Executive Summary
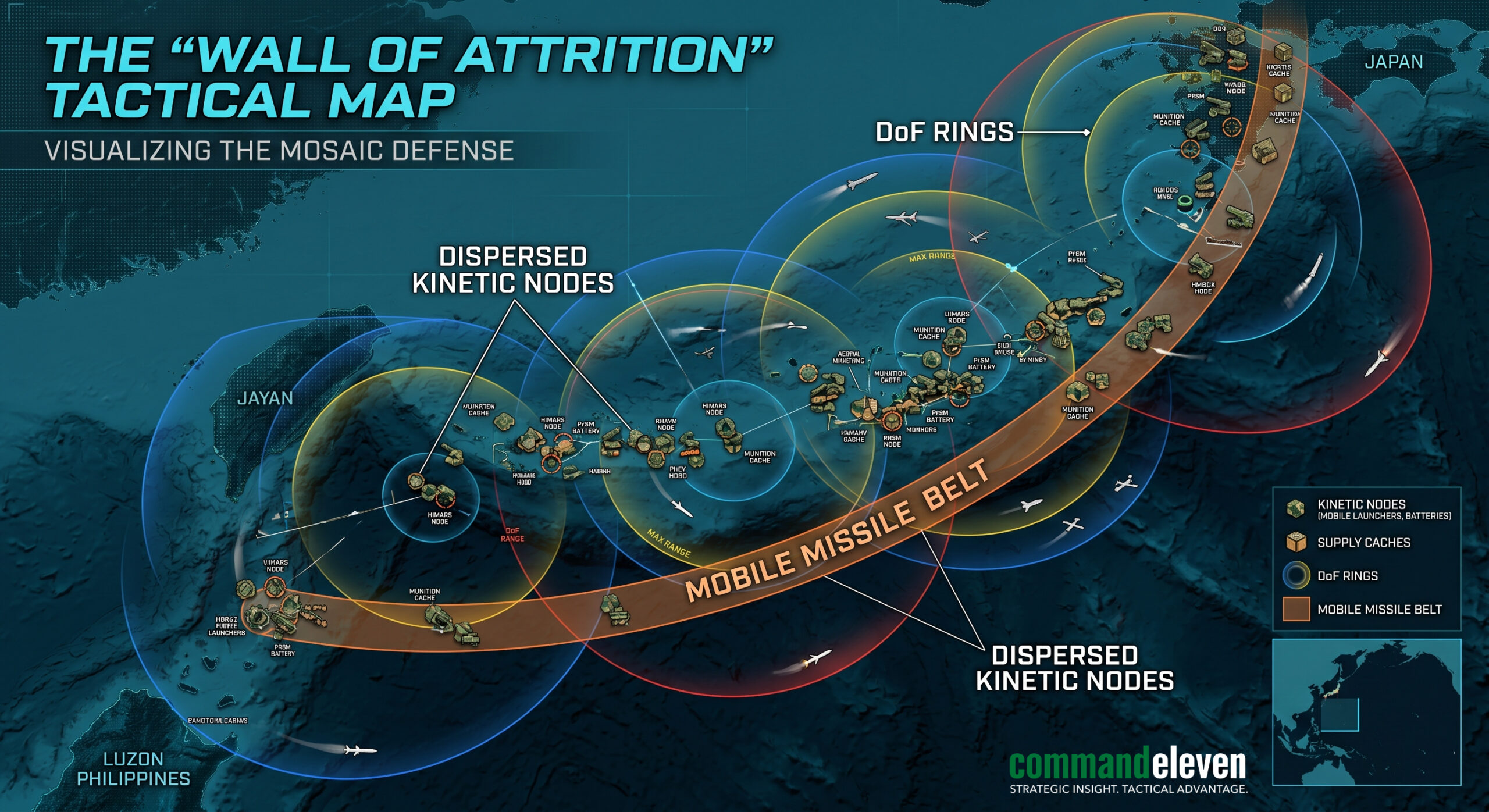
This article explains the terminal decline of the “Exquisite Deterrence” model following the munitions exhaustion of the 2026 Levantine conflict. It deconstructs the transition to a Deterrence by Denial posture, characterized by the physical hardening of the First Island Chain and the deployment of the Mosaic Defense. By prioritizing resilient force dispersion and “Attritable” systems, Allied forces in Tokyo, Taipei, and Manila are moving to compensate for a critical PGM (Precision-Guided Munition) deficit, establishing a mathematical “Wall of Attrition” designed to neutralize the PRC’s fait accompli windows.
3 Key Takeaways
- Transition to the “Wall of Attrition”: The 1.4x replenishment deficit in high-end interceptors has forced a shift from carrier-centric defense to a dispersed, mobile, and hardened network of thousands of small kinetic nodes.
- The “Exquisite” Failure: The legacy model of high-cost, low-volume platforms (F-35, Virginia-class) has reached a breaking point due to a catastrophic Cost-Exchange Ratio (CER) and maintenance attrition curves.
- The Hardening Multiplier (Dhard): Strategic survival now relies on increasing the physical resilience and “Noised” masking of regional assets to maintain deterrence despite a depleted munitions magazine.
The Post-Exquisite Era
The kinetic intensity of Operation Epic Fury in the Middle East has finalized the expiration of the “Exquisite Deterrence” model. As of Q2 2026, the U.S. and its allies no longer possess the depth of high-end Precision-Guided Munitions (PGMs) required to guarantee a “surgical” defense of the Pacific. Consequently, the strategy has shifted to Deterrence by Denial. The objective is no longer to “win” a decisive naval battle, but to make the cost of a PRC fait accompli mathematically prohibitive through the physical hardening of the First Island Chain.
The “Wall of Attrition”: Structural Reinforcement
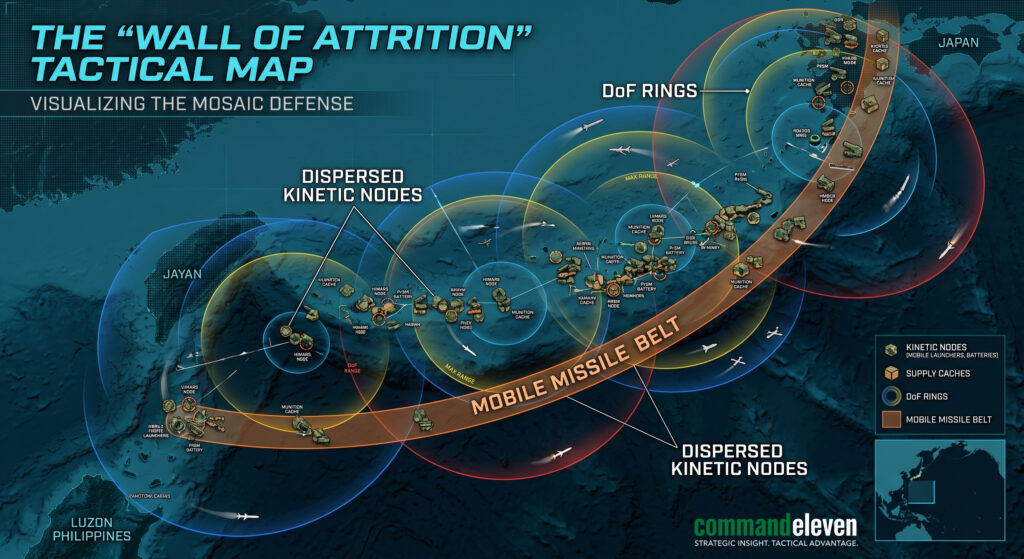
The 2026 defense of the First Island Chain—stretching from Japan through Taiwan to the Philippines—is now modeled as a synchronized Wall of Attrition. This move away from centralized carrier-centric defense is a response to the “Strategic Gap” identified in our Thursday audits.
Resilient Force Dispersion (The “Colby” Doctrine)
Following the tactical lessons of the 2026 drone swarms, Allied forces have implemented a radical dispersal of kinetic assets:
- The “Noised” Perimeter: Large, static airbases like Kadena are now viewed as “Legacy Targets.” Kinetic weight has been moved to hundreds of mobile, camouflaged nodes across the Ryukyu and Philippine archipelagos.
- Mobile Missile Belts: Deployment of Truck-mounted Typhon and HIMARS systems capable of firing PrSM (Precision Strike Missiles) and Tomahawks from jungle canopy or urban sprawl, negating the PRC’s satellite-guided “First Strike” advantage.
Taiwan’s “Porcupine” Maturation
Post-Epic Fury, Taiwan has pivoted from purchasing expensive aircraft to mass-producing “Attritable” systems.
- The Domestic Drone Surge: Taiwan has operationalized a fleet of 50,000 low-cost loitering munitions, creating a “Kinetic Cloud” over the Taiwan Strait that forces PLAN (People’s Liberation Army Navy) vessels to expend their own limited interceptors before they even reach the “Indonesia Gate.”
The Philippine Anchor: Fortifying the Luzon Corridor
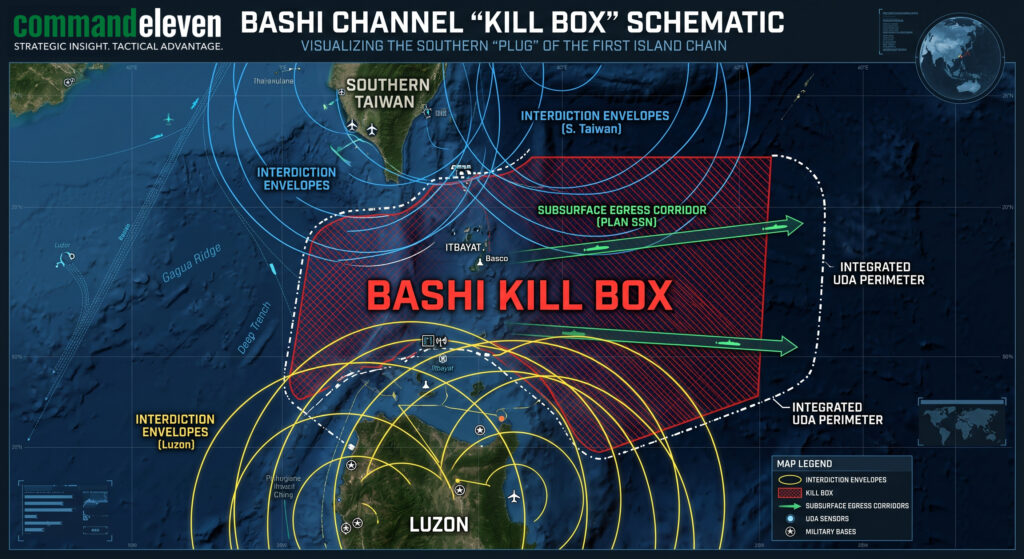
The Major Defense Cooperation Partnership (MDCP) with Jakarta and the expanded EDCA (Enhanced Defense Cooperation Agreement) sites in the Philippines have turned Luzon into the southern “Plug” of the chain.
- Bashi Channel Denial: The installation of long-range coastal sensors and anti-ship cruise missiles (ASCM) in the northern Philippines ensures that any PLAN egress into the Philippine Sea is funneled through a high-threat “Kill Box.”
- Logistical Sharding: The Philippines now hosts “Pre-Positioned Stockpiles” (PPS) of low-cost munitions, ensuring that the “Wall” can remain kinetic even if the primary U.S. supply lines from the mainland are disrupted by a “Flash-Dark” cyber-kinetic event.
Mathematical Modeling: The Cost of Invasion (Cinv)
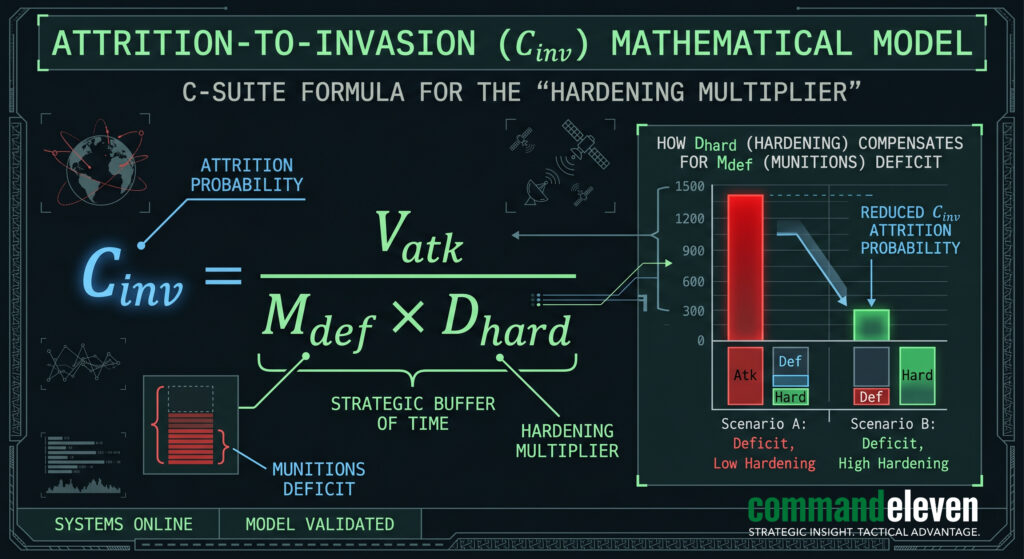
We model the probability of a successful PRC invasion using the above Attrition-to-Invasion Ratio, where:
- Vatk = Volume of attacking force.
- Mdef = Available defensive munitions (currently reduced by the Levantine Siphon).
- Dhard = The Hardening Multiplier of the First Island Chain nodes.
By increasing Dhard through physical fortification and force dispersal, the West compensates for the reduction in Mdef. The “Wall of Attrition” ensures that even with a depleted PGM magazine, the Cost-Exchange Ratio (CER) remains high enough to deter Beijing’s “Flash-Invasion” protocols.
Deconstructing the “Exquisite Deterrence” Model
The Exquisite Deterrence model is predicated on the “Quality-over-Quantity” axiom. It assumes that a technologically superior force, utilizing expensive, high-precision assets, can deter an adversary by threatening a surgical and overwhelming response. In the 2026 landscape, this model has encountered its terminal limit.
The Four Pillars of Exquisite Deterrence
The model is supported by a “four-pillar” architecture designed for high-end, short-duration conflicts:
- Exquisite Platforms: Reliance on multi-billion dollar “Tier-1” assets, such as the Ford-class carriers, Virginia-class submarines, and F-35 Lightning II aircraft. These platforms are designed for maximum survivability and lethality but are difficult and slow to replace.
- The Precision-Only Magazine: A munitions strategy focused on high-cost, high-fidelity PGMs (Precision-Guided Munitions) like the Tomahawk (Block V) and LRASM. These weapons offer a “one-shot, one-kill” probability but have a massive “Production-to-Expenditure” deficit.
- Vertical C2 (Command and Control): A centralized, top-down decision-making structure that relies on uncontested satellite communications (SATCOM) and a persistent, high-altitude ISR (Intelligence, Surveillance, and Reconnaissance) “unblinking eye.”
- Technological Overmatch: The belief that “Stealth” and “Electronic Warfare (EW)” superiority create an impenetrable shield that renders the adversary’s volume-based attacks irrelevant.
The “Exquisite” Failure in 2026
The Levantine Siphon and the rise of the Mosaic Defense have exposed three fatal flaws in this model:
- The Cost-Exchange Ratio (CER) Trap: When an “Exquisite” system expends a $3.9 million Patriot PAC-3 interceptor to neutralize a $20,000 Shahed-149 drone, the defender is being defeated economically even while succeeding tactically.
- The Maintenance Attrition Curve: Exquisite platforms are “brittle.” They require specialized parts and thousands of man-hours of maintenance. In a high-tempo conflict, these platforms reach a “Readiness Floor” where they can no longer generate sorties, regardless of pilot availability.
- Magazine Exhaustion: Because exquisite munitions are “hand-built” in limited quantities, the “Winchester” threshold (running out of ammo) is reached long before the adversary runs out of low-cost drones or missiles.
The Pivot: From Exquisite to Attritable
The transition to Deterrence by Denial marks the end of this era. Allied forces are now prioritizing “Attritable” systems—cheap, mass-produced, and autonomous—that can be lost in combat without creating a strategic crisis. The “Wall of Attrition” in the First Island Chain is the antithesis of the Exquisite model: it is built on the strength of a thousand small nodes rather than the fragility of a few exquisite ones.
Deconstructing the “Acoustic Handshake”
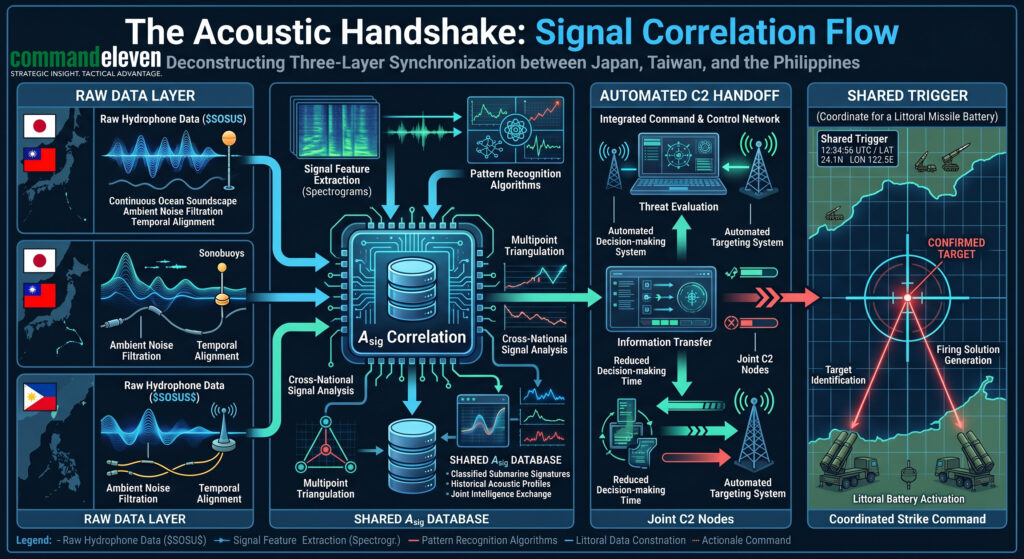
The Acoustic Handshake is the real-time, cross-national synchronization of undersea sensor data. In the 2026 battlespace, specifically within the Bashi Channel and the Sunda-Lombok corridors, this protocol ensures that the “Underwater Domain Awareness” (UDA) is a shared, unified picture rather than a series of disconnected national silos.
The Three Layers of the Handshake
The handshake operates across three distinct technical layers to ensure that a PLAN submarine signature detected by a Japanese hydrophone is instantly actionable by a Philippine missile battery.
- The Raw Data Layer (Hydrophone Integration):
- This involves the physical linking of the SOSUS (Sound Surveillance System) and the newer IUSS (Integrated Undersea Surveillance System) arrays.
- The “Handshake” utilizes Distributed Acoustic Sensing (DAS) via subsea fiber-optic cables. By measuring the minute phase-shifts in laser light caused by the pressure wave of a passing hull, the network creates a high-fidelity “Heat Map” of subsurface movement.
- The Algorithmic Layer ($A_{sig}$ Correlation):
- Raw acoustic data is useless without identification. The “Handshake” includes access to a shared Acoustic Fingerprint ($A_{sig}$) Database.
- When a “Shadow” hull or an SSN (Attack Submarine) emits a specific frequency—such as the unique “Blade Rate” of its propeller—the algorithm performs a sub-second correlation against the library of known PRC signatures.
- The C2 Handoff (The “Shared Trigger”):
- This is the most sensitive layer. It involves the automated transmission of a Target Suggestion across national fire-control networks.
- If a PLAN submarine is detected egressing the Bashi Channel, the “Handshake” bypasses traditional diplomatic “Request-for-Information” (RFI) delays, feeding the coordinates directly into the Mosaic Defense mesh via encrypted LPI (Low Probability of Intercept) burst-links.
Strategic Utility: Closing the “Southern Leak”
The Acoustic Handshake is the only reason the “Kinetic Gate” in Indonesia is viable. It allows for:
- Persistent Tracking: A target is “handed off” from Japanese sensors to Taiwanese sensors, and finally to Indonesian/Philippine sensors without the track being lost in the complex bathymetry of the archipelago.
- Deterrence by Detection: By demonstrating that the PRC’s “Quiet” submarines are being tracked in real-time by a unified allied front, the West re-establishes a level of subsurface deterrence that legacy “Exquisite” platforms could no longer provide alone.
UTM Indicators: Refining “Exquisite Failure”
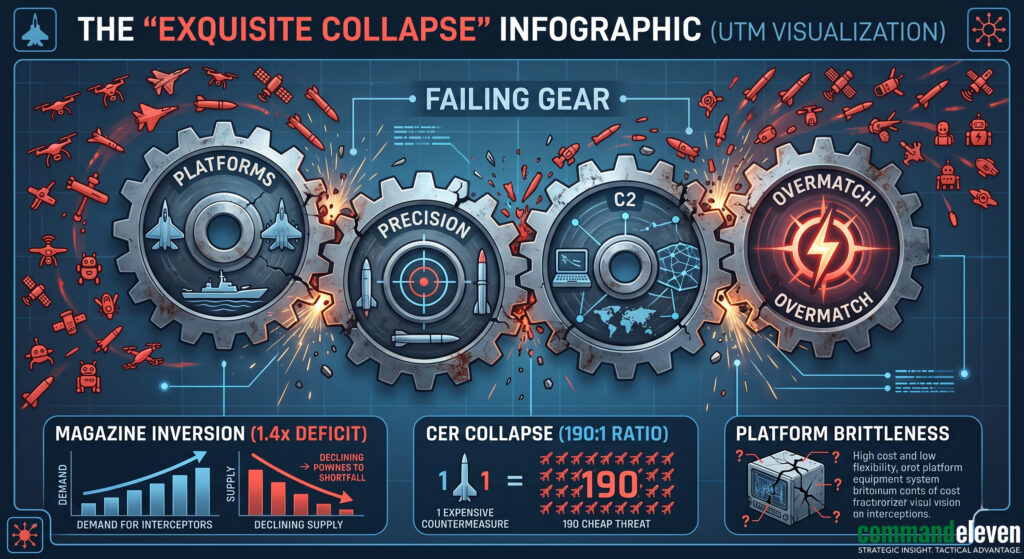
The Unified Threat Matrix (UTM) identifies specific “Red Line” indicators where the Exquisite Deterrence model collapses under the weight of 2026 multi-domain realities. These indicators serve as the forensic evidence for why the “Wall of Attrition” is now a mechanical necessity.
| Vector | Indicator (The “Tell”) | Forensic Impact | 2026 “Real-World” Case |
| KT (Kinetic) | Magazine Inversion | The rate of expenditure exceeds the rate of production by >3:1. | SM-6 depletion post-Operation Epic Fury. |
| KT (Kinetic) | Platform Brittleness | A single non-kinetic hit (ramming/drone strike) removes a $2B+ asset from the theater for >6 months. | LCS/Destroyer damage in the South China Sea Grey Zone. |
| CPT (Cyber) | HMI Ghosting | Adversary PLC rootkits mask the physical degradation of hardware on “Exquisite” digital displays. | SCADA targeting of Western municipal energy nodes. |
| GER (Geofinancial) | CER Collapse | The cost of the defensive intercept is >100x the cost of the offensive threat. | $2M Interceptors vs. $20k OWA Drones. |
| CI (Cognitive) | Decision Paralysis | The “Exquisite” requirement for 100% PID (Positive ID) prevents a strike within the 15-minute window. | “Shadow Fleet” interdiction delays in the Bashi Channel. |
Conclusion: The Survival of the Chain
The First Island Chain is no longer a tripwire; it is a fortress. The “Strategic Gap” of 2026 has forced a level of Allied synergy—spanning Tokyo, Taipei, Manila, and Washington—that legacy diplomacy could not achieve. While the U.S. Navy recovers from its logistical valley, the Mosaic Defense of the First Island Chain provides the only viable “Buffer of Time.”
CommandEleven Red Team Assessment: Beijing is aware that the “Window of Opportunity” created by the Middle East conflict is closing as the First Island Chain hardens. We anticipate a surge in “Cognitive Vector” attacks intended to break the political will of the Jakarta-Washington-Manila axis before the physical “Wall” is fully operationalized in Q4 2026.