KRE Methodologies: Operational Frameworks for High-Stakes Extraction in Non-Permissive Environments
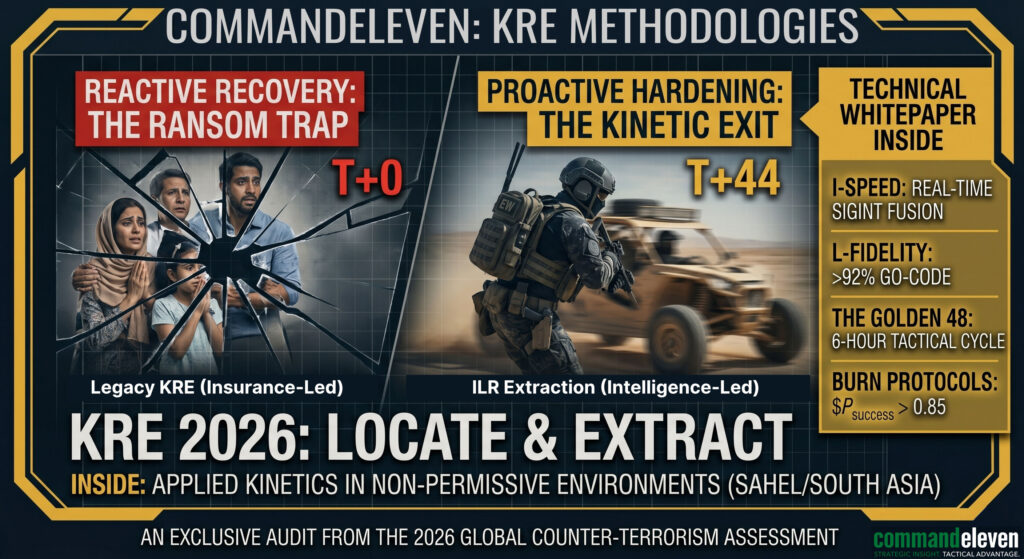
Technical intelligence on KRE methodologies for non-permissive environments. Operational frameworks for risk mitigation, crisis response, and high-stakes extraction.
Geopolitical Advisory for Investment – Intelligence-Driven ROI
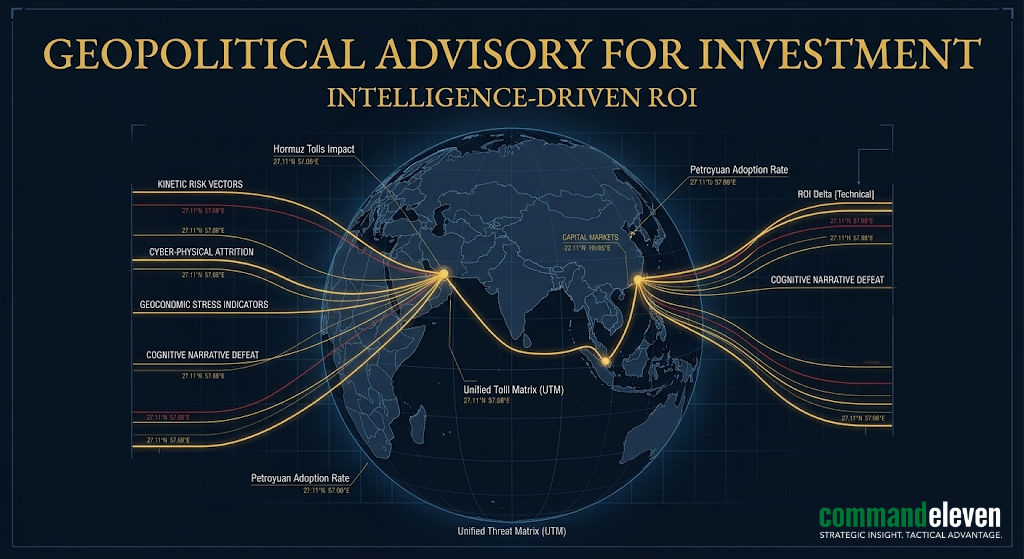
Strategic advisory on navigating 2026’s high-entropy markets. Use the Unified Threat Matrix to identify energy, logistics, and cyber-physical investment risks.
Cognitive Defense Training – Executive Hardening Protocols 2026
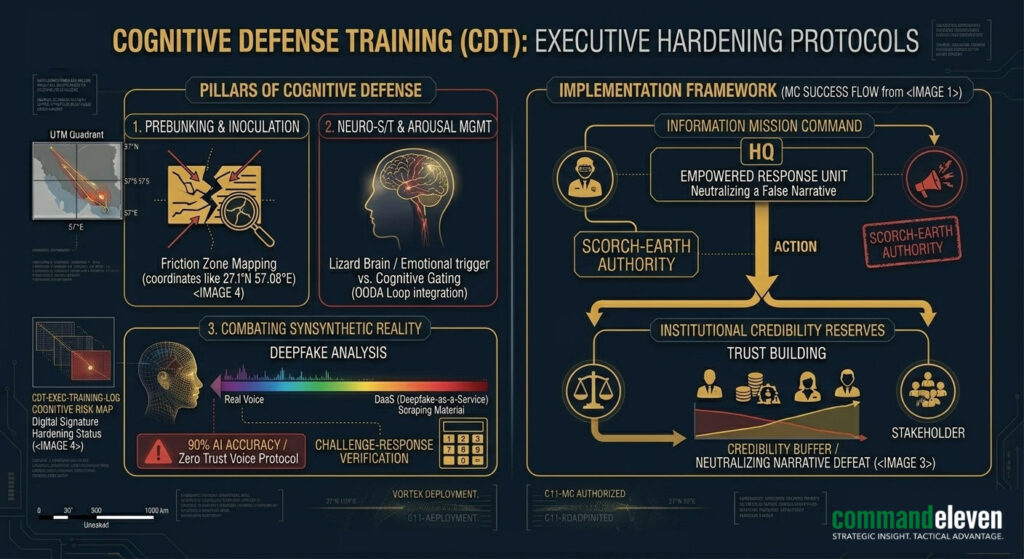
Operational security briefing on Cognitive Defense Training (CDT). Hardening the C-Suite against deepfakes, narrative warfare, and engineered distrust.
