Executive Summary
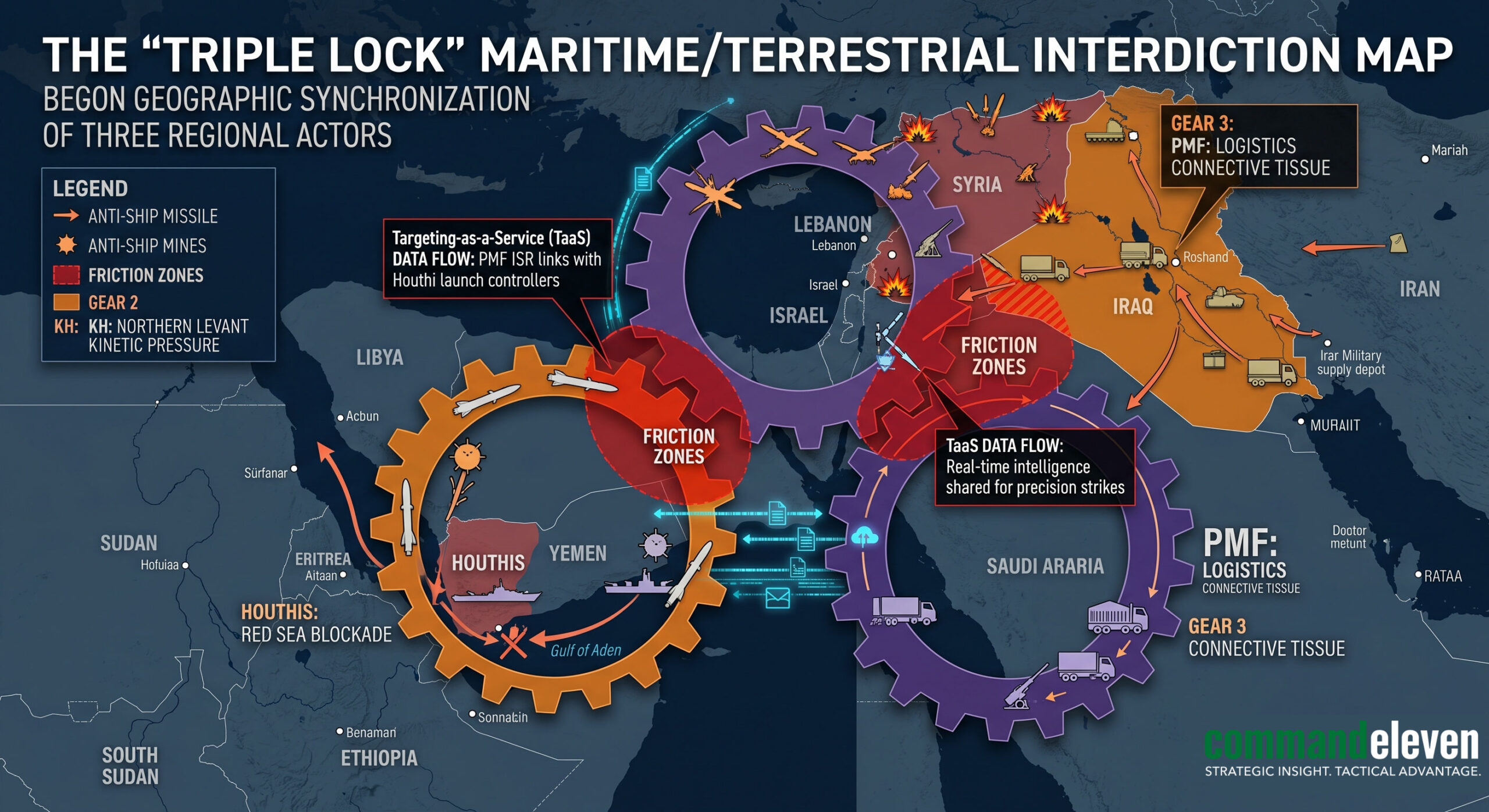
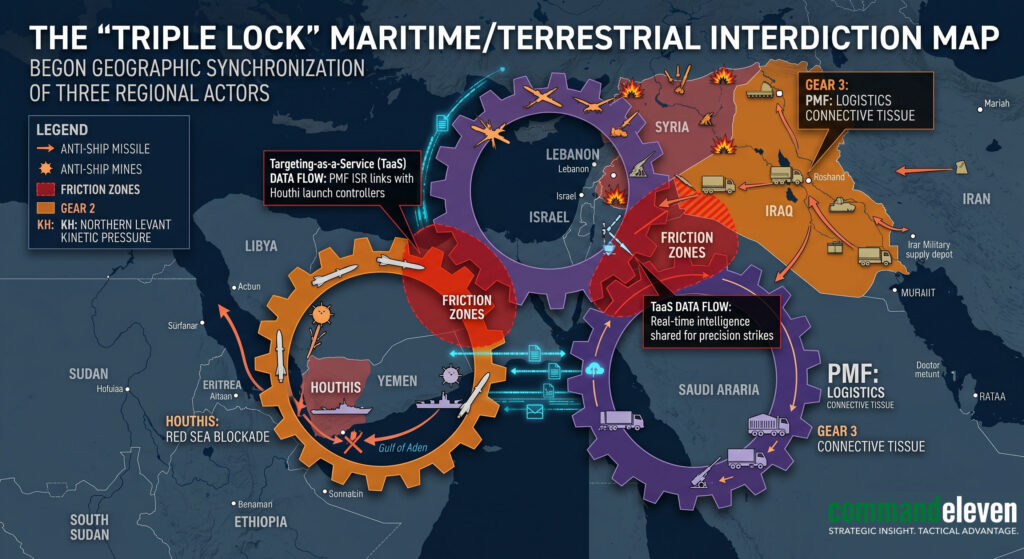
The “Triple Lock” is the operational realization of the Mosaic Defense (est. 2002) applied to the regional battlespace. It represents a transition from autonomous proxy operations to a synchronized, multi-front “lock” on Western maritime and terrestrial assets. This doctrine ensures that any U.S. or allied kinetic action against one node triggers a simultaneous, pre-programmed escalation across the other two, effectively “locking” the adversary into a perpetual state of multi-domain attrition.
Key Takeaways
- The IRGC-QF acts as the “Operating System” providing technical and strategic interface.
- Shared SIGINT loops allow for “Targeting-as-a-Service” across three distinct fronts.
- Autonomous escalation is hard-coded into the “Triple Lock” regional architecture.
Management & Structure: The IRGC-QF as the “Architect of Mosaic Attrition”
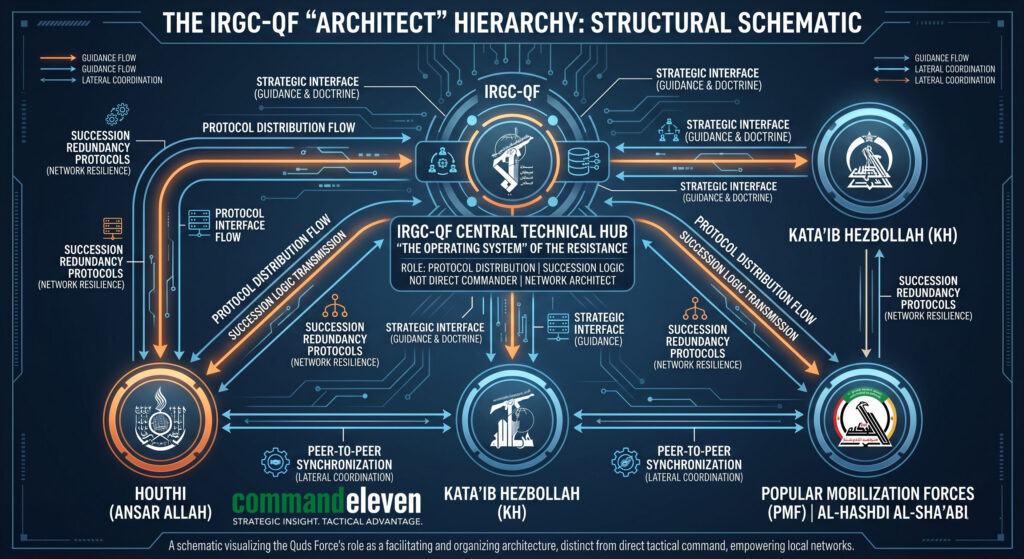
While the Houthi-KH-PMF entities execute the kinetic “Lock,” the Islamic Revolutionary Guard Corps – Quds Force (IRGC-QF) serves as the structural architect and strategic guarantor.
- The Transition from Patron to Peer: Under the 2026 doctrine, the IRGC-QF has evolved from a traditional “supplier” into a Strategic Interface. It provides the high-level intelligence and specialized technical components (e.g., encryption modules, guidance chips) that allow the Triple Lock to function as a unified entity.
- Decentralized Command, Unified Intent: The QF manages the “Strategic Sync” without requiring a physical presence. It establishes the “Succession Protocols” and “Operational Decision Trees” that ensure proxies do not collapse into infighting post-decapitation.
- The QF “Hub and Spoke” Redundancy: By sharding technical expertise across multiple geographic theaters (Sana’a, Baghdad, Beirut), the QF ensures that the neutralization of a command center in Iraq does not degrade the technical capacity of the Houthi nodes. The QF acts as the “Memory” of the Mosaic Defense, ensuring that tactical lessons learned in one theater are instantly codified into the protocols of another.
Actor Profiles & Functional Roles
The Triple Lock functions through a division of operational labor, synchronized via the Stigmergic C2 model:
| Actor | Geographic Sector | Functional Role in the “Lock” |
| Ansar Allah (Houthis) | Southern Red Sea / Bab el-Mandeb | The Maritime Anchor: Primary interdiction of global energy trade and “Hormuz Toll” enforcement in the South. |
| Kata’ib Hezbollah (KH) | Iraq / Syria / Northern Levant | The Kinetic Pressure Valve: Precision drone/missile strikes on U.S. regional footprints to disrupt logistics and C2. |
| Popular Mobilization Front (PMF) | Iraq / Trans-Regional Logistics | The Connective Tissue: Securing land-bridge corridors and providing “Targeting-as-a-Service” for the other nodes. |
Technical Vector: SIGINT Loops and Adaptive EW Resilience
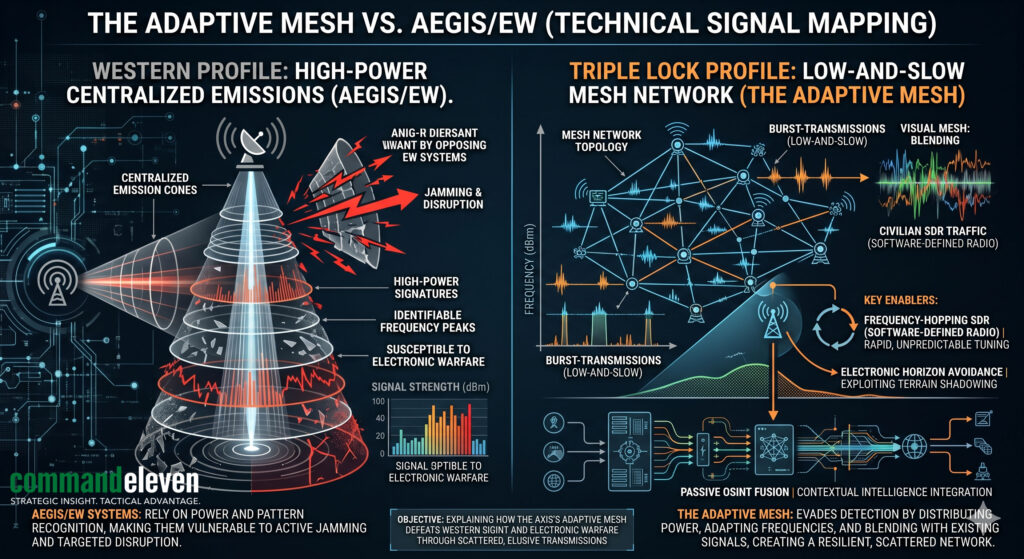
The failure of Western SIGINT to degrade Triple Lock coordination stems from the axis’s transition to Environmentally Adaptive Mesh-Networking.
- Defeating Western SIGINT Technology: Legacy Western SIGINT relies on detecting high-power, centralized radio/satellite emissions. The axis utilizes low-power, burst-transmission mesh networks that blend into the “Urban Noise” of the Levant and the “Maritime Noise” of the Red Sea. By utilizing Software-Defined Radio (SDR), these nodes operate on frequency-hopping patterns that are indistinguishable from civilian cellular or maritime radar traffic.
- Adversary-Specific Encryption Shifting: The Triple Lock utilizes an adaptive encryption layer that shifts based on the adversary’s detection profile.
- Against US Navy (AEGIS-based EW): The mesh-network shifts to high-frequency, short-range terrestrial relays that avoid the “Electronic Horizon” monitored by carrier groups.
- Against Local State Actors: It shifts to encrypted cellular overlays (VPN-on-VPN) that utilize existing commercial infrastructure as a “shield.”
- EW Countermeasures: When the U.S. initiates high-power jamming, the Triple Lock nodes automatically transition to “Silent Listen” mode. They utilize passive sensors (COTS-based OSINT) to maintain situational awareness without emitting a signal, re-engaging the mesh-network only when the jammer passes or is localized.
Operational Analysis: The “Epic Fury” Response
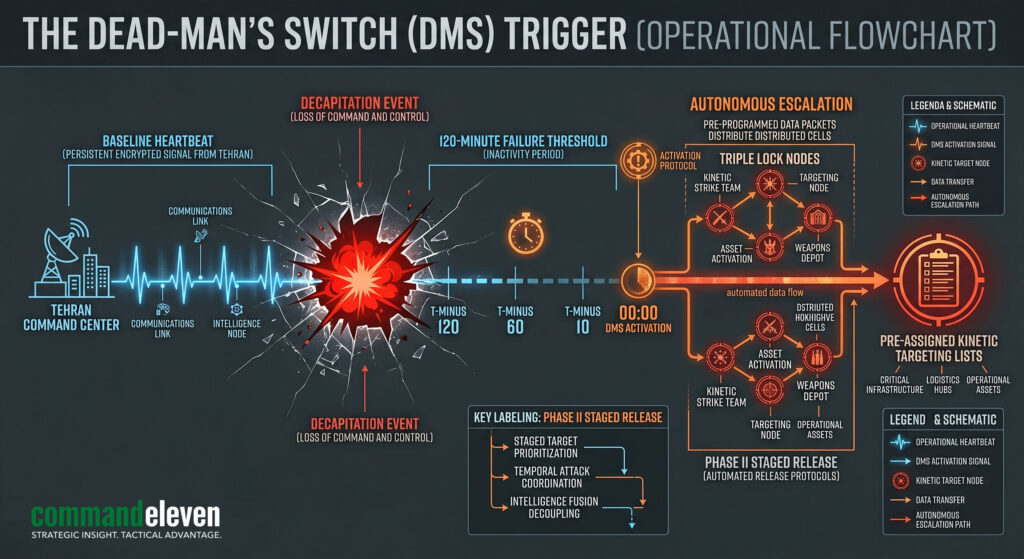
As discussed multiple times in our podcast series with Survival Dispatch Network (SDN) regarding foreign-based sleeper cells, Autonomous Escalation is not a “called” play; it is an “activated” state. It functions through a Dead-Man’s Switch (DMS) protocol.
- The Autonomous Trigger: The “Lock” is set to a “Pre-Kinetic Baseline.” Regional commanders and sleeper cells must provide a regular “Heartbeat Signal” to the network.
- The Decapitation Trigger: When the “Heartbeat” of a Tier-1 commander (e.g., the Supreme Leader or the QF Chief) ceases, the network enters a “Staged Release” of kinetic responses.
- Sleeper Cell Activation: In the 2026 model, foreign-based cells are pre-assigned “Trigger Events” (e.g., a direct kinetic strike on Tehran). Once the “Trigger” is verified via public OSINT channels, the cell is authorized to initiate localized “Infrastructure Attrition” without further contact from the QF.
The Triple Lock deployed in the following phases:
- Phase I (The Houthi Trigger): Immediate implementation of the “Southern Blockade.”
- Phase II (The KH/PMF Expansion): Simultaneous “Saturation Attacks” on U.S. logistics nodes in Erbil and Al-Tanf to prevent a coordinated Western naval response.
- Phase III (The Stasis Lock): The axis moved to a “Low-and-Slow” attrition model, where the cost of defending against the Triple Lock exceeds the strategic value of remaining in the theater.
Understanding the Autonomous Trigger Flow
- Baseline: Continuous SIGINT “Heartbeat” between the Hub (IRGC-QF) and the Spokes (Proxies/Sleeper Cells).
- Event: Kinetic Decapitation (Neutralization of the Hub).
- Threshold: 120-minute “Heartbeat” failure.
- Action: Autonomous transition to “Mosaic Defense Phase II”—pre-assigned targeting lists (The Triple Lock) go active.
Kinetic Vector: The Mosaic Defense in Action
The Triple Lock is the ultimate expression of Mosaic Defense distribution. By sharding their launch platforms and SIGINT nodes across three distinct geographic theaters, the axis has effectively “noised” the U.S. targeting cycle.
- Succession Reliability: Leadership targeting of KH or Houthi commanders has failed to degrade the “Lock.” The Stigmergic nature of the C2 ensures that the Protocol (The Lock) remains active even when the Personnel are neutralized.
- CER Defeat: The axis continues to leverage the Cost-Exchange Ratio, utilizing $20k disposable kinetics to force the expenditure of $2M precision-guided munitions (PGMs) across three fronts simultaneously.
CommandEleven Red Team Assessment
The Triple Lock cannot be broken by traditional “Decapitation” or localized kinetic strikes. Breaking the Lock requires a Systemic Disruption of the shared SIGINT loops and the connective logistics managed by the PMF.
Operational Indicator: We anticipate a coordinated “Triple Lock” surge in the Arabian Sea by early May, intended to test the endurance of the U.S.-Indonesia maritime pact. Corporate clients must activate the 72/48 Hardening Protocol immediately for any assets transiting the Southern Corridor.