Executive Summary
The “Hardware Truth” of the Transnational Border Void audits the failure of digital-centric security in the high-friction mountain corridors of 2026. Centralized states have fallen victim to the Digital Mirage, losing administrative control to Conflict Clusters that utilize Analog Persistence to normalize shadow governance. CommandEleven mandates a pivot to Hardware Truth—physics-based verification—and the restructuring of border garrisons into autonomous Administrative Tiles via the #72/48 Resilience Protocol.
3 Key Takeaways
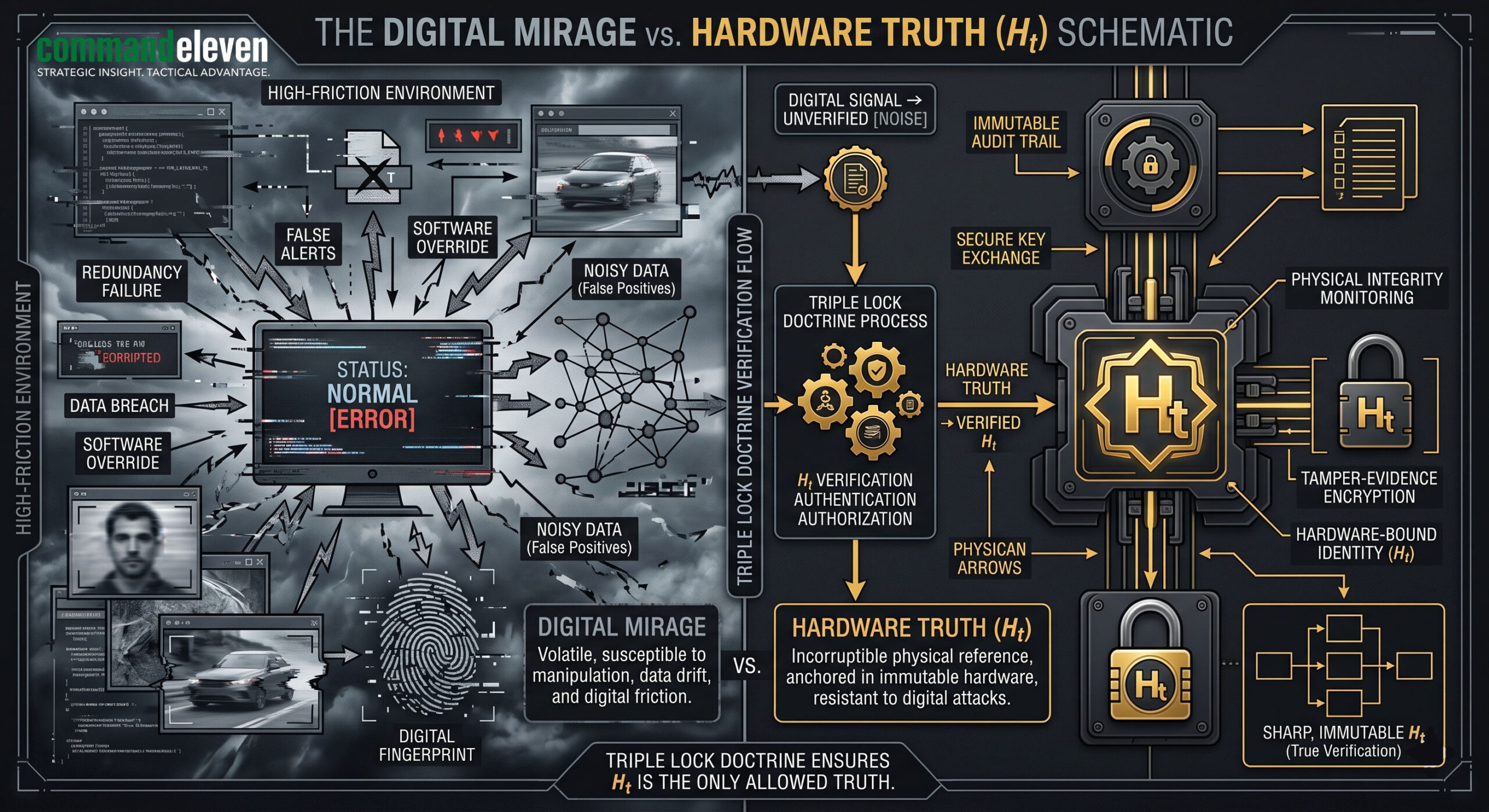
- Failure of the Digital Mirage: High-tier digital surveillance is a lagging indicator in the Border Void. Security depends on Hardware Truth and the Triple Lock Doctrine for all tactical verification.
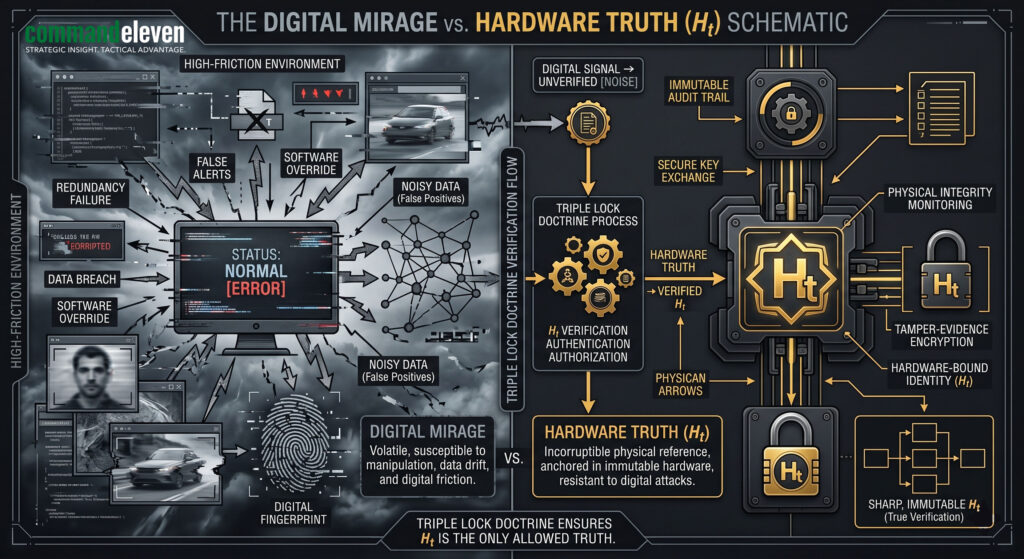
- Shadow Governance Normalization: Non-state actors in the “Conflict Cluster” are winning the Administrative Asymmetry battle by providing localized, predictable utility that the centralized state cannot match.
- Resilience through Tile Autonomy: Reclaiming the border requires the deployment of autonomous “Tiles” capable of 48-hour persistence during total network “Flash-Dark” events, focusing on the interdiction of manual logistical oxygen.
The Digital Mirage of Border Security
In the 2026 security environment, the reliance on high-tier digital surveillance—UAV feeds, signals intelligence (SIGINT), and automated sensor grids—has created a “Digital Mirage.” While centralized dashboards in Islamabad or Kabul may signal a secured perimeter, the physical reality of the Transnational Border Void (specifically the Bajaur/Dir/Kunar corridor) tells a different story.
The “Void” is characterized by a total network “Flash-Dark” environment, where digital signals are either intercepted, jammed, or simply non-existent due to terrain shielding. In this theater, the state’s reliance on digital dashboards has led to a catastrophic Competency Gap. To secure the border, we must pivot from digital consensus back to Hardware Truth.
Defining Hardware Truth in the Borderlands
Hardware Truth is the immutable, physics-based baseline of situational awareness. It is the physical verification of a transit route, the face-to-face “Acoustic Handshake” with a local malik, and the manual audit of an outpost’s resource sovereignty.
- The Clinical Baseline: If a satellite feed shows an empty mountain pass but the “Hardware Truth” (a physical audit by a LPI-equipped team) identifies fresh tire tracks and manual logistical caching, the Hardware Truth dictates the tactical response.
- The Triple Lock Doctrine: No kinetic or administrative action is authorized based on digital signals alone. Every “Digital Mirage” must be triple-locked via:
- Level 1 (Digital): SIGINT/UAV identification (Secondary).
- Level 2 (Acoustic): Voice-verified human intelligence (Tertiary).
- Level 3 (Hardware): Direct, physical confirmation of the threat signature on the ground (Primary).
The Conflict Cluster: Shadow Governance in the Void
The Transnational Border Void has become the primary theater for the “Conflict Cluster”—a mosaic of non-state actors that have achieved Shadow Governance Normalization. These groups operate outside the digital grid, utilizing Analog Persistence to manage their administrative cores.
- Administrative Asymmetry: The Cluster provides more predictable adjudication and resource distribution in these mountain “Tiles” than the centralized state. By the time a state official logs into a portal to report a grievance, the Shadow Judge has already executed a verdict based on Shadow Judicial Primacy.
- The Sukkur Protocol in the Highlands: Just as in the Indus corridor, clandestine networks in the borderlands utilize low-signal infiltration to hollow out state authority. They don’t attack the garrison; they simply make the garrison irrelevant to the population’s daily survival.
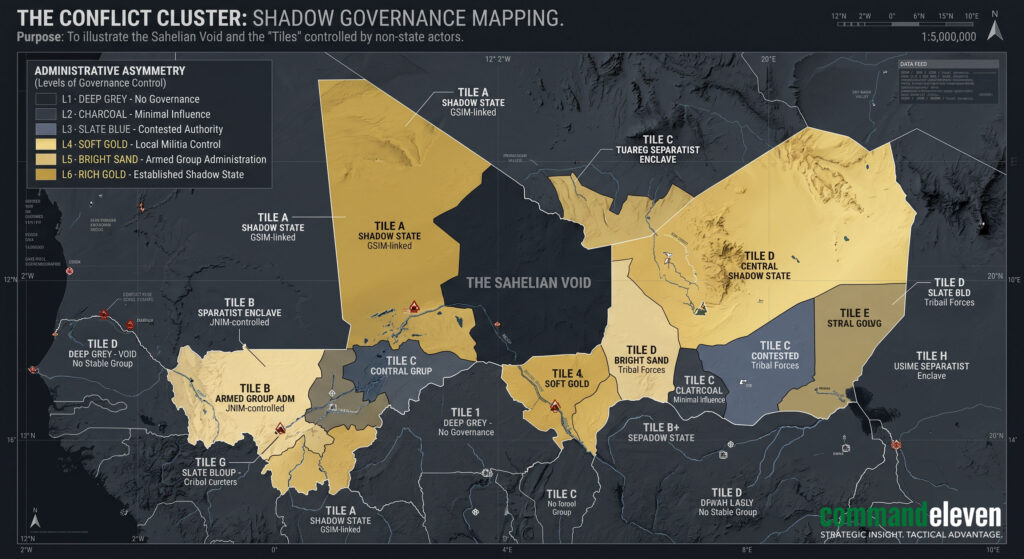
Implementing the #72/48 Resilience Protocol for Border Tiles
To reclaim the Void, border outposts must be restructured as autonomous Administrative Tiles.
- The 72-Hour Hardening: In the event of a high-velocity incursion or a total network severance, the Tile immediately severs its digital umbilical. It enters a state of “Silent Running,” relying on pre-coordinated, physics-based C2.
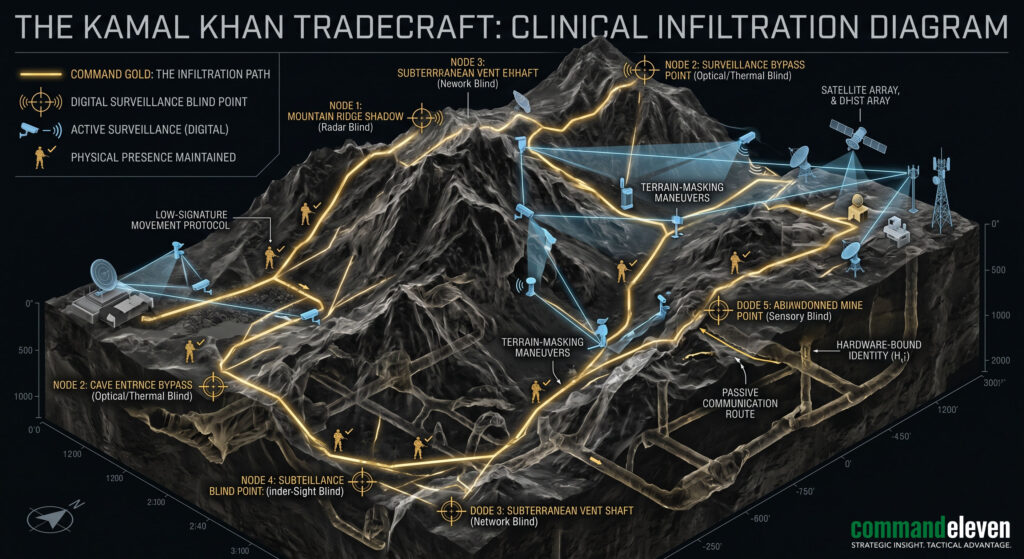
- The 48-Hour Autonomous Persistence: The Tile must maintain its own Analog Liquidity and security posture without external support. This is the Kamal Khan Standard: the ability to operate as a surgical, self-sustaining unit in a transparent but digitally-severed battlespace.
Geospatial Mapping of the Void: The Kunar-Bajaur Axis
Our audit identifies the Kunar-Bajaur axis as the critical rupture point for 2026. This is where the Geofinancial Risk (GER) is highest, as the Cluster weaponizes artisanal mining and smuggling routes to fund their Analog Liquidity.
- Logistical Artery Interdiction: The state must identify the five primary manual transit routes that serve as the “Logistical Oxygen” for the Cluster. Reclaiming these requires Mosaic Defense—placing autonomous “Tiles” at each node to enforce verification.
The Terminal Reality
The Transnational Border Void cannot be secured through a screen. The “Digital Mirage” has only served to widen the Competency Gap, allowing the Conflict Cluster to normalize its shadow administration. Reclaiming sovereignty requires a clinical return to the physics of warfare: the deployment of autonomous tiles, the mandatory use of the Triple Lock Doctrine, and the absolute primacy of Hardware Truth.