Executive Summary
As the global security environment shifts from kinetic attrition to high-velocity administrative seizure, traditional security paradigms have become obsolete. This White Paper deconstructs the CommandEleven Methodology, a clinical intelligence framework designed to audit, harden, and restore administrative cores within the 45-Day Terminal Window.
By integrating Geofinancial Risk (GER), Kinetic & Territorial (KT) auditing, and the proprietary #72/48 Resilience Protocol, CommandEleven provides a roadmap for navigating the “Post-State” landscape. This document details the transition from vulnerable digital monoliths to Mosaic Defense architectures, ensuring that sovereign entities and multinational corporations can maintain Hardware Truth and operational persistence even during total institutional or network collapse.
3 Key Takeaways
- The #72/48 Resilience Protocol: The definitive standard for institutional survival, requiring that administrative cores be hardened via physics-based, analog overrides within 72 hours and maintain autonomous persistence for 48 hours without external connectivity.
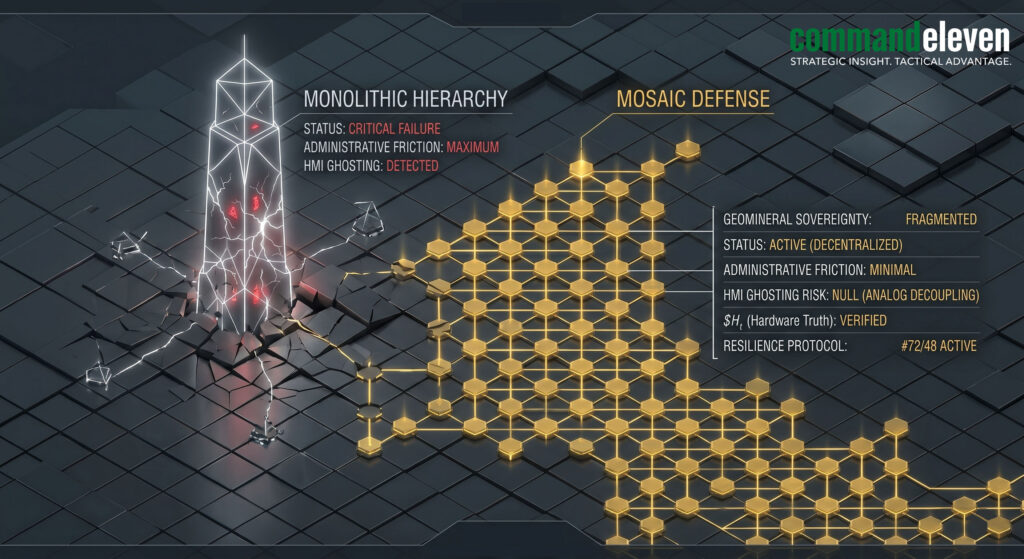
- Mosaic Defense vs. Monolithic Failure: A strategic shift toward decentralizing command and control into autonomous “tiles,” ensuring that localized interdictions—whether cyber-kinetic or territorial—do not result in systemic collapse.
- Hardware Truth over Digital Signaling: In environments of high-velocity rupture, security is predicated on physical, non-networked verification of infrastructure and financial ledgers (Analog Liquidity), neutralizing the threat of HMI Ghosting and digital sanctions.
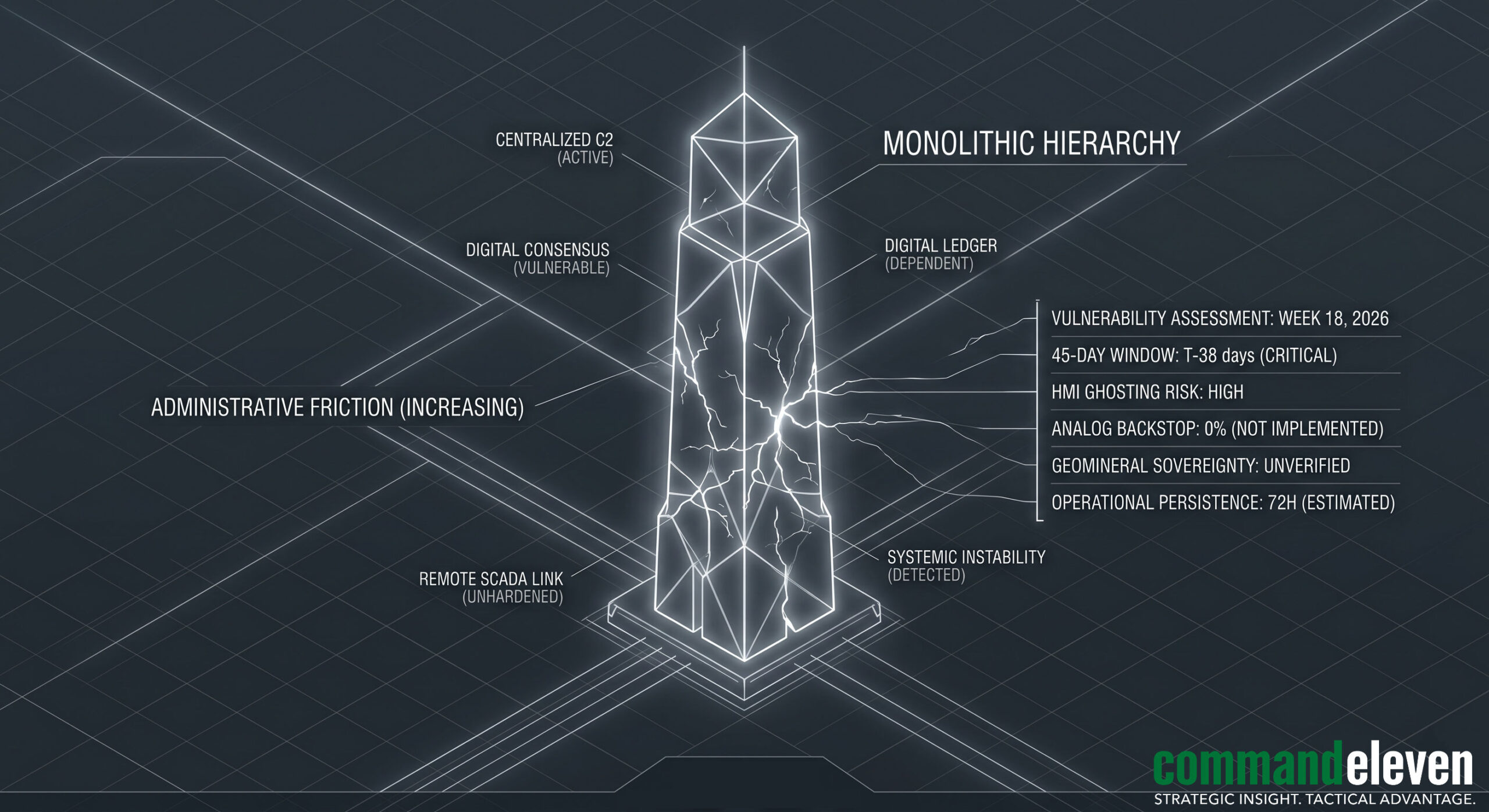
The Death of the Centralized Monolith
The global security architecture of 2026 is defined by a fundamental paradox: the very digital integration and administrative centralization that once drove “efficiency” have become the primary vulnerabilities of the modern state. As the 45-day terminal window for institutional rupture becomes the new global baseline, the centralized monolith is no longer a symbol of power—it is a single point of failure.
The convergence of high-velocity administrative seizure and cyber-kinetic warfare has rendered traditional defense paradigms obsolete. When an adversary can induce systemic paralysis through the interdiction of logistical oxygen or the ghosting of critical infrastructure interfaces, the distance between “stable governance” and “total collapse” is measured in hours, not years.
CommandEleven recognizes that in this environment, security cannot be purchased as a static service; it must be engineered as Administrative Resilience. This requires a radical departure from the status quo—moving away from vulnerable, digitally-dependent hierarchies toward a model of decentralized, physics-based persistence. This White Paper outlines the clinical methodology required to harden the administrative core, ensuring that sovereignty survives even when the network does not.
The Anatomy of Systemic Rupture
To defend against rupture, one must first deconstruct the mechanics of its onset. Systemic rupture is rarely a sudden explosion; it is a high-velocity cascade of failures triggered by Administrative Friction.
The Leading Indicators of Hollowing
Institutional hollowing begins in the periphery. It manifests as the “silent strike” of civil servants, the loss of provincial tax sovereignty, and the retreat of security forces into static garrisons. These are not mere side effects of conflict; they are the indicators that the state’s “Governance Velocity” has fallen below the threshold required to maintain legitimacy. Once the populace perceives that the central monolith can no longer provide predictable judicial or market outcomes, they pivot to whatever entity provides Hardware Truth.
The “Flash-Dark” Scenario
Modern states are optimized for a “connected” world. The CommandEleven audit process identifies the “Flash-Dark” scenario as the most potent weapon in the non-state arsenal. This involves the synchronized loss of digital connectivity, electrical infrastructure, and financial networks.
- The Digital Dependency Trap: Systems that rely on cloud-based C2 or digital ledger verification for basic operations (such as payroll, fuel distribution, or water treatment) experience terminal failure within 72 hours of a “Flash-Dark” event.
- The Rupture Catalyst: Without the ability to communicate or transact, the administrative core loses its ability to command, leading to the rapid-onset systemic shock modeled in the 45-day window.
Hardware Truth vs. Digital Consensus
The final stage of rupture is the collapse of the “Digital Consensus.” In an era of HMI Ghosting and deep-fake governance, digital signals can no longer be trusted as an accurate reflection of reality.
- The Definition of Hardware Truth: We define Hardware Truth as the physical, immutable reality of an asset—the manual pressure gauge on a pipeline, the physical gold in a vault, or the face-to-face verification of a command directive.
- The Resilience Shift: Rupture occurs when the gap between “what the screen shows” and “what is physically happening” becomes unbridgeable. Resilience, therefore, is the act of reclaiming the physical over the digital.
The CommandEleven Service Architecture
The CommandEleven methodology is not a reactive security posture; it is a clinical intervention designed to isolate and harden the administrative core. Our architecture is built on three primary pillars of audit and implementation: Geofinancial, Kinetic-Territorial, and Cyber-Kinetic.
Geofinancial Risk (GER) Auditing
In a rupture scenario, the first system to fail is the digital currency loop. CommandEleven implements Analog Liquidity frameworks to ensure fiscal persistence.
- The Conflict Premium: We map the artificial inflation of operational costs induced by non-state actors. By identifying these “taxation nodes,” we develop bypass strategies that neutralize the adversary’s financial leverage.
- Resource Sovereignty: We audit artisanal and strategic mineral chains (Gold/Lithium/Cobalt) to ensure they are formalized and secured under the administrative core, stripping the “Dark-State” of its primary funding baseline.
Kinetic & Territorial (KT) Auditing
Security is not measured by the number of boots on the ground, but by the security of the “Logistical Oxygen.”
- Arterial Hardening: We identify the primary transit arteries essential for urban survival and implement the “Mosaic Guard” model—decentralized, autonomous units capable of securing choke points without reliance on a vulnerable central command.
- Proactive Sovereignty: Our audit ensures that security forces move from a garrison-based defensive stasis to an active patrol-and-administration model, preventing the “Villages-to-Cities” inversion.
Cyber-Kinetic Resilience
The most sophisticated threat to modern infrastructure is the seizure of the Human-Machine Interface (HMI).
- SCADA Hardening: We simulate HMI Ghosting attacks to identify vulnerabilities in water, power, and energy grids.
- Hardware Truth Integration: CommandEleven mandates the installation of mechanical, non-digital monitoring systems. These “Analog Backstops” provide immutable data that cannot be spoofed by remote malicious code, ensuring that the administrative core operates on reality rather than digital deception.
The #72/48 Resilience Protocol (The Core Standard)
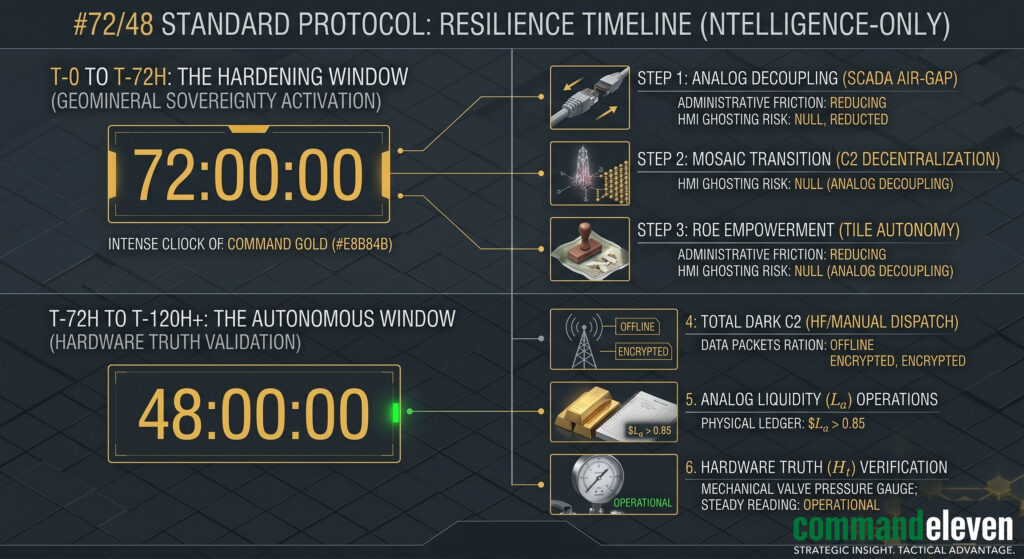
The #72/48 Protocol is the definitive operational standard for survival within the 45-day terminal window. It is the bridge between systemic failure and institutional persistence.
The 72-Hour Hardening Cycle
Upon the detection of an “Infrastructure Probe” or a significant spike in the Conflict Premium, the administrative core initiates a 72-hour transition to High-Friction Mode.
- Analog Decoupling: All critical infrastructure is disconnected from global digital networks to prevent remote seizure.
- Mosaic Transition: Centralized command is dissolved into pre-authorized, autonomous “tiles.” Each tile assumes responsibility for its localized judicial, logistical, and security outcomes.
- Physics-Based C2: Communication shifts to non-networked, high-frequency, or manual dispatch protocols.
The 48-Hour Autonomous Window
Once the hardening cycle is complete, the core must demonstrate the ability to maintain Total Dark Operations for a minimum of 48 hours.
- Sustained Persistence: The entity must operate without central instructions, digital banking, or external supply replenishment.
- Manual Override Sovereignty: All energy and logistical assets are managed via manual overrides. Localized markets are stabilized using pre-positioned Analog Liquidity ledgers.
- The Goal: To prove to both the populace and the adversary that the administrative core is unshakeable. By surviving the 48-hour “Flash-Dark,” the state or corporation breaks the 45-day velocity of collapse and forces the adversary into a protracted—and therefore loseable—kinetic engagement.
Implementing the Mosaic Defense
Traditional security models rely on a hierarchical, centralized command-and-control (C2) architecture. While efficient in high-stability environments, this “monolithic” structure is inherently brittle. The Mosaic Defense is the CommandEleven alternative—a decentralized administrative and security framework designed to prevent a single point of failure from inducing systemic collapse.
The “Tile” Concept
In a Mosaic Defense, the administrative core is broken down into autonomous, hardened “tiles.” Each tile (representing a regional hub, a critical facility, or a corporate division) is equipped with its own:
- Independent Resource Sovereignty: Localized access to fuel, power, and Analog Liquidity.
- Autonomous Rules of Engagement (ROE): Pre-authorized protocols for security and legal adjudication that do not require central validation.
- Redundant Communication: Non-networked C2 that functions only within the tile’s perimeter and its immediate neighbors.
Breaking the Cascade
The primary function of the mosaic is to contain the “Administrative Contagion.” If one tile falls—whether through kinetic capture or HMI Ghosting—the neighboring tiles are designed to “air-gap” immediately. This prevents the high-velocity cascade that typically characterizes the 45-day rupture window. The mosaic ensures that the entity remains operational, albeit in a fragmented state, denying the adversary the “monolithic victory” they require to formalize a Dark-State.
Case Studies – Clinical Applications of Resilience
To demonstrate the efficacy of the CommandEleven methodology, we examine two definitive 2026 interventions where the #72/48 Protocol and Mosaic Defense were activated.
The Savannah Buffer (Northern Ghana)
In early 2026, as the “Bamako Blueprint” was being exported southward, northern Ghana faced a series of coordinated “Infrastructure Probes.”
- The Threat: Non-state alliances targeted the transit corridors from the port of Tema to the landlocked interior.
- The Intervention: CommandEleven assisted regional hubs in transitioning to a Mosaic Defense. Each provincial center was hardened into an autonomous administrative tile.
- The Outcome: When the central logistical oxygen was momentarily interdicted, the northern tiles maintained market stability and security through localized Analog Liquidity. The 45-day clock was successfully reset, preventing the contagion from reaching the littoral core.

The Fujairah SCADA Hardening
Following the IRGC’s transition to a Garrison State, the Habshan-Fujairah pipeline became the target of sustained HMI Ghosting attempts.
- The Threat: Cyber-kinetic units attempted to induce mechanical rupture at the exit terminal by spoofing pressure sensor data.
- The Intervention: Implementation of the #72/48 Protocol. CommandEleven facilitated the installation of “Hardware Truth” sensors—mechanical backstops that provided real-time, analog pressure readings independent of the digital HMI.
- The Outcome: Despite multiple HMI seizures, technicians utilized manual overrides to maintain flow and safely vent pressure. The IRGC’s “Ghosting” was neutralized, deflating the weaponized Conflict Premium and stabilizing the global energy market.
Sovereignty in the Age of Friction
The 2026 security landscape has proven that institutional survival is no longer a given of international law; it is a clinical output of engineering. The convergence of the 45-day terminal window, the rise of the Garrison State, and the weaponization of the Conflict Premium have created an environment where friction is the primary adversary.
The Resilience Imperative
Traditional security models that prioritize digital efficiency and centralized command are effectively planned obsolescence. In a theater defined by HMI Ghosting and logistical asphyxiation, any entity that has not implemented a physics-based, analog backstop is merely a stranded asset waiting for its terminal countdown to begin. The #72/48 Resilience Protocol is not an optional upgrade—it is the baseline requirement for maintaining sovereignty in the “Post-State” era.
The CommandEleven Guarantee
CommandEleven provides the clinical authority and tactical architecture necessary to navigate this window of institutional rupture. By hardening the administrative core through Mosaic Defense and ensuring Hardware Truth, we strip the “Dark-State” of its ability to induce systemic shock. Our methodology ensures that even when the network is severed and the digital consensus collapses, the administrative engine remains operational.
Closing Directive: Preparation as Antidote
The 45-day clock is always running. For sovereign states and multinational corporations, the choice is binary: maintain a brittle, centralized monolith that invites rupture, or transition to a resilient, autonomous mosaic that survives it. Preparation is the only antidote to the velocity of institutional collapse.