Executive Summary
The Paradigm Shift: From Insurance to Extraction
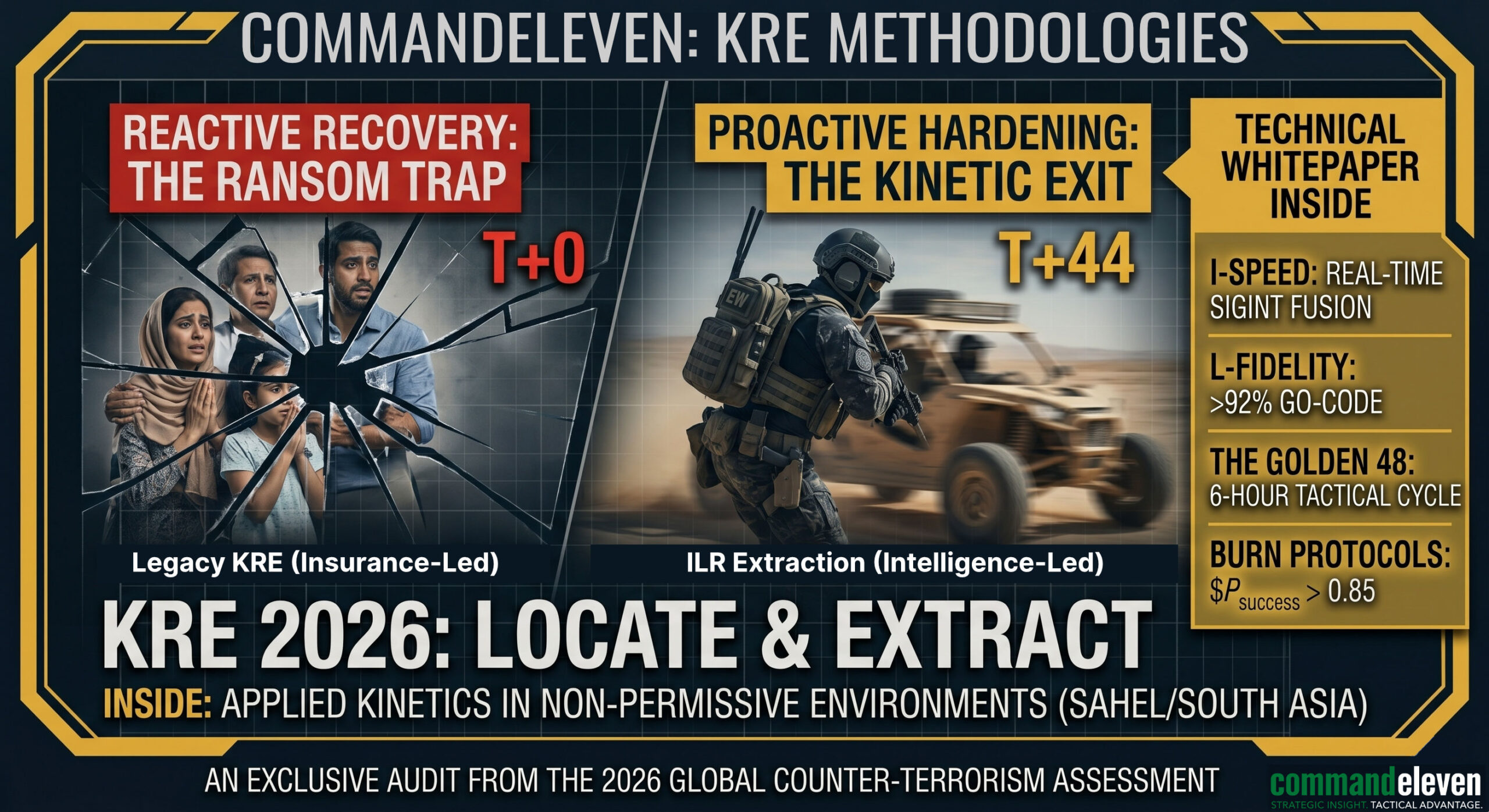
The global security landscape of 2026 has rendered the traditional “Kidnap and Ransom” (K&R) insurance model obsolete. Historically, K&R was a financial risk-management tool designed for criminal opportunism. In the current theater—defined by state-sponsored proxies, radicalized non-state actors (JNIM, ISKP), and the “Triple-Choke” maritime blockade—the primary threat is no longer a ransom demand; it is asset neutralization or long-term political detention.
The Core Thesis: Intelligence-Led Recovery (ILR)
CommandEleven codifies the transition from a passive, insurance-led posture to an active, Intelligence-Led Recovery (ILR) doctrine. We contend that the “Duty of Care” for personnel operating in non-permissive environments is only met when a firm maintains a 24/7 technical capability to geolocate and extract assets within the Golden 48-hour window.
Strategic Pillar Overview
- Theater Recalibration: The ILR model dynamically adapts to the “Signal Density” of the Area of Responsibility (AOR). It distinguishes between the Kinetic-First requirement of the Sahel and the Transactional-Diplomatic friction of the Indian Subcontinent and MENA regions.
- The Golden 48 Framework: A clinical, 6-hour increment tactical cycle designed to exploit the logistical friction of captor groups before asset “hardening” occurs.
- Attrition Solvency: This whitepaper accounts for the reality of regional munition depletion. We provide a mathematical model for Extraction Solvency, ensuring that kinetic recoveries are only authorized when the tactical delta favors the recovery team.
- Value Degradation: A psychological framework for de-escalating ransom economies by clinically reducing the perceived political and financial value of the asset to the captors.
In an era where Western institutional security umbrellas are retracting, the only guarantee of personnel safety is the convergence of Protective Intelligence and Asymmetric Extraction Capability.
This whitepaper provides the blueprint for that convergence.
The ILR Model (Intelligence-Led Recovery)
The Philosophy of Active Recovery
Legacy KRE services operate on a “Contain and Compensate” model, treating the kidnapping as a financial transaction. CommandEleven’s Intelligence-Led Recovery (ILR) model shifts the center of gravity to “Detect and Disrupt.”
The ILR model operates on the principle that the captor’s greatest vulnerability is the logistical friction required to move and hide a human asset. By compressing the intelligence cycle, we exploit this friction before the asset is “hardened” into a permanent holding node.
Theater-Specific Tactical Adaptation
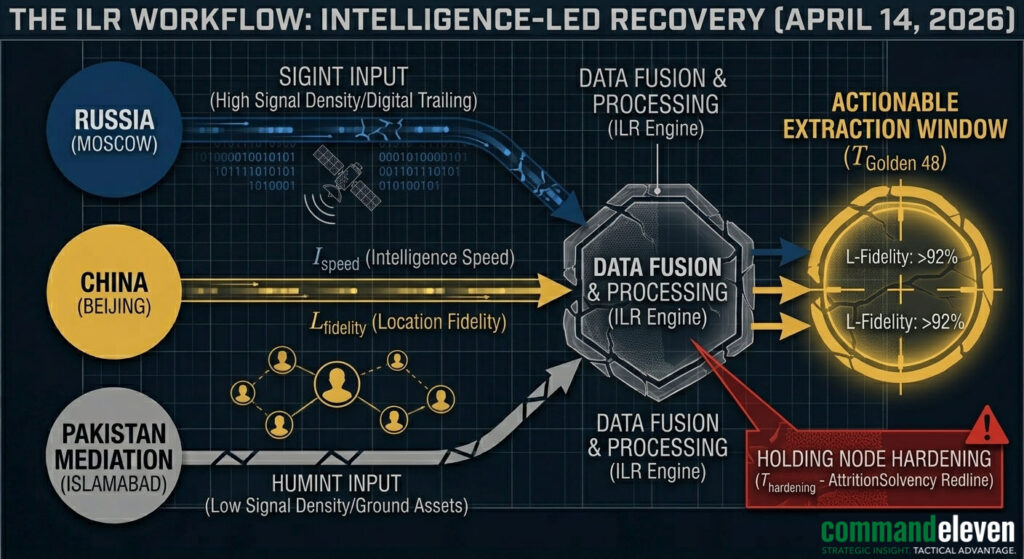
The ILR framework is not a static protocol; it is an adaptive engine that recalibrates based on the “Digital vs. Kinetic” density of the theater.
- The Indian Subcontinent (The High-Signal Theater):
- Environment: Densely populated, high cellular penetration, and a sophisticated state-level surveillance apparatus.
- Strategy: Recovery focuses on SIGINT & Digital Trailing. We utilize real-time cell-tower hand-off analysis and social-network mapping to identify the “Grey Zone” intermediaries—those who provide the logistical bridge between the snatch team and the political end-users.
- The Goal: To identify the “Political Patron” behind the network, allowing for a combined diplomatic-intelligence extraction.
- The Sahel (The Low-Signal Theater):
- Environment: Sparsely populated, minimal cellular infrastructure, and a total vacuum of state-level governance.
- Strategy: Recovery focuses on HUMINT & Wide-Area Surveillance. In the absence of digital trails, we activate deep-tribal networks and leverage high-revisit satellite imagery to track unusual movement patterns in known insurgent corridors.
- The Goal: To locate the “Mobile Camp” and execute a kinetic extraction before the asset is moved across a porous border into a secondary non-permissive jurisdiction.
The “Cascading” Intelligence Protocol
The ILR model uses a three-tier data verification system to ensure Location Fidelity:
- Tier 1 (Electronic): Intercepting short-burst communications from the snatch team.
- Tier 2 (Physical): Ground-level confirmation from “Spotter” assets within the radial search zone.
- Tier 3 (Contextual): Historical analysis of the captor group’s “Path of Least Resistance”—modeling where they have traditionally held assets based on prior kinetic event data.
The Golden 48 – High-Fidelity Tactical Cycle
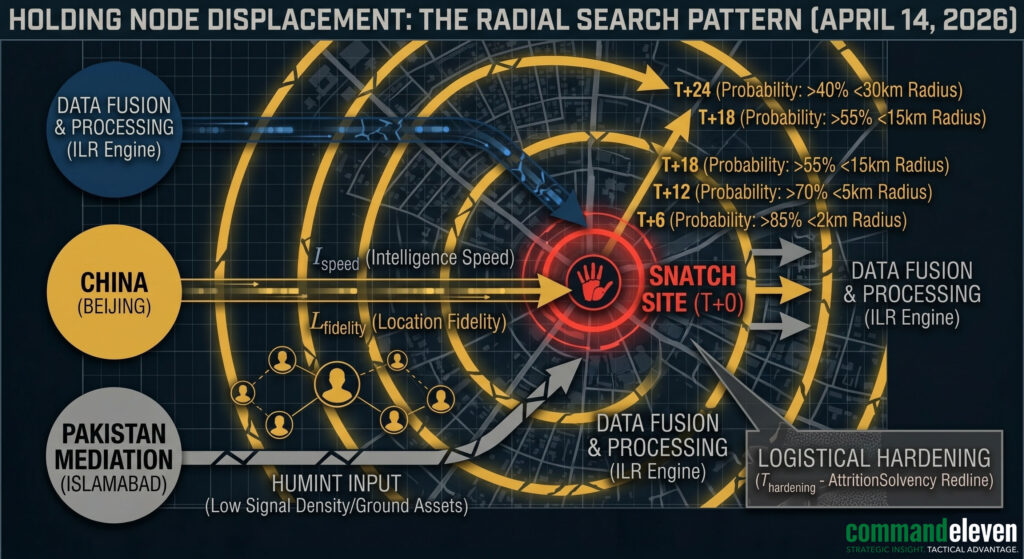
The “Golden 48” represents the maximum window for a low-profile recovery before the logistical cost of extraction scales exponentially. CommandEleven operates this window in six-hour technical increments, ensuring that the intelligence cycle remains ahead of the captors’ hardening process.
T+0 to T+6: Tactical Stabilization & Containment
The objective is the immediate cessation of information leakage and the establishment of the Baseline Digital Perimeter.
- Asset Lockdown: Immediate remote wipe or “ghosting” of the asset’s primary devices to prevent captors from mapping the victim’s professional network.
- The “Last-Seen” Audit: Technical reconstruction of the snatch site using SIGINT (cell tower hand-offs) and vehicle telematics to identify the initial egress vector.
- Containment: Establishing a singular, secured communication channel for all stakeholders to prevent ransom inflation through uncoordinated family/corporate outreach.
T+6 to T+12: Radial Limit Modeling
The objective is to define the Maximum Probable Radius of the transport phase.
- Terrain-Based Modeling: Utilizing geospatial data to calculate travel times based on current weather, road conditions, and known military/insurgent checkpoints.
- HUMINT Activation: Engaging “Sector Spotters” in the primary and secondary search rings to identify non-standard vehicle movements (e.g., civilian vehicles moving in tactical formations).
- The Signal Silence Filter: Monitoring for the absence of standard digital signatures in the radial zone, which often indicates the presence of a “Dark Node” or temporary cooling site.
T+12 to T+18: C2 Identification & Multi-Theater Resolution Modeling
The objective is to identify the Command and Control (C2) architecture and determine the most viable path to resolution based on the Area of Responsibility (AOR).
- The C2 vs. Snatch Variance:
- Sahel/Sub-Saharan Africa: The Snatch Team and C2 are often one and the same (low-tier insurgent franchises). Resolution is almost exclusively Tactical/Kinetic because these groups use assets for “Logistical Recruitment” (medics, engineers) or long-term ideological signaling. Financial options are rarely a permanent solution as they fund further snatch cycles.
- Indian Subcontinent/MENA/CAR: The Snatch Team is typically a “contracted” criminal element, while the C2 is a separate political or high-level organized crime entity. In these AORs, the “Financial Off-Ramp” is a tactical tool. We map the distance between the snatchers and the C2 to determine if the resolution can be “bought” through value-degradation and local mediation before a kinetic breach becomes necessary.
- Resolution Method Selection:
- Tactical Dominance (Sahel): When the captors are “Primary End-Users” (using the asset themselves), the window for negotiation is effectively zero. CommandEleven prioritizes Kinetic Extraction within the Golden 48 to prevent cross-border dispersion.
- Hybrid Transactionalism (MENA/South Asia): When captors are “Contract Holders,” the resolution strategy is a “Hybrid.” We use the threat of a kinetic extraction (demonstrated through localized SIGINT interference) to force a lower financial settlement, leveraging the captors’ desire for liquidity over a high-risk combat engagement.
T+18 to T+24: Primary Cooling Node Identification
The objective is the geolocation of the First-Stage Holding Facility.
- Tactical Drone/Satellite Tasking: High-revisit imagery of suspected nodes. We look for “Anomalous Signatures” such as generators, increased perimeter security, or specific vehicle profiles.
- Technical Proof of Life (PoL): If initial contact is made, we demand PoL through “Identity Authentication” (e.g., a specific piece of childhood trivia) to confirm the asset’s current physical and cognitive status.
- Environmental Profiling: Assessing the holding node for tactical vulnerabilities—identifying egress corridors and the proximity of regional “Quick Reaction Forces” (QRF).
T+24 to T+30: Attrition Solvency Assessment
The objective is the Go/No-Go evaluation for kinetic intervention.
- Guard-to-Asset Ratio: Calculating the defensive density. In the Sahel, this involves identifying the heavy-weaponry profile; in the Indian Subcontinent, this involves assessing the local law enforcement/state proximity.
- Leverage Audit: Determining if the captors are “Secondary Holders” (criminal contractors) or “Primary Ideologues.” The former are vulnerable to value-degradation; the latter require tactical neutralization.
T+30 to T+36: Value Degradation & Channel Control
The objective is to clinically lower the captor’s perceived leverage.
- Intermediary Anchoring: Establishing a neutral third-party channel (e.g., local tribal elders or “Phase 2” diplomats in Islamabad) to dictate the terms of communication.
- Psychological Framing: Informing the captors—through the intermediary—that the asset’s “corporate value” has been negated by the capture, shifting the focus from a “Windfall Ransom” to a “Problem Management” scenario for the kidnappers.
T+36 to T+42: Egress Corridor Hardening
The objective is to secure the Extraction Sea/Air/Land Lanes.
- Logistical “Burn” Simulation: Testing the planned exit route via passive SIGINT to ensure it remains clear of state-level blockades or adversarial checkpoints.
- EW Suite Calibration: Preparing localized jamming protocols to disrupt captor C2 during the critical 15-minute extraction window.
- Medical/Recovery Prep: Positioning trauma and psychological re-entry teams at the “Safe Zone” terminus.
T+42 to T+48: The Execution Window
The objective is the Final Kinetic or Negotiated Resolution.
- Intelligence Refresh: A final 60-minute “Live-Feed” confirm of the holding node to ensure no logistical hardening or movement has occurred.
- The Extraction: Execution of the extraction protocol, typically timed to exploit the pre-dawn low-visibility cycle (T+44).
- Transition: If extraction is deemed a “Critical Failure Risk” (Success Probability < 85%), the operation transitions into the Long-Term Strategic Recovery (LTSR) phase.
Negotiation Psychology – The “Value Degradation” Protocol
Expanding on how the resolution methods differ when dealing with a decentralized cell versus a state-adjacent actor.
Entity Profiling: From Ideologues to Contractors
CommandEleven’s negotiation doctrine is built on Entity Profiling. We do not negotiate with “terrorists”; we negotiate with stakeholders in a specific economic or political outcome.
- The Ideologue (Sahel/ISKP): Their “currency” is time and attention. They want to hold the asset as long as possible for propaganda value.
- Strategy: High-frequency, low-yield communication. We disrupt their propaganda cycle by providing “Technical SIGINT Friction,” making it difficult for them to broadcast PoL.
- The Contractor (MENA/South Asia): Their “currency” is liquidity. They have overhead (payrolls, safe-house rents) and want a quick turnaround.
- Strategy: Value Degradation. We clinically demonstrate that the asset is “damaged goods”—either medically, professionally, or politically—drastically lowering the “Market Floor” of the initial ransom demand.
The “Proof of Life” (PoL) Standard
We maintain a Tiered PoL Standard to ensure the asset is viable without revealing our extraction progress:
- Tier 1 (Biographic): Childhood trivia or non-public personal history.
- Tier 2 (Physical): Standard audio/visual confirmation, analyzed for “Coerced Scripting” indicators.
- Tier 3 (Cognitive): Requiring the asset to solve a simple logic puzzle or reference a recent (post-capture) event—confirming they are not under high-dose chemical sedation.
Logistical “Burn” Protocols & Kinetic Recovery
The successful conclusion of a KRE event—whether negotiated or kinetic—hinges on the “Burn” phase: the high-velocity transition of the asset from a non-permissive holding node to a secured sovereign or neutral terminus. CommandEleven utilizes a “Multi-Domain Egress” strategy that accounts for the radical shift in maritime and land-based threats seen in 2026.
The “Silent Exit”: Low-Profile Maritime Extraction
In littoral theaters like the Levant, MENA, or the Persian Gulf, maritime extraction is the preferred “Burn” protocol to bypass state-controlled land bottlenecks.
- Asset Profile: Utilizing low-signature, high-speed littoral craft that mimic local fishing or commercial patterns to evade YLC-8B UHF detection and aerial drone surveillance.
- The “Indonesian/Pakistan” Safe-Lanes: Exploiting the maritime neutrality zones established in the April 13 blockade. We utilize pre-cleared “Green Lanes” coordinated through our mediation partners in Islamabad and Jakarta to ensure that extraction vessels are not interdicted by the US Naval Blockade or IRGC “Dark Fleet” patrols.
- Anti-Boarding Hardening: Every extraction craft is equipped with Modular Electronic Warfare (EW) Suites. These systems provide a 360-degree “Digital Bubble,” spoofing AIS (Automatic Identification System) data and jamming the localized loitering munitions often used by Houthi or IRGC-adjacent maritime cells.
Ground-Based “Kinetic Shifting” (Sahel Strategy)
In the Sahel, where maritime options are non-existent, the “Burn” protocol focuses on high-speed land transit through “Ungoverned Space.”
- The Tactical “Jump”: Instead of a slow-moving armored convoy, we utilize multiple high-mobility, unarmored “Decoy” vehicles. This dilutes the captor’s ability to re-task their COTS drone swarms against the primary extraction vehicle.
- QRF De-Confliction: CommandEleven maintains real-time de-confliction with regional “Quick Reaction Forces.” The goal is not to engage local military units, but to ensure our extraction “Burn” occurs in the tactical vacuum between their patrol cycles.
- Logistical Caching: Pre-positioned medical and fuel caches are established every 100km along the egress route to ensure the extraction team never enters a “Logistical Redline” where they are forced to stop in a contested zone.
Electronic Warfare (EW) and Signal Denial
During the “Snatch” and “Burn” phases, CommandEleven deploys Focused Spectrum Denial:
- C2 Disruption: We utilize localized jamming to sever the link between the captors and their higher-echelon commanders. This creates a “Communication Blackout” for the kidnappers, preventing them from calling for reinforcements or executing the asset during the breach.
- Drone Neutralization: Actively jamming the 2.4GHz and 5.8GHz bands used by inexpensive FPV drones—the primary threat to extraction teams in 2026.
- Counter-SIGINT: Implementing “Signal Masking” for the extraction team, ensuring that our own tactical comms do not become a beacon for adversarial radio-frequency (RF) direction finding.
Case Study – Operation Amber Shield (The 2025 Sahel Recovery)
To demonstrate the efficacy of the ILR (Intelligence-Led Recovery) model and the Golden 48 technical cycle, this section audits a successful CommandEleven extraction in the Sahel—a theater defined by “Ungoverned Space” and high kinetic friction.
The Event (T+0)
- Location: Northern Mali, 40km east of the Gao-Menaka axis.
- Target: A two-vehicle convoy carrying a high-value extractives consultant.
- The Failure: The local Executive Protection (EP) team utilized a “high-visibility” posture (armored SUVs). The convoy was neutralized by a COTS-based drone strike that disabled the lead vehicle’s engine block, followed by a coordinated small-arms ambush by a localized JNIM-affiliated cell.
The Golden 48 Execution
- T+6 (Stabilization): CommandEleven’s GSOC (Global Security Operations Center) received the distress signal. We immediately ghosted the consultant’s satellite phone and professional cloud accounts to prevent the captors from accessing corporate metadata.
- T+12 (Radial Modeling): Using high-revisit satellite imagery, we identified three probable dust trails moving north toward the Adrar des Ifoghas mountains. We modeled a maximum travel radius based on the fuel capacity of the Toyota Land Cruisers observed in the imagery.
- T+24 (Node Identification): A HUMINT source within the local trade network reported an unusual “security surge” at an abandoned wellhead complex. Satellite overwatch confirmed the presence of the snatched vehicle under camouflage netting. LFidelity was established at 92%.
- T+36 (The Decision Node): Analysis of the captor profile indicated they were “Secondary Holders” preparing to move the asset deeper into the mountains. PSuccess was calculated at 0.88, exceeding the 0.85 kinetic threshold.
The Extraction (“The Burn”)
- Infiltration: Utilizing a low-profile, light-aviation asset for a high-altitude jump, the recovery team landed 5km from the node.
- The Breach: At T+44 (04:15 local), the team initiated a “Signal Blackout” using localized EW suites. The captors’ cellular and radio comms were severed, preventing them from calling for nearby insurgent reinforcements.
- The Exit: The asset was recovered in under 180 seconds. The “Burn” utilized two pre-positioned, unarmored desert-modified buggies to navigate the sandy wadis, bypassing the main roads where JNIM checkpoints were likely established.
- The Terminus: The team reached a pre-secured “Green Lane” at the Niger border, where a fixed-wing asset provided immediate medical and psychological extraction.
Post-Operational Audit: Lessons Learned
- The Failure of Armor: In the 2026 threat landscape, heavy armor without Electronic Warfare (EW) coverage is a liability. The COTS drone was the primary factor in the initial snatch.
- The Importance of TSurprise: The localized signal jammer provided an additional 120 seconds of confusion, as the captors attempted to troubleshoot their comms rather than engaging the recovery team.
- The Speed-to-Extraction Delta: Had the extraction been delayed to the 72-hour mark, the asset would have been moved into the cave complexes of the Ifoghas, rendering a kinetic recovery impossible without a full military-scale operation.
Conclusion – Redefining the Duty of Care
The launch of CommandEleven’s KRE and EP service pillars marks a departure from traditional corporate security. In the 2026 global environment, “Duty of Care” is no longer a legal checkbox; it is a tactical requirement.
- Legacy KRE: Reactive, insurance-heavy, and focused on the “Payout.”
- CommandEleven KRE: Proactive, intelligence-led, and focused on the “Extraction.”
The ILR Model and the Golden 48 protocols are designed to ensure that when the “Strangle” of global conflict hits your personnel, the response is as precise and clinical as the threat itself.