Executive Summary
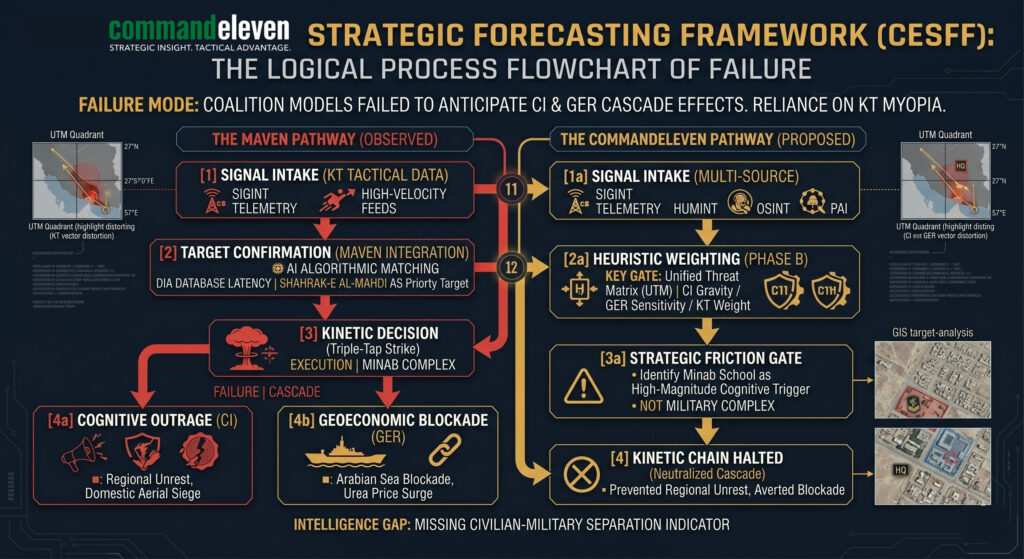
The CommandEleven Strategic Forecasting Framework (CESFF) provides a non-linear technical methodology for modeling global risk. Moving beyond traditional kinetic analysis, the CESFF utilizes the Unified Threat Matrix (UTM) to identify the “Forced Convergence” of Kinetic, Cyber, Geoeconomic, and Cognitive vectors. This framework allows decision-makers to anticipate cascading failures before they reach systemic saturation.
Key Takeaways:
- Vector Weighting: Traditional models over-prioritize kinetic data; CESFF balances this with sub-threshold cyber and cognitive triggers.
- The UTM Pivot: Every regional event is a multi-domain incident; a strike in the Gulf is simultaneously a domestic cyber and economic event.
- Forecast Failure Modes: Analyzing Operation Epic Fury reveals that database latency and lack of cultural-cognitive indicators are the primary drivers of strategic surprise.
- Strategic Superiority: Success is defined by the ability to identify “Friction Zones” where adversarial intent meets institutional vulnerability.
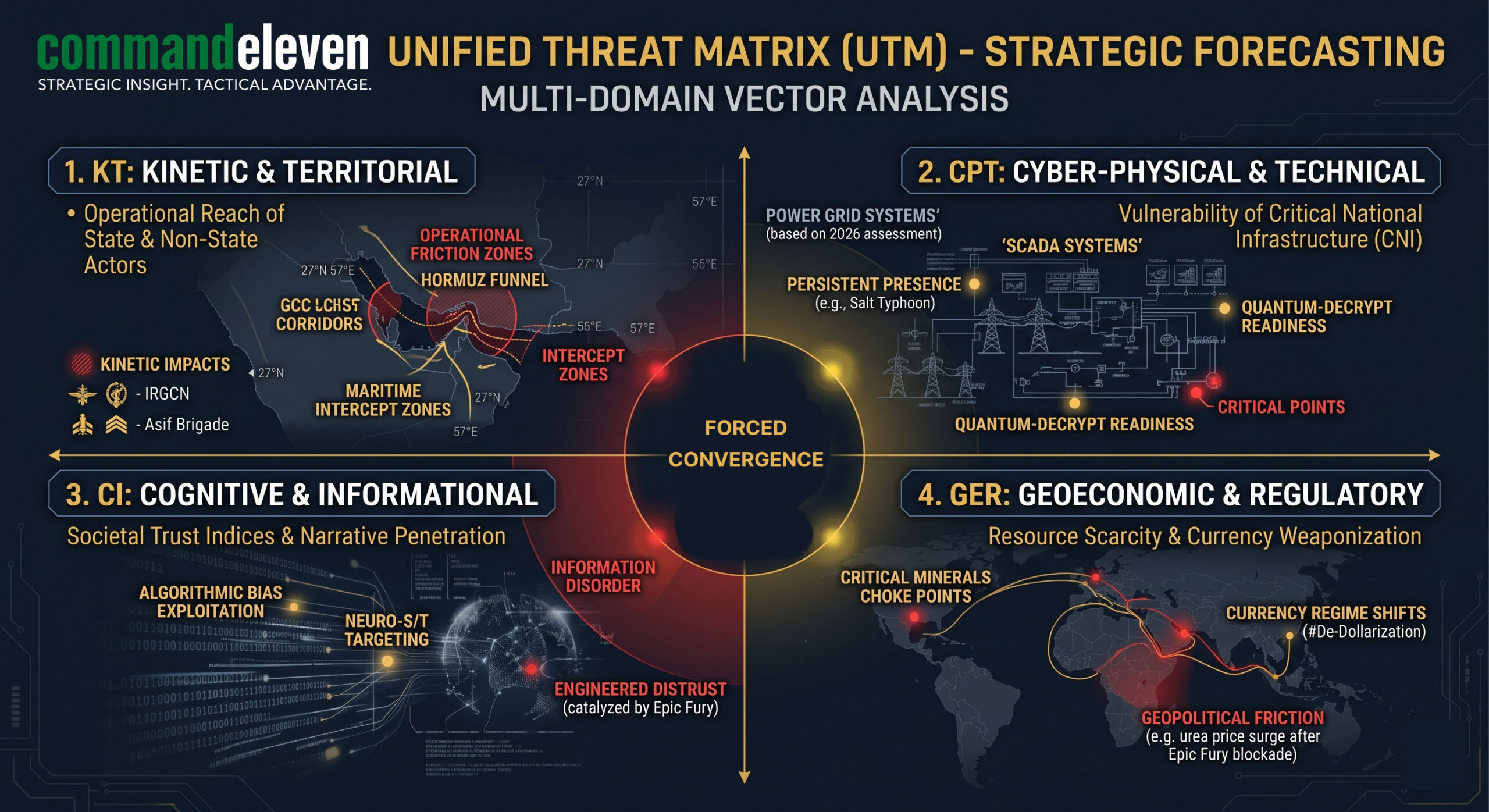
The Unified Threat Matrix (UTM): A Vector-Based Approach
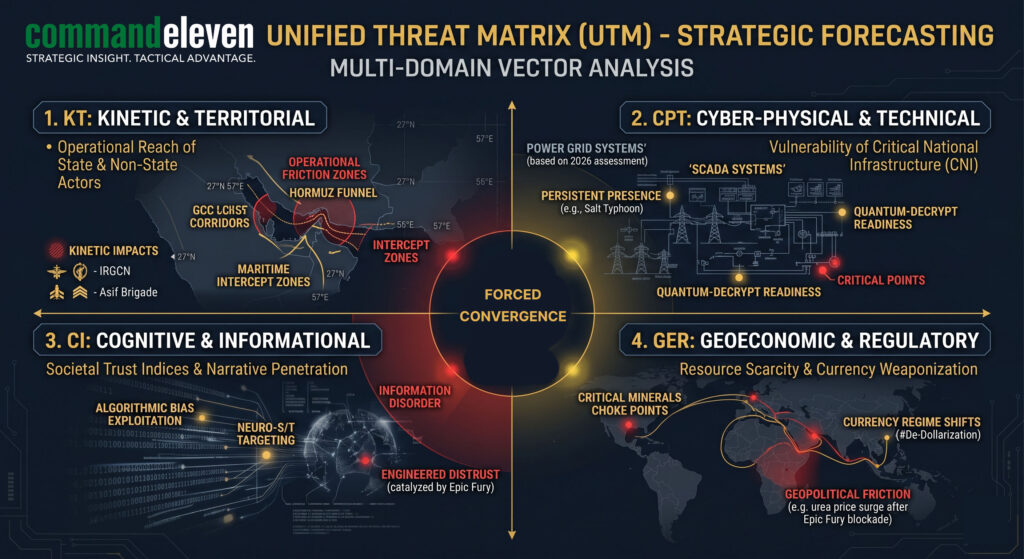
To achieve high-fidelity forecasting, CommandEleven rejects the siloed analysis of “Geopolitics” or “Cybersecurity” as separate entities. Instead, we utilize a vector-based model that weights four distinct but overlapping domains.
- Kinetic & Territorial (KT): Traditional force projection, maritime intercept zones, and insurgent activity.
- Cyber-Physical & Technical (CPT): The integrity of SCADA systems, telecommunications backbones, and quantum-resistant encryption.
- Cognitive & Informational (CI): Narrative penetration, algorithmic bias, and the manipulation of societal trust.
- Geoeconomic & Regulatory (GER): Resource-based conflict, supply chain weaponization, and currency-regime shifts.
The Signal-to-Noise Filtration Process
The primary challenge in 2026 is not the lack of data, but the “Information Deluge.” CommandEleven employs a three-phase filtration process to extract actionable intelligence from the global data stream.
Phase A: Multi-Source Intake (MSI)
We operate under a zero-trust data protocol. Intelligence is gathered via SIGINT telemetry from contested zones, HUMINT field reports from verified assets, and OSINT/PAI linguistic analysis.
Phase B: Heuristic Weighting
Every signal is passed through an algorithmic weighting system. A signal’s Criticality Score is not just its probability, but its proximity to a predefined “trigger point” and its potential magnitude of disruption.
Criticality = (P X M) x log(Pr)
Phase C: Adversarial Red-Teaming
Forecasts are subjected to “Shadow Analysis,” where internal teams simulate adversarial responses from actors like the IRGC or TTP to ensure the model accounts for non-rational escalation.
Case Study: Operation Epic Fury – The Forecasting Breakdown
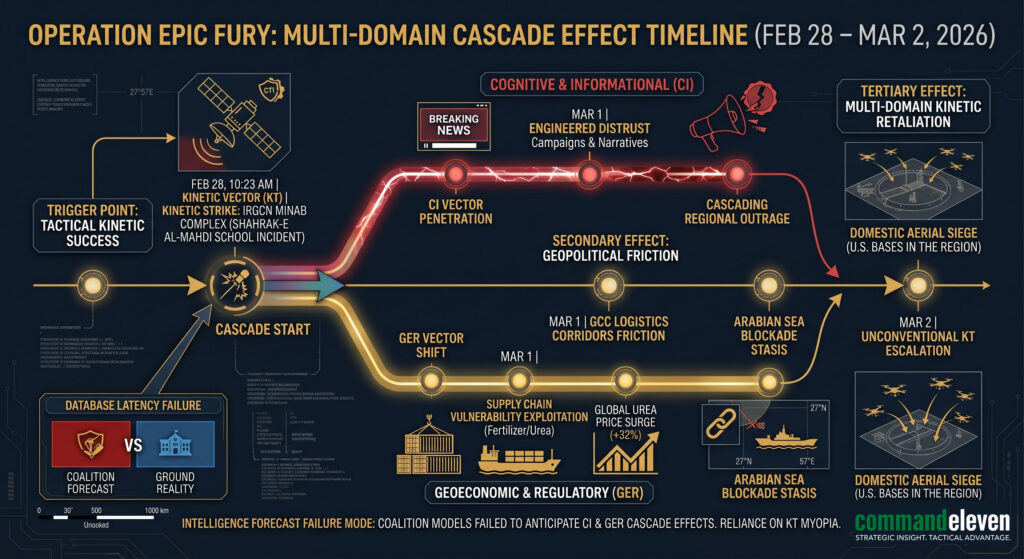
Operation Epic Fury serves as the definitive example of the “Forecasting Gap” in modern warfare. While the operation achieved immediate kinetic success, the failure to forecast the non-linear “Cascade Effect” led to a strategic net loss.
The Strategic Myopia
The operation prioritized the Kinetic (KT) vector (neutralizing an Iranian educational facility and naval assets) but failed to weight the Cognitive (CI) and Geoeconomic (GER) repercussions. The predictive models used by the coalition failed to identify that the target—while tactically valid—held a “Cognitive Gravity” that would catalyze regional proxy groups.
The Cascade Effect: From Hormuz to the Home Front
The forecasting failure manifested in two primary waves:
- The Hormuz Blockade: The failure to anticipate the immediate shift in the GER vector led to the maritime stasis in the Arabian Sea, crippling logistics corridors.
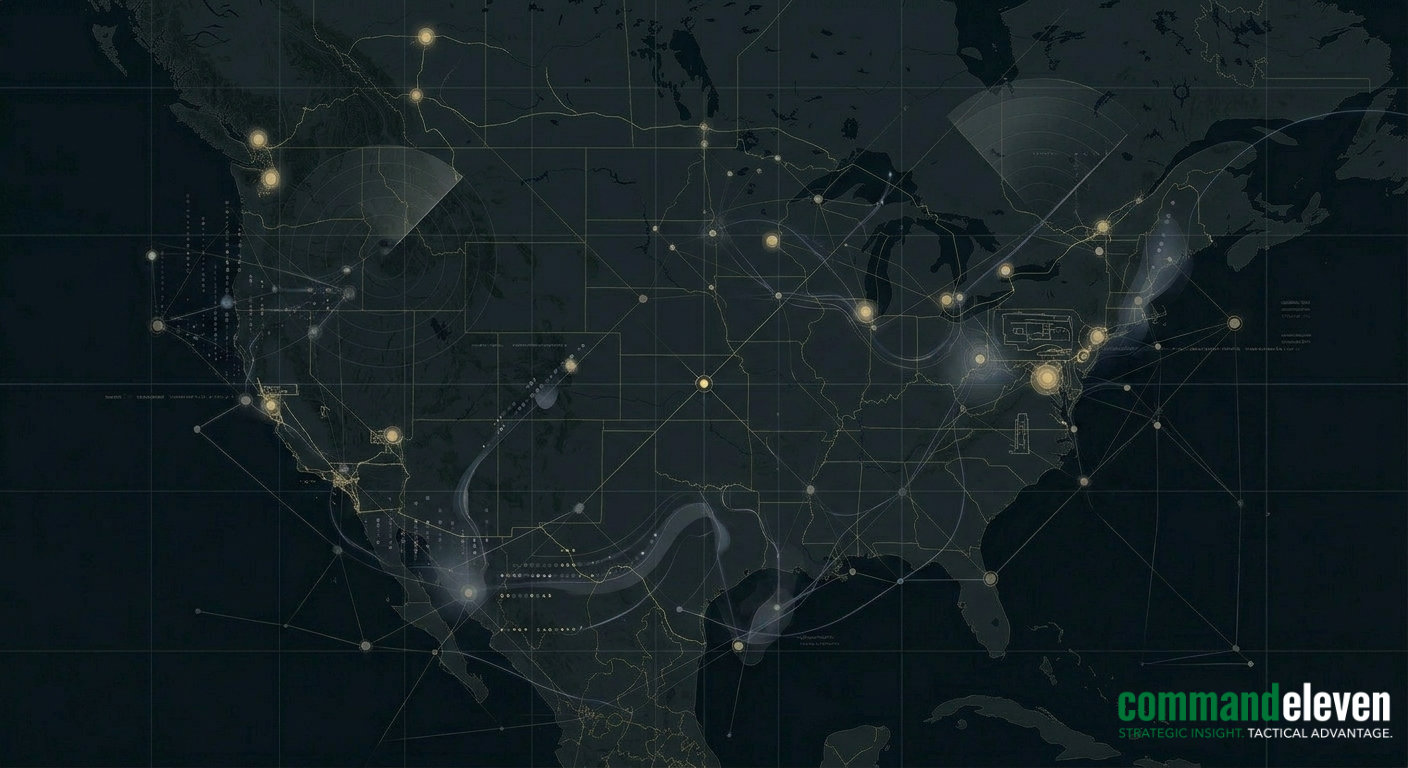
- The Domestic Aerial Siege: The most significant oversight was the inability to forecast the CI-to-KT transition. The “Cognitive” outrage triggered by the strike fueled the domestic aerial drone siege of U.S. military bases, effectively bringing the conflict to the home front.
Anticipatory Defense: The 2026–2030 Horizon
The CommandEleven methodology provides the framework to avoid the failures seen in Epic Fury. By utilizing the UTM, we move from “Post-Event Reaction” to “Pre-Event Posturing.”
- Weighted Decoupling: Separating tactical data from strategic significance.
- Cross-Domain Trigger Mapping: Identifying how a strike in one domain (e.g., Cyber) will manifest as a crisis in another (e.g., Geoeconomic).
- Temporal Depth: Forecasting not just the first-order strike, but the second- and third-order retaliatory loops.
Conclusion
Strategic Intelligence Forecasting in 2026 requires the rejection of certainty in favor of probability and weighted impact. The CommandEleven methodology ensures that senior decision-makers are not merely reacting to the “Epic Furies” of the future, but are positioned to neutralize the vectors before they converge.