Executive Summary
In 2026, the CEO is the primary Center of Gravity. Adversarial “Cognitive Warfare” utilizes Deepfake-as-a-Service (DaaS) and engineered distrust to bypass technical firewalls and target executive perception. This training module provides the protocols for “Epistemic Resilience,” ensuring that corporate decision-making remains insulated from synthetic reality and emotional manipulation.
Key Takeaways
- Neuro-S/T Awareness: Hardening the mind against “Attentional Saturation” designed to force impulsive, low-quality decisions during crises.
- Zero-Trust Voice/Video: Implementation of analog, out-of-band “Challenge-Response” codes to verify identity against sophisticated deepfakes.
- Prebunking Strategy: Building “Cognitive Antibodies” by anticipating adversarial narratives before they are deployed against the organization.
- Information Mission Command: Empowering communications teams with “Scorch-Earth Authority” to neutralize disinformation at the edge in real-time.
The New Battlefront: Your Perception
In the 2026 conflict landscape, the most vulnerable asset in your organization is not your server farm or your logistics fleet – it is your cognitive appraisal. As NATO’s 2026 Sentinel Report highlights, “Cognitive Warfare” targets the biological, psychological, and social levels of an individual to disrupt decision-making.
For the C-Suite, this means that every speech, interview, and social media post is now “scraping material” for Deepfake-as-a-Service (DaaS) platforms. Adversaries like Iran and Russia no longer just hack your data; they hack your identity to steer your organization toward “Narrative Defeat.”
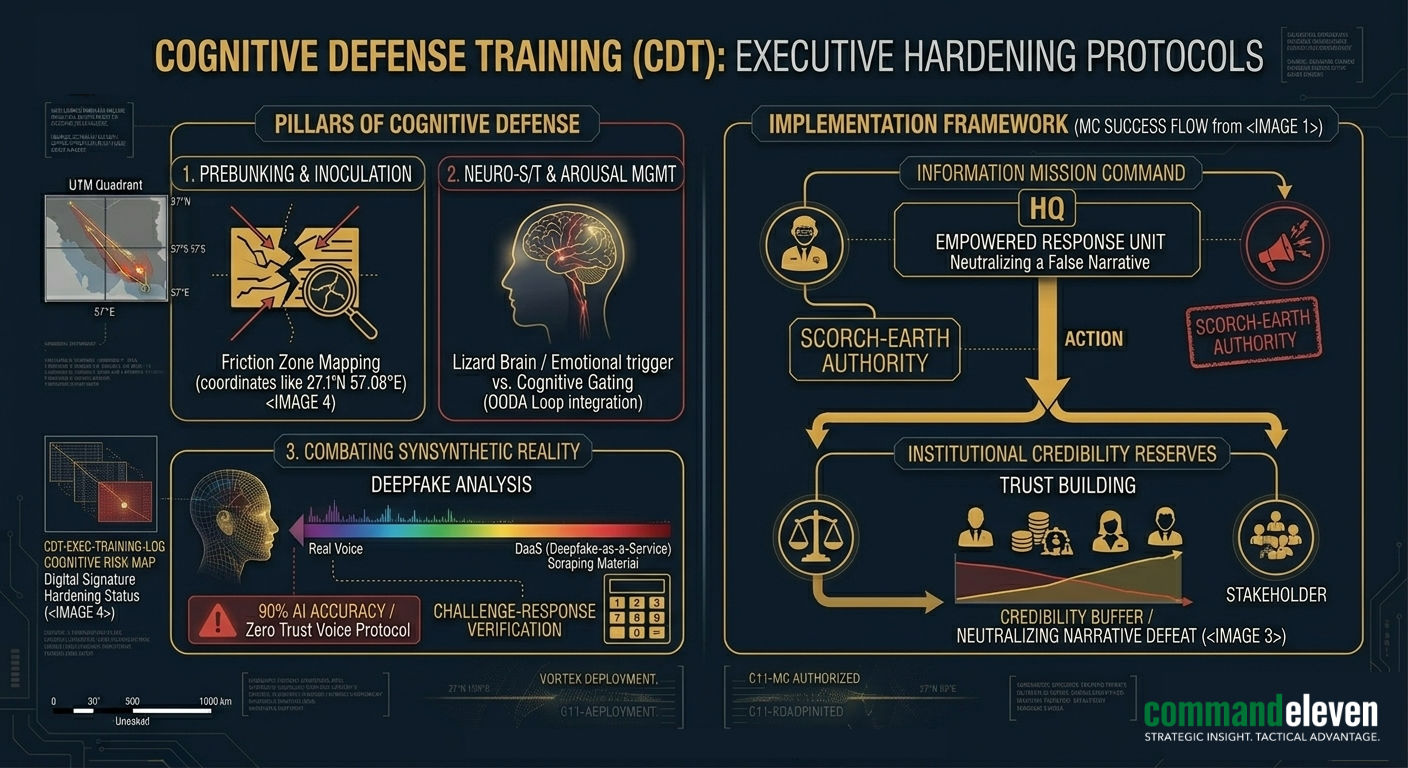
The Pillars of Cognitive Defense
Standard cybersecurity awareness training is obsolete. Cognitive Defense Training (CDT) focuses on “Information Hygiene” and “Epistemic Resilience.”
Prebunking & Inoculation
Rather than reacting to disinformation after it goes viral, CDT utilizes Prebunking. This involves exposing executives to weakened forms of manipulation techniques (e.g., “emotional framing” or “false dilemma” fallacies) to build cognitive antibodies.
- Executive Step: Pre-emptively map your organization’s “Friction Zones” (areas of known vulnerability, like recent layoffs or supply chain failures) and anticipate the adversarial narratives that will target them.
Neuro-S/T Awareness: Managing Arousal States
Adversarial operations use “Stress Induction” and “Attentional Saturation” to force executives into the Lizard Brain – where analytical processing is replaced by emotional reaction.
- Tactical Protocol: Implementation of “Cognitive Gating.” During a crisis (like a domestic aerial siege), executives must use pre-authorized decision templates to bypass emotional triggers and maintain OODA Loop velocity.
Combating Synthetic Reality (Deepfakes)
In 2025, AI-powered corporate impersonation attacks surged by 30%. By 2026, deepfake voices can bypass bank authentication and board-level video calls with 90% accuracy.
- The “Zero Trust” Voice Protocol: Never authorize high-magnitude decisions based on voice or video alone. Use an out-of-band Challenge-Response Code (a physical or analog verbal key) to verify identity.
Implementing “Mission Command” for Information
Just as we discussed in the Executive Crisis Management assessment, cognitive security requires a distributed leadership model.
- Information Mission Command: Empower your communications team to act as “Information Defenders.” Give them the authority to “Scorch-Earth” a false narrative immediately without waiting for a board-level review.
- Institutional Credibility Reserves: Trust is your strategic center of gravity. Transparency and consistent behavior create a “Credibility Buffer” that makes adversarial deepfakes harder to believe. If your stakeholders trust you, the lie cannot take root.
The 72-Hour Cognitive Hardening Checklist
To prepare for the imminent mediation failure, executives must harden their personal and professional digital signatures:
- Digital Footprint Minimization: Scrub high-resolution personal audio/video from public domains to reduce DaaS scraping material.
- Personal Out-of-Band (OOB) Keys: Establish a “Family & Executive” verbal code word for emergency identity verification.
- Cognitive Red-Teaming: Conduct a simulation where your team identifies how an adversary would use a deepfake of you to trigger a corporate or social cascade.
- Narrative Pre-Positioning: Draft “Truth-First” templates for your most likely failure points (JIT logistics, fuel surges) so you aren’t drafting from a place of stress when the crisis hits.
Conclusion: Resilience is a Choice
Cognitive warfare is a “trust exploitation” game. The adversary wins when you stop trusting your data, your team, and your own judgment. By treating Cognitive Security as a core operational requirement—on par with physical and cyber security—you ensure that your organization remains the “Center of Gravity” in a world of engineered distrust.