Executive Summary: The Institutional Paralysis
The 2026 security environment is characterized by a systemic failure of Western institutional security architectures. The “Stability-Operations” model, which relied on state-centric partnerships and high-altitude technical dominance, has collapsed in the face of decentralized, asymmetric “Gray Zone” threats. This audit identifies the Capability-Intent Gap as the primary driver of Western obsolescence in the Sahel and South Asian theaters, necessitating a transition to agile, intelligence-led recovery models.
The Sahelian Vacuum: A Post-Western Reality
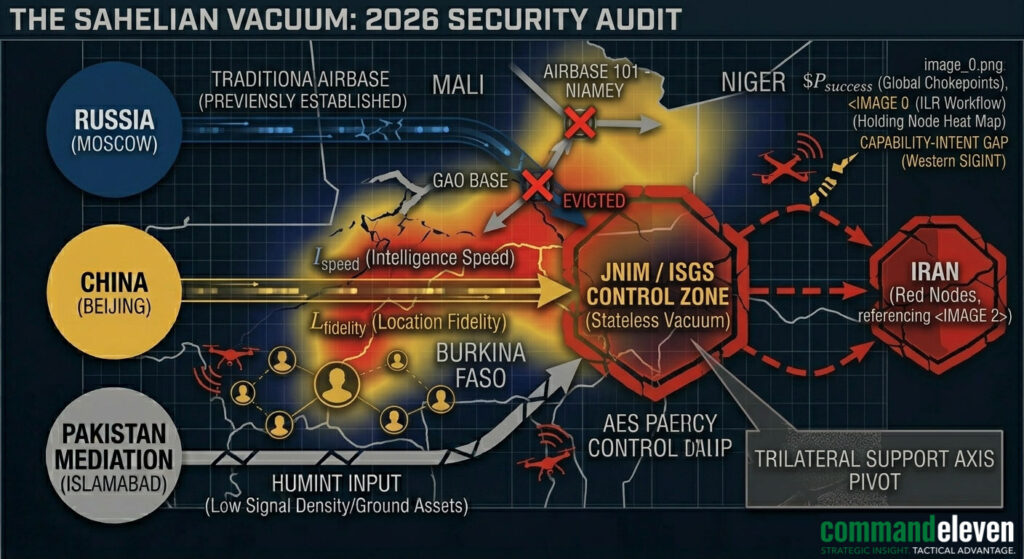
The withdrawal of the United States and France from the Liptako-Gourma region has transitioned the Sahel from a monitored conflict zone to a Stateless Vacuum.
The Eviction of Institutional Intelligence
The systemic collapse began with the military-led “Alliance of Sahel States” (AES) pivoting toward the Trilateral Support Axis (Russia, China, Iran). The resulting eviction of Western assets—specifically from Airbase 101 and the Gao hub—has blinded Western SIGINT capabilities.
Insurgent Consolidation (JNIM/ISGS)
Without Western kinetic deterrence, JNIM and ISGS have achieved administrative control over 60% of Burkina Faso and significant sectors of Mali. They have successfully integrated COTS (Commercial Off-The-Shelf) drone technology into their snatch-and-grab operations, rendering traditional unarmored EP convoys defenseless.
Diagnostic: For Western personnel remaining in-theater, the absence of a resident military QRF means that any security incident is, by definition, an “unsupported recovery.”
South Asian Predictive Failure: The Grey Zone
In South Asia, Western intelligence has failed not in presence, but in Cognitive Accuracy.
The Capability-Intent Gap
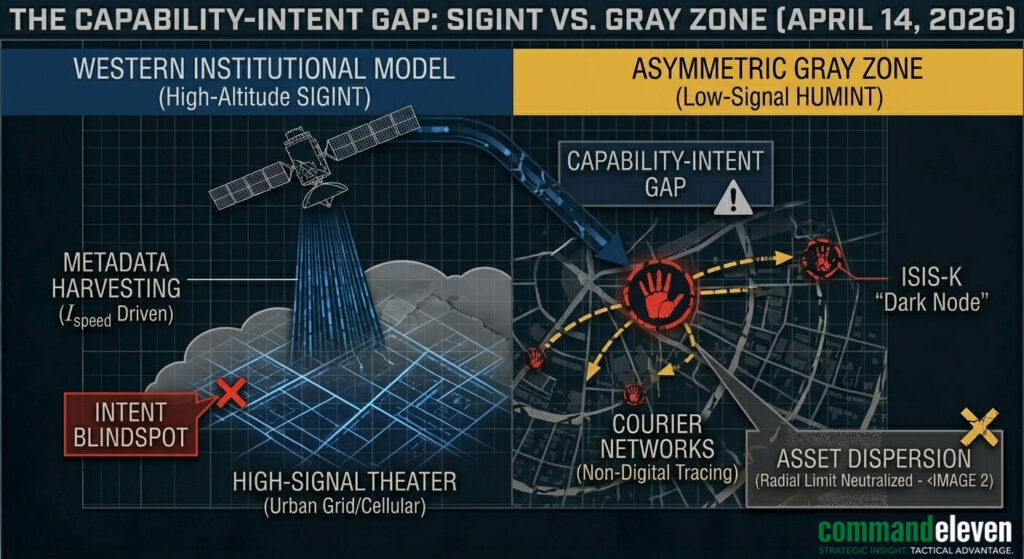
Western services remain over-reliant on High-Altitude SIGINT. While these sensors can track physical movement (Capability), they are demonstrably blind to the ground-level “Dark Nodes” utilized by ISIS-K and regional proxies. The use of non-digital courier networks and tunnel-based logistics in the border regions has neutralized the Western technical advantage.
The Stealth Neutralization (YLC-8B)
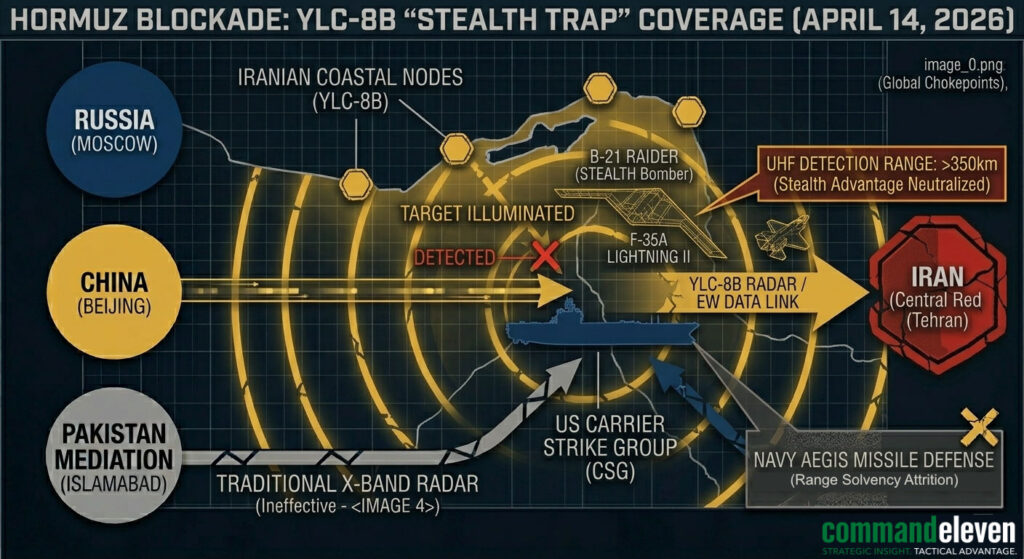
The proliferation of YLC-8B UHF Radar along the Iranian coast and Pak-Afghan border has effectively neutralized the “Stealth Umbrella.” Western carrier-based aviation, once the ultimate deterrent, is now “illuminated” at ranges exceeding 350km. This has created a tactical stalemate in the Hormuz Blockade, where Western naval power is geographically fixed and vulnerable.
The Insurance-Led Trap: Corporate Failure
Western corporate security persists in utilizing the “Ransom Economy” model, which CommandEleven identifies as a Systemic Failure Loop.
The Ransom Death Spiral
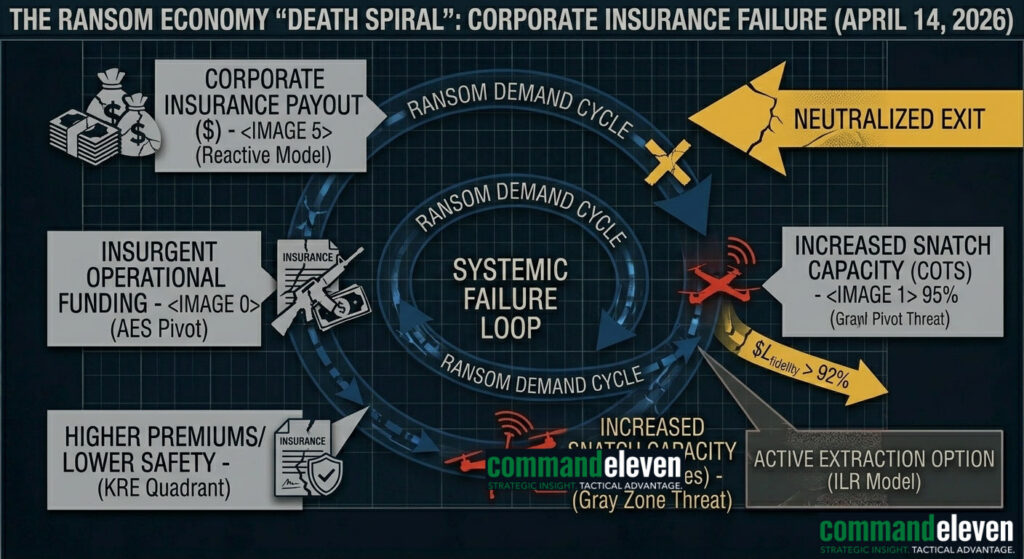
The traditional “Negotiate and Pay” framework, backed by high-premium insurance, serves as a direct funding mechanism for the adversary.
- Payout: Insurance funds the ransom.
- Reinvestment: Insurgent groups utilize funds to acquire advanced weaponry (COTS drones/ATGMs).
- Escalation: The success of the snatch cycle leads to increased kidnapping frequency and higher premiums.
The Political Pivot
In 2026, captor groups are increasingly prioritizing Political Leverage over financial gain. An insurance policy cannot negotiate the release of a prisoner held for ideological signaling or state-proxy leverage.
Technical Pillars of Failure
- Regulatory Rigidity: Failure to adapt supply-chain security to prevent the weaponization of “Adversary Vendor” technology.
- Export Control Obsolescence: The inability to stem the flow of dual-use drone components to non-state actors.
- Signature Vulnerability: Continued reliance on detectable RF signatures by Western EP teams, facilitating easy targeting by low-cost RDF (Radio Direction Finding) militias.
Conclusion: The Asymmetric Requirement
Western security failures are rooted in Rigidity. The institutional model is built for a world that no longer exists. CommandEleven’s ILR (Intelligence-Led Recovery) and EP (Executive Protection) pillars are designed to operate specifically within these vacuums, replacing bureaucratic inertia with asymmetric agility.


