Executive Summary
“Deepfake Volatility”- a phenomenon where high-fidelity synthetic media is used to disrupt organizational decision-making and secure authentication – is a critical vulnerability of financial Command and Control (C2) structure. While traditional cybersecurity focuses on perimeter defense, CommandEleven proposes Cognitive Shielding – a multi-layered framework designed to strengthen human and machine discernment. The framework integrates advanced detection algorithms with psychological conditioning (“Cognitive Hardening”) for high-value decision-makers. By establishing a “Shared Liability” and “Verifiable Truth” architecture, the paper argues that financial institutions can maintain operational continuity even as deepfake tools become more accessible to malicious actors.
3 Key Takeaways
- Shift from Technical to Cognitive Defense: Traditional KYC (Know Your Customer) and identity controls are increasingly bypassed by deepfakes. Defense must evolve to include “Cognitive Shielding,” which prepares decision-makers for the psychological manipulation inherent in AI-generated fraud.
- The Threat to Financial C2: Deepfakes pose an existential risk to organizational Command and Control by impersonating high-level executives (CFOs/CEOs) to authorize illicit fund transfers or extract classified intelligence.
- Mandatory Detection & Watermarking: To stabilize financial systems against volatility, the paper advocates for regulatory mandates requiring structured synthetic data for detection and digital watermarks to verify the provenance of all internal financial communications.
The Taxonomy of Synthetic Volatility: From Fraud to State-Level Attrition
The traditional banking threat model is predicated on the “Thief” archetype—actors seeking to exfiltrate capital for profit. The 2026 landscape introduces the “Saboteur” archetype—state-sponsored entities seeking to induce systemic insolvency.
The “CEO-Proxy” Attack and the Collapse of Verbal C2
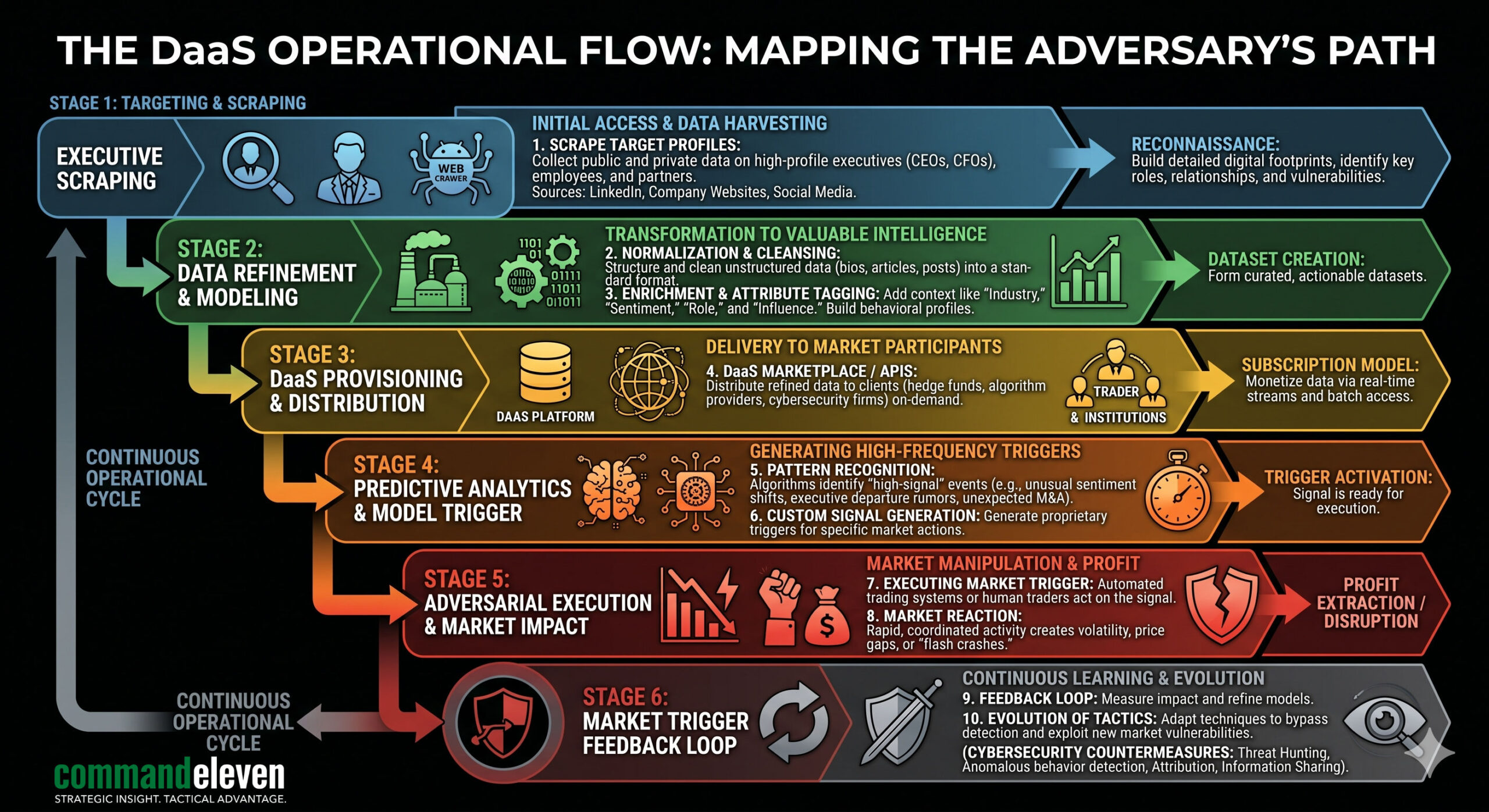
The reliance on VOIP and high-definition video conferencing has created a massive vulnerability in executive Command and Control. Deepfake-as-a-Service (DaaS) platforms now utilize generative adversarial networks (GANs) to monitor an executive’s public speaking cadence, tonal shifts, and emotional micro-expressions.
- Case Analysis: During a Tier-1 kinetic crisis, the “Fog of War” reduces the bandwidth for verification. A CFO receives a “priority” video call from the CEO, appearing to be in a high-stress environment (simulating a bunker or transit), ordering the liquidation of regional assets to “protect them from nationalization.”
- The Result: The liquidation itself triggers a market panic that the adversary then amplifies through bot-led OSINT channels.
Market-Trigger Deepfakes and Algorithmic Vulnerability
Modern HFT (High-Frequency Trading) algorithms are programmed to scrape social media and news wires for “Breaking” sentiment.
- The Exploit: A synthetic video of a Federal Reserve or Central Bank official leaked to a fringe but high-traffic news node. Even if the video survives for only 120 seconds before being debunked, the HFT algorithms have already executed sell-offs based on the “intent” of the speech.
- The “Flash-Insolvency” Event: We model a scenario where a localized deepfake in a GCC state triggers a bank run that consumes 40% of liquid reserves within 4 hours, long before “Truth-First” templates can be deployed.
Strategic Defense: The Cognitive Shielding Framework
Cognitive Shielding is the institutional equivalent of a Faraday cage; it is designed to ensure that the internal C2 remains unaffected by the “Electro-Magnetic Pulse” of synthetic misinformation.
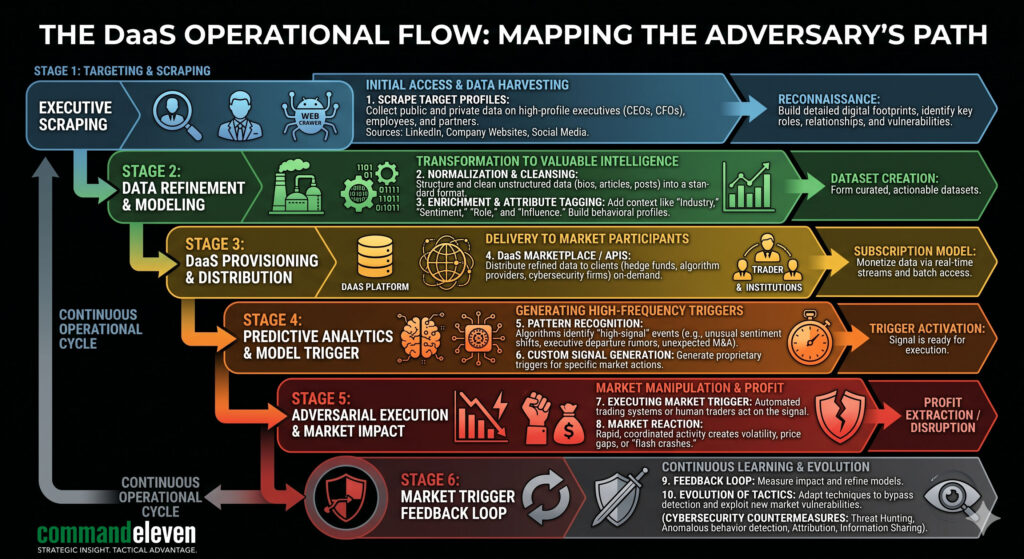
Out-of-Band (OOB) Verification: The Return to Analog
Digital trust is currently zero. To maintain C2, banking institutions must revert to “Hard-Key” authentication that exists outside the network being defended.
- Protocol 404 (Physicality): For any transaction exceeding the “Resilience Threshold,” the authorizing officer must provide a countersign from a physical, non-digital source. This includes “One-Time Pads” (OTPs) printed on physical security paper.
- Biometric Nullification: Since biometrics (voice/face) can now be synthesized, they must be treated as “Username” only—never as “Password.” Authentication must rely on “What you know” (the OOB key) and “Where you are” (verified through hardened GPS/Location tags).
Narrative Pre-positioning: The Antibody Strategy
In Cognitive Warfare, the first narrative to occupy the “Information Space” becomes the baseline.
- The Credibility Buffer: Banks must publish daily “Operational Baseline” reports. These are not marketing updates; they are technical proofs of liquidity and C2 stability. When an adversary launches a deepfake, the public already has a 24-hour “Baseline” to compare it against.
- Synthetic Fingerprinting: All legitimate executive communications must be embedded with a digital “Distortion Signature” or watermark that is invisible to the human eye but instantly recognizable by the bank’s own verification bots.
Operationalizing “Mission Command” in Banking
In the event of a total communication blackout or a “C2-Collapse” at HQ, regional banking nodes must transition to Mission Command (MC).
Decentralized Autonomy and the “Silent C2” Posture
Under MC, a regional branch manager is authorized to ignore centralized directives if they fail the OOB verification test. This prevents a “Top-Down” collapse where a compromised HQ inadvertently destroys the entire network.
- The 72/48 Hardening Trigger: Upon the detection of increased “Narrative Pre-positioning” (bot activity increasing by 300% on specific financial keywords), the organization enters a “Hardened Posture.”
- Actionable Tasks: All digital voice/video directives are suspended. Communication reverts to encrypted text-only channels accompanied by the Protocol 404 keys.
Technical Integration: The Unified Threat Matrix (UTM)
Cognitive defense cannot be siloed. It must be mapped against the Kinetic (KT) and Cyber-Physical (CPT) vectors.
CPT Vector: Protecting the Physical Ledger
Adversaries often use deepfakes as a “Distraction Vector.” While the C-Suite is busy managing a narrative crisis, a kinetic or cyber-physical attack is launched against the data centers or the power grid.
- Integrated Monitoring: The UTM dashboard must show “Narrative Sentiment” alongside “Network Intrusion” and “Physical Perimeter Status.” A spike in CI (Cognitive) activity must trigger an automatic “High Alert” for the CPT (Cyber-Physical) nodes.
GER Vector: Geoeconomic Resilience
Banking C2 must account for the “Hormuz Toll” reality. If the bank’s assets are tied to energy trade, the Cognitive Shielding must also monitor “Currency Narrative Shifts” (e.g., rumors of a sudden shift from USD to RMB) to prevent being caught in a liquidity trap.
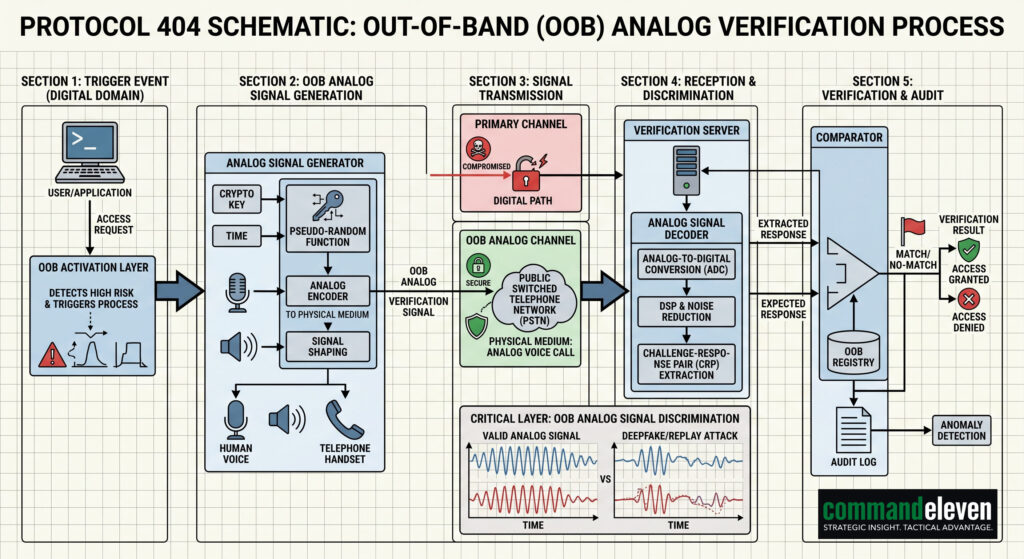
Technical Schematics: The OODA Loop vs. The Narrative Attack
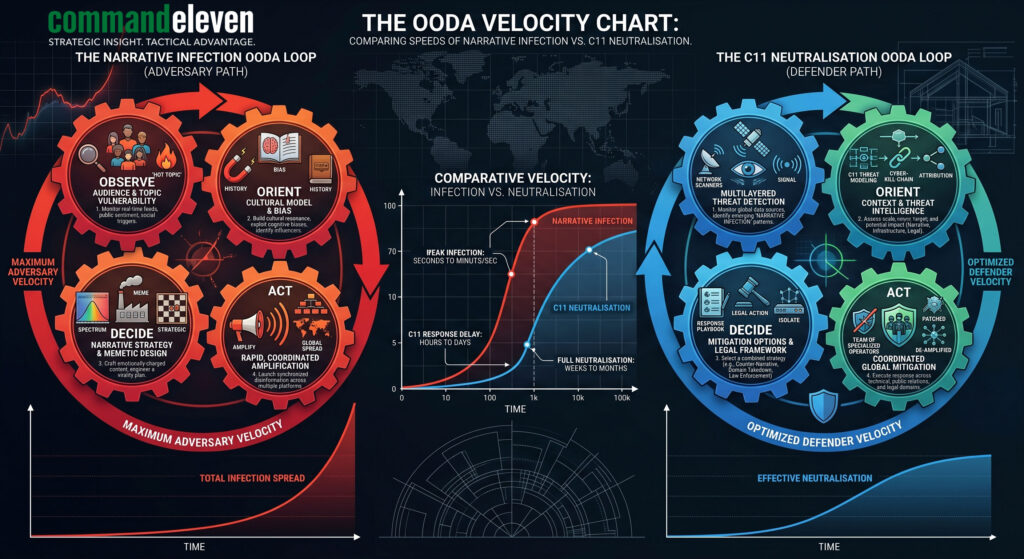
The success of a deepfake is entirely dependent on its ability to complete its “Infection Cycle” before the target institution can complete its “Detection/Neutralization Cycle.”
- Attack Velocity: A deepfake reaches 10 million views in <60 minutes.
- C11 Defense Velocity: Using “Truth-First” templates and automated “Distortion Signature” checks, the neutralization must occur in <15 minutes.
The Clinical Necessity of Cognitive Shielding
The financial battlespace of 2026 is one of Perception Management. A bank is only as solvent as its most recently verified directive. By implementing CommandEleven’s Cognitive Shielding, institutions move from being “Narrative Victims” to “Hardened Information Nodes.”
CommandEleven Red Team Assessment
We anticipate a “Proof of Concept” state-level deepfake attack on a Tier-2 Western bank by the end of Q2 2026. Adoption of Protocol 404 and OOB Analog keys is the only viable defense against systemic “Flash-Insolvency.”
The Neuro-S/T Factor: The Psychology of Engineered Distrust
Cognitive Warfare is, at its core, an attack on the biological processing centers of the brain. In high-stress banking environments, the “Cognitive Load” of an executive is already near capacity. Adversaries exploit this biological ceiling.
Heuristic Exploitation and “Stress-Induced Certainty”
During a kinetic crisis—such as the collapse of the “Mediation Stasis” in the Levant—the human brain reverts to “System 1” thinking: rapid, intuitive, and highly susceptible to emotional triggers.
- The Exploit: A Deepfake does not need to be perfect; it only needs to be “emotionally resonant.” By simulating a state of extreme urgency or fear in a synthetic likeness, adversaries bypass the executive’s critical analytical faculties.
- The “Availability Cascade”: Once a synthetic narrative (e.g., “The central bank has frozen all outbound SWIFT transfers”) is amplified by bot-networks, it creates a self-reinforcing loop. The executive sees the “news” on multiple channels, which reinforces the validity of the synthetic audio/video directive they just received.
The Neuro-Biology of Institutional Trust
Trust is a neural shortcut. Institutional collapse occurs when the “Cost of Verification” exceeds the “Speed of Crisis.”
- The Cognitive Defense Solution: We implement “Forced Verification Slowness.” By mandating the Protocol 404 keys, we force the executive out of the emotional “System 1” state and back into “System 2” analytical processing. This 120-second pause is often the difference between a catastrophic capital flight and a successful narrative neutralisation.
Implementation Roadmap: The 180-Day Hardening Cycle
Transitioning a global financial institution to a Cognitive Shielding posture is a phased operation. This roadmap aligns with the 72/48 Hardening Protocol previously established.
Phase I: Audit and Baseline (Days 1–45)
- Narrative Vulnerability Audit: Mapping the digital footprint of all Tier-1 and Tier-2 executives.
- C2 Infrastructure Review: Identifying “single-point-of-failure” communication channels (e.g., reliance on WhatsApp or unencrypted VOIP for C-Suite directives).
- Baseline Sentiment Analysis: Establishing the “Credibility Buffer” by documenting the institution’s historical reliability and communication cadence.
Phase II: Architecture Deployment (Days 46–120)
- Protocol 404 Integration: Distribution of physical OOB (Out-of-Band) keys and training for all authorized financial officers.
- Synthetic Fingerprinting: Implementing automated watermarking and distortion signatures on all legitimate outbound media.
- Mission Command Drill: Simulating a “C2-Collapse” scenario where regional nodes must operate autonomously using OOB keys for a 24-hour period.
Phase III: Active Defense Posture (Days 121–180)
- UTM Integration: Linking the Cognitive monitoring dashboard to the Kinetic (KT) and Cyber-Physical (CPT) sensors.
- Truth-First Template Library: Pre-vetting crisis communication templates for 12 identified failure scenarios (e.g., Liquidity Rumors, Executive Death Hoax, Grid Failure).
- Red Team Validation: Executing a controlled “Deepfake Stress Test” to measure the institution’s OODA loop velocity from detection to neutralisation.
Conclusion – The New Baseline of Financial Sovereignty
The “Petroyuan Pivot” and the “Indian Ocean Interdiction” are proof that the physical and financial worlds are no longer separate. In 2026, Cognitive Warfare is the most efficient tool for state actors to achieve kinetic results without firing a single shot.
Banking institutions are the “High-Water Mark” for this conflict. If the C2 of the global financial system can be narratively compromised, the resulting “Flash-Insolvency” will do more damage than any conventional blockade. Cognitive Shielding is not a luxury; it is the fundamental requirement for institutional survival in the 2026 battlespace.