploitation, and proxy assembly protocols.
