[ CLASSIFICATION: STRATEGIC OVERWATCH // CRITICAL INFORMATION REQUIREMENT ]
Executive Summary: Technical Audit of the Protective Vacuum
This intelligence audit deconstructs the comprehensive failure of the United States Secret Service (USSS) to maintain a viable Field of Perimeter Control (FPC) between 2024 and 2026. Analysis of the five assassination attempts on both candidate and now President Donald Trump, alongside high-consequence breaches in D.C. and London, confirms a Successive Failure Loop. These are not isolated security lapses but are symptomatic of an institutional refusal to evolve beyond a 20th-century reactive doctrine.
CommandEleven identifies two primary drivers of this vacuum:
- Doctrinal Sclerosis: The USSS remains tethered to a physical-only “Thin Shell” model, leaving the Vertical (UAS) and Digital (C3) perimeters essentially uncontested.
- The AVHP Vector: Transnational adversaries, specifically the IRGC-QF and ISKP, have successfully implemented an Asymmetric Virtual Handler Protocol. This allows remote actors to trigger domestic “Biological Assets” via encrypted mesh-networks, bypassing traditional counter-surveillance and weaponizing domestic political noise as atmospheric cover.
This report concludes that the “Protective Envelope” has been functionally defeated. Restoration of mission integrity requires an immediate shift to an Intelligence-Led Predictive Envelope – integrating SIGINT-heavy perimeters, behavioral AI, and aggressive interdiction of the Cloud-to-Kinetic (C2K) supply chain. Failure to implement these Tier 1 tactical shifts will ensure the continued success of state-sponsored probes.
Key Intelligence Takeaways (KITs)
- KIT 1: The Normalization of Perimeter Defeat.
The recurrence of “Point-of-Failure” commonalities – specifically unsecured high ground, drone-blindness, and face-to-face incursions – proves that Butler was not an anomaly, but the blueprint for a systemic degradation of zone integrity. The USSS currently lacks the doctrine to secure the modern vertical and digital perimeters. - KIT 2: The C2K (Cloud-to-Kinetic) Reality.
Transnational adversaries, including the IRGC-QF and ISKP, have successfully weaponized the U.S. domestic “noise.” By utilizing an Asymmetric Virtual Handler Protocol (AVHP), these actors project lethal force through “remote-controlled” domestic assets, effectively bypassing physical counter-surveillance and creating a gap that the USSS Intelligence Division is structurally incapable of closing. - KIT 3: Institutional and Technical Attrition.
The technical anomaly aboard Air Force One and the investigative failures post-Butler indicate a collapse in deterrence. The USSS is currently “fighting the last war” with a 20th-century mindset, failing to integrate the SIGINT and AI-driven behavior detection required to mitigate 21st-century Cyber-Kinetic probes.
The Chronology of Attrition – From Butler to the 2026 Vacuum
Zero-Day: The Butler Engagement & The Failure of Zone Integrity
The July 2024 assassination attempt in Butler, Pennsylvania, serves as the definitive point of divergence for U.S. executive security. From a tactical standpoint, Butler was not a failure of individual bravery, but a total collapse of Integrated Perimeter Defense.
- The Roof-Line Paradox: The failure to secure a high-ground position within 150 meters of the primary asset is a violation of foundational EP (Executive Protection) principles. This “unsecured high ground” has now become a recurring vulnerability in the USSS “noisy” event model.
- Information Siloing: The inability to synthesize local law enforcement sightings of a suspicious actor with the USSS tactical command (the “Command Post”) reflects a breakdown in the Intelligence-to-Kinetic pipeline. This gap remains unbridged in 2026.
- Counter-UAS (Unmanned Aerial Systems) Negligence: The perpetrator’s ability to conduct pre-kinetic drone surveillance of the site – despite the presence of USSS electronic warfare assets – exposed a critical technological lag that adversaries have since exploited.
The Technological Lag: Mesh-Network Evasion Tactics
A primary failure point in Butler – and a persistent vulnerability in 2026 – is the USSS’s inability to interdict Below-the-Radar (Mesh) Drone Technologies. Non-state actors have evolved beyond standard RF (Radio Frequency) control, utilizing decentralized mesh-networking to evade traditional Electronic Warfare (EW) umbrellas.
- Frequency Hopping & Mesh-Control: Adversaries are now utilizing multi-node mesh networks where the drone is not controlled by a single point-to-point signal, but by a “web” of localized low-power nodes. This makes standard “Jamming” ineffective, as there is no primary command signal to sever.
- The “Silent” Probe: These tactics allow for pre-kinetic site surveys – as seen in Butler – where drones can loiter and map roof-lines without triggering the EW “tripwires” typically deployed by USSS specialized units.
The Failure of the Intelligence-to-Kinetic (I2K) Pipeline
In military doctrine, the Intelligence-to-Kinetic Pipeline describes the speed and accuracy with which raw data is converted into a physical response. The USSS has failed to adapt this military-grade speed to its civil-protection mandate.
- The Lag Variable: In military targeting, once a sensor (HUMINT or SIGINT) identifies a threat, the “Time-to-Target” is minimized. In Butler, and later in the Charlie Kirk engagement, the “Intelligence” (suspicious actor reports) existed, but the “Kinetic” response (interdiction) was stalled by bureaucratic communication loops.
- Fragmented Command: Unlike a military Joint Operations Center (JOC), the USSS currently operates with a fragmented reporting structure that prioritizes administrative clearance over immediate perimeter neutralizing.
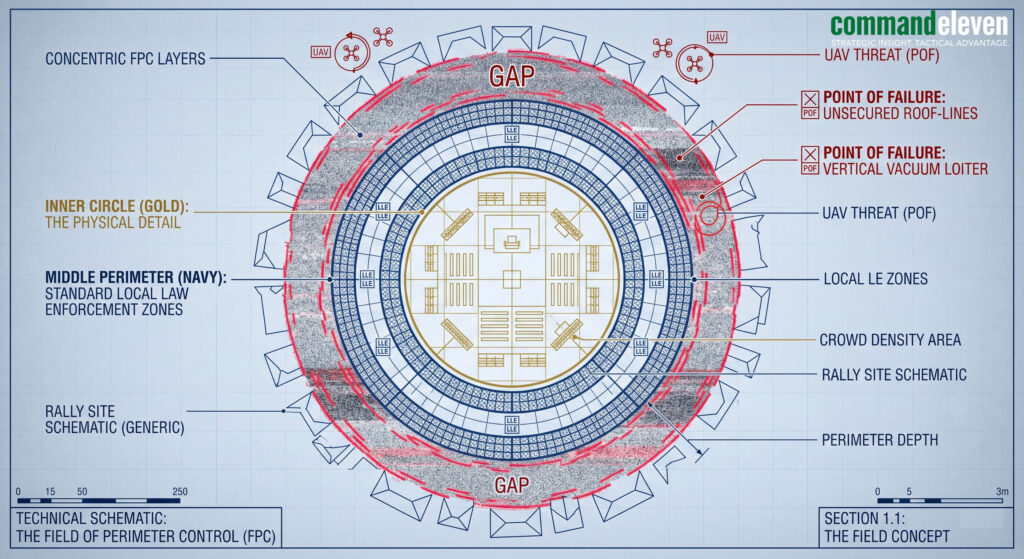
The Absence of Field of Perimeter Control (FPC)
The most egregious tactical failure across the Butler, London, and D.C. incidents is the inability to establish a Field of Perimeter Control (FPC).
- Military Definition of FPC: A proactive tactical posture where every vector within the engagement zone is monitored, filtered, and controlled through successive layers of interdiction.
- The USSS “Thin Shell” Problem: Instead of a multi-layered “field,” the USSS has defaulted to a “Thin Shell” model – protecting the immediate person but failing to control the environment. This is why protestors reached face-to-face proximity in D.C. and why a single individual could secure high ground in Butler.
- The Perimeter Defeat: By failing to establish FPC, the USSS allows adversaries to “test the fence.” Once the field is breached (as in the London motorcade), the “Layers of Security” are revealed to be non-consecutive, making the final breach a matter of timing rather than complexity.
The Normalization of the Breach: D.C., London, and the Face-to-Face Variable
Since Butler, the “Protective Envelope” has transitioned from a rigid barrier to a porous screen. This is evidenced by the “Atmospheric” breaches that preceded more lethal kinetic attempts.
- The D.C. Incursion (Joe’s Seafood Prime Steak & Stone Crab): In a Tier 1 security environment, an asset the level of the President should never be “surprised” by hostile actors. The ability of Code Pink protestors to reach face-to-face proximity inside a secured venue indicates a failure in Advance Site Survey and Inner Perimeter Validation. It signals to adversaries that the “Final 10 Feet” are vulnerable.
- The London Motorcade Breach: The London incident demonstrated a failure in Route Integrity. By allowing a protestor to penetrate the motorcade’s “buffer zone,” the USSS and its local partners exposed the vulnerability of mobile assets to low-cost, high-impact interdiction. In 2026, a “protestor” is often a probe for a more lethal kinetic follow-up.
The Technology Attrition: The Air Force One Anomaly
The security/electrical failure aboard Air Force One during the London return transit must be analyzed as a Targeted Technical Interdiction.
- The Cyber-Kinetic Probe: In the current threat landscape, technical failures on “Special Mission” aircraft are rarely organic. This incident suggests a sophisticated attempt to disrupt the President’s Command, Control, and Communications (C3).
- The Impact: If the “Flying White House” can be compromised technically, the psychological barrier of “Total Security” is shattered, emboldening state-sponsored actors (IRGC/MSS) to test deeper system vulnerabilities.
Technical Audit: The Air Force One C3 Disruption
The technical failure on Air Force One (AF1) must be analyzed through this FPC vacuum. The “Field” of protection must extend into the digital and electrical architecture of the transport assets.
- Internal Field Failure: If an “Electrical Anomaly” occurs on a VC-25A, it represents a breach of the Technical Perimeter. In a 2026 environment, this is viewed as a Cyber-Kinetic Probe.
- C3 Compromise: The objective of such a probe is to test the resilience of the President’s Command, Control, and Communications (C3). By forcing a “Return to Base,” the adversary achieves a successful “Mission Kill” without firing a shot – proving that the USSS cannot maintain FPC in the digital domain.
The Investigative Void: The Charlie Kirk Precedent
The “weak investigative process” following the Charlie Kirk assassination attempt serves as a force multiplier for future attackers.
- Deterrence Decay: When the post-incident investigation fails to publicly and surgically dismantle the radicalization engine behind an attack, it creates a “Green Light” effect.
- The Successive Failure Loop: Butler’s unlearned lessons (Roof-lines/Drone-gaps) led directly to the vulnerability seen in the Charlie Kirk engagement. The USSS is now caught in a loop where they are investigating the last failure while the adversary is already exploiting the next one.
The Radicalization Engine – The Virtual Handler & Transnational Proxies
The Death of the “Lone Wolf” Myth
The USSS and FBI continue to categorize domestic attackers as “self-radicalized lone actors.” From an intelligence perspective, this is a dangerous mischaracterization. In the current threat landscape, “Lone Wolves” are actually Remote-Operated Assets.
- The New Orleans Blueprint: The January 2025 Bourbon Street attack by Shamsud-Din Jabbar (an IT specialist and 82nd Airborne veteran) serves as a case study. Despite “no foreign involvement” being cited by federal agencies, the tactical execution – utilizing body armor, rented heavy vehicles to bypass malfunctioning barriers, and military-grade C2 – mirrors the ISKP virtual handbook.
- The Palm Springs Vector: The Palm Springs bombing investigations revealed direct digital links to a “Virtual Entrepreneur” – an offshore handler who provides tactical coaching, target selection, and psychological anchoring without ever stepping onto U.S. soil.
The Asymmetric Virtual Handler Protocol (AVHP)
The AVHP is a low-cost, high-deniability model utilized by the IRGC-QF and ISKP to project power into the U.S. interior. It bypasses traditional USSS counter-surveillance by exploiting the “Digital-to-Kinetic” gap.
- Phase 1: Deep-Dive Social Mining: Handlers use AI-driven tools to identify domestic individuals with specific “friction points” (e.g., military veterans with grievances or radicalized ideological converts).
- Phase 2: The Encrypted Handshake: Contact is established via mainstream social media before transitioning to decentralized, end-to-end encrypted (E2EE) mesh-communications.
- Phase 3: The Technical Coaching: Unlike 2010-era radicalization, 2026 handlers provide specific technical data: Mesh-network drone frequencies, USSS radio-frequency blind spots, and vulnerability maps of high-value transport assets like AF1.
The IRGC-QF Domestic Pivot: State-Sponsored Assassination
While ISIS focuses on mass-casualty events, the IRGC (Islamic Revolutionary Guard Corps) has pivoted toward State-Sponsored Decapitation Strikes on U.S. soil.
- Retaliatory Doctrine: IRGC commanders (including newly installed Chief Ahmad Vahidi) have explicitly framed the targeting of Donald Trump as a “legal and tactical necessity” for regional leverage.
- The Proxy Synchronization: By utilizing domestic “Biological Assets” (radicalized U.S. citizens), the IRGC achieves Plausible Deniability. If a breach occurs – like the D.C. restaurant or the London motorcade – Tehran can distance itself from the “protestor” while reaping the intelligence gathered during the probe.
Psychological Interdiction: The “Atmospheric” Trigger
The Virtual Handler does not just provide tactics; they provide the Atmospheric Cover.
- Noise vs. Signal: Handlers instruct assets to move during periods of high domestic polarization. This ensures that the USSS Intelligence Division is “saturated” with low-level threats (protestors/noise), allowing the lethal “Signal” (the assassin) to penetrate the Field of Perimeter Control undetected.
- The London/D.C. Probes: CommandEleven assesses that the face-to-face breaches in D.C. and London were likely “Dry Runs” or probes orchestrated to test the response times and “flinch factors” of the President’s inner detail.
Technical Definition: Cloud-to-Kinetic (C2K) Architecture
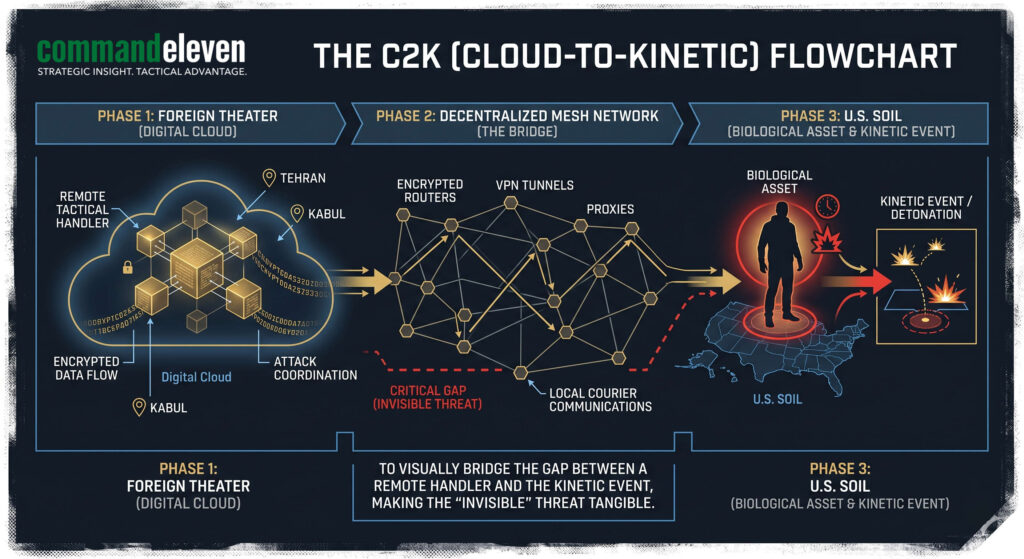
Cloud-to-Kinetic (C2K) is the operational process by which a remote, non-theater actor (The Handler) utilizes decentralized digital infrastructure to direct physical force against a high-value target (The Asset).
Unlike traditional “Lone Wolf” radicalization, C2K involves a Command and Control (C2) link that remains active until the moment of kinetic engagement.
- The Cloud Layer: Utilizes E2EE mesh-networks and hidden social nodes to transmit tactical data (GPS coordinates, USSS blind spots, and technical evasion protocols).
- The Kinetic Layer: The “Biological Asset” (The Attacker) on the ground, who serves as the terminal delivery system for the Handler’s instructions.
The C2K Advantage: It allows transnational entities like the IRGC-QF to project lethal force within the U.S. domestic “Field of Perimeter Control” with absolute deniability and zero physical logistical footprint.
The Doctrine of Failure – Strategic Inertia and the Technology Gap
Institutional Sclerosis: Fighting the Last War
The fundamental failure of the USSS is a refusal to evolve beyond the Reagan-Era Protective Model. While the agency remains proficient at “Close-In” physical protection (reactive), it has failed to adapt to a world of Distributed Lethality. Current USSS doctrine is predicated on a “flinch response” – intercepting a threat once it has entered the physical perimeter.
- In the age of high-powered optics and C2K-guided assets, once a threat is visible to the detail, the “Protective Envelope” has already been defeated.
- The shift toward administrative compliance and political “optics” has diluted tactical rigor.
- As seen in D.C. and London, the desire for the asset to appear accessible has been allowed to compromise the Field of Perimeter Control (FPC).
Personnel Attrition and the “Elite” Dilution
The USSS is currently suffering from a mission-to-resource paradox. The expansion of the “Protected Class” combined with high-tempo 2026 campaign cycles has led to chronic Operational Fatigue. When agents are rotated through back-to-back high-consequence events without adequate recovery, situational awareness drops.
This “Alert Fatigue” is exactly what allowed the Butler perpetrator to loiter and survey the site for extended periods without interdiction. The agency’s training pipeline remains focused on traditional firearms and physical intervention, largely neglecting the SIGINT (Signals Intelligence) and Electronic Warfare (EW) competencies required to identify a mesh-network drone controller or a virtual handler probe.
The Counter-UAS (C-UAS) Vacuum
The most visible technology gap is the agency’s inability to secure the Vertical Perimeter. Butler was the “proof of concept” for drone-led assassination, yet the USSS response remains fragmented. While the USSS has access to detection technology, their Mitigation Protocol (the ability to legally and technically “drop” a drone) is hamstrung by jurisdictional friction and fear of collateral electronic interference. The USSS’s standard EW suites are optimized for high-power, point-to-point signals. They are effectively blind to the low-power, frequency-hopping mesh networks utilized by sophisticated non-state actors (ISKP/IRGC).
Digital Perimeter Erosion: The C3 Vulnerability
The “Air Force One Anomaly” highlights a broader failure to secure the Presidential C3 (Command, Control, and Communications). The USSS views “Cyber” as a separate department. Modern protection requires a unified Cyber-Physical Security doctrine. If an adversary can disrupt the electrical or communication bus of a transport asset, they have effectively blinded the protective detail, creating a window for a kinetic follow-up. There is a recurring failure to integrate real-time digital threat indicators (e.g., a sudden spike in specific encrypted traffic in a 2km radius) with the physical agents on the ground. The “Intelligence” is stuck in a dashboard while the “Kinetic” detail is looking at the crowd.
The Restoration of the Envelope – CommandEleven Tactical Recommendations
Transitioning to the Predictive Envelope
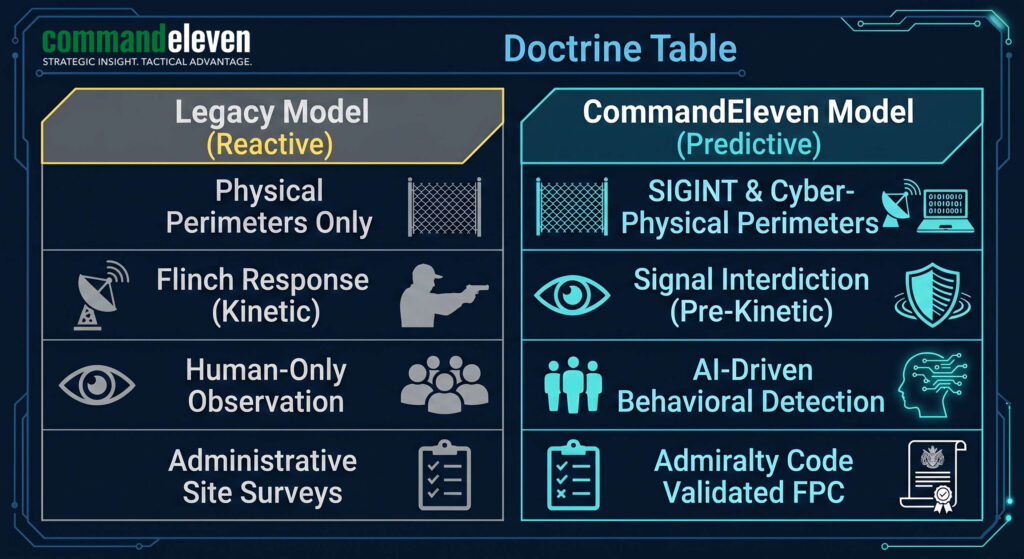
The USSS must move away from the “Thin Shell” and implement a Predictive Envelope that prioritizes interdiction at the Signal Phase rather than the Kinetic Phase.
- SIGINT-Heavy Perimeters: Every EP detail must include a dedicated Electronic Warfare & Signal Analysis (EWSA) unit. Their job is not just to jam signals, but to map the local RF environment to identify the “Silent Probes” of mesh-network drones before they reach line-of-sight.
- Behavioral AI Integration: Real-time facial recognition and behavior detection must be deployed at the outer perimeter to identify known radicalization proxies and “pre-kinetic” behavioral cues in high-noise environments like D.C. or London.
Harmonizing the Intelligence-to-Kinetic (I2K) Pipeline
To stop the “Successive Failure Loop,” the command structure must be flattened.
- Unified Tactical Command (UTC): Elimination of jurisdictional silos. The “Command Post” must have direct, sub-second communication channels to every local law enforcement officer on the perimeter.
- Admiralty Code Accountability: Every site survey must be rated using a standardized risk metric (e.g., Admiralty Code). If a site fails to meet the Field of Perimeter Control (FPC) threshold – such as an unsecured roof-line within 200m – the event is aborted. No exceptions for political “optics.”
Countering the Virtual Handler (AVHP Mitigation)
Defeating the Cloud-to-Kinetic threat requires aggressive counter-radicalization and digital interdiction.
- The Digital Counter-Probe: Intelligence agencies must aggressively hunt for “Virtual Entrepreneur” signatures within encrypted social conduits. When a handler is identified, their domestic “Biological Assets” must be neutralized before they move into the pre-operational phase.
- Hardening the Digital Assets: Transport assets (AF1, Motorcades) must undergo continuous Cyber-Kinetic Stress Tests. The “Electrical Anomaly” in London must be the last time a primary transport asset is allowed to fail technically in a hostile or high-tension environment.
The 0400 GMT Integration
The USSS must augment its internal capabilities with private sector Tier 1 Intelligence Hubs.
- Real-Time Data Injection: Incorporating regional geoeconomic and kinetic data streams – such as those provided by CommandEleven – allows the protective detail to understand the “Atmospheric” triggers that handlers use to launch attacks.
- Strategic Foresight: Moving beyond “who is in the crowd” to “what is the global threat vector today.”