Executive Summary
In the 2026 security landscape, the primary battlespace has migrated from physical geography to the cognitive architecture of the administrative core. Traditional intelligence frameworks are struggling to adapt to a reality where “Digital Signaling” is no longer just a method of communication, but a kinetic-grade weapon capable of inducing total institutional paralysis. This white paper codifies the CommandEleven Mosaic Doctrine, shifting from centralized, vulnerable hierarchies to a decentralized architecture of autonomous “Tiles.” By prioritizing Hardware Truth over digital consensus and implementing the #72/48 Resilience Protocol, an organization ensures that an adversary’s “Single-Trigger” threat fails to achieve systemic collapse. The objective is terminal: to transition from a state of reactive “Green Zone Hallucinations” to a proactive model of Cognitive Shielding and administrative persistence.
3 Key Takeaways
- The Primacy of Hardware Truth: In an era of industrial-scale deception (DaaS), digital data is a compromised baseline. Resilience is achieved only through the Triple Lock Doctrine, anchoring high-value decisions in immutable, physics-based verification (mechanical gauges and physical ledgers).
- The Mosaic Defense Transition: Centralized C2 is a strategic liability. Hardening the administrative core requires the deployment of autonomous “Tiles” capable of Stigmergic Coordination, allowing localized governance to persist even during a total “Flash-Dark” network severance.
- Neutralizing the Conflict Premium: Cognitive warfare is a geofinancial tool used to harvest market windfall through Synthetic Panic. The #72/48 Resilience Protocol acts as a deterrent by denial, proving to the market that the administration can maintain flow and utility regardless of digital disruption.
Executive Summary – The Institutional Rupture of Perception
In the current 2026 security theater, the primary battlespace has migrated from physical geography to the cognitive architecture of the administrative core. Traditional intelligence frameworks are struggling to adapt to a reality where “Digital Signaling” is no longer just a method of communication, but a kinetic-grade weapon capable of inducing total institutional paralysis.
The New Frontline: Administrative Vulnerability
Cognitive Warfare is the systematic exploitation of the perception-action cycle. By flooding an administrative core with Narrative Amplification and Synthetic Panic, an adversary does not need to destroy a building to seize a state; they merely need to ensure the decision-makers within that building believe they have already lost. This represents the terminal evolution of the “Dark-State” Model, where the formal state’s inability to process reality results in a high-velocity surrender of its administrative functions.
The Rupture of the 45-Day Window
Our audit of recent institutional failures confirms that once cognitive dominance is achieved, the 45-Day Terminal Window begins. This is the measured interval between the first digital signal and the mechanical collapse of civil authority. In this window, the adversary utilizes Administrative Asymmetry to prove that their shadow governance is more predictable, more resilient, and more “truthful” than the established state.
The Resilience Mandate: Cognitive Shielding
Administrative Resilience is no longer a matter of robust servers or thicker walls; it is the capacity of a command structure to maintain Cognitive Accuracy under extreme “Noise Induction.” To survive, the state must transition from a reactive posture—chasing ghosts in the digital mirage—to a “Whole-of-Nation” Cognitive Shielding model. This doctrine prioritizes Hardware Truth over digital consensus and replaces monolithic command structures with a decentralized Mosaic Defense.
The objective of this white paper is to codify the methodologies required to identify, audit, and neutralize cognitive incursions before they hit the Transparency Threshold and trigger a systemic rupture.
Anatomy of a Cognitive Incursion – Mechanics of the Digital Mirage
A cognitive incursion is not defined by the volume of data, but by the Velocity of Rupture it induces within the decision-making cycle. Unlike traditional electronic warfare, which seeks to jam signals, Cognitive Warfare seeks to saturate and distort them until the administrative core can no longer distinguish between a legitimate threat and a Synthetic Panic.
The Synthetic Panic Induction
The opening phase of an incursion utilizes Narrative Amplification to create an artificial environment of institutional friction. By deploying Deepfake-as-a-Service (DaaS) and coordinated bot-networks, an adversary can simulate a groundswell of civil unrest or administrative failure.
- The Strategic Intent: To force a “Reactive Posture” where the state exhausts its resources chasing a digital mirage, leaving the actual Kinetic Gate undefended.
- Archive Precedent: This mirrors the Sukkur Protocol tradecraft, where localized chaos was manufactured to blind central intelligence to the hollowing out of the secondary transit arteries.
Noise Induction & The Transparency Threshold
As the incursion matures, it hits the Transparency Threshold. This is the point where the volume of contradictory data—the “Noise Induction”—overwhelms the administrative core’s capacity for Cognitive Accuracy.
- Institutional Myopia: Decision-makers become hyper-focused on the digital noise, losing sight of the Hardware Truth on the ground.
- The Sanitization Gap: In this state, the state inadvertently “sanitizes” its own intelligence to fit the emerging digital narrative, effectively doing the adversary’s work for them.
From Digital Ambush to the Kinetic Gate
The terminal phase of a cognitive incursion is the transition from psychological pressure to physical intervention. This is the Single-Trigger Threat.
- The Mechanism: Once the administrative core is paralyzed by Synthetic Panic, the adversary triggers a localized kinetic event—an interdiction of a pipeline, a SCADA blackout, or a targeted strike.
- The Result: Because the state is still looking at the “Mirage,” its Sensor-to-Shooter Latency (SSL) is too high to respond. The kinetic event is then narrative-amplified as “Total State Collapse,” triggering the 45-Day Terminal Window.
Audit of the “Flash-Dark” Vector
In 2026, the most dangerous cognitive incursion concludes with a “Flash-Dark” event. By weaponizing the fear of a total network blackout, an adversary can induce a Passive Survival Posture in a population before a single light actually goes out. Reclaiming control in this environment requires an immediate pivot to Analog Verification and the severing of all compromised digital signaling.
Deepfake-as-a-Service (DaaS) – The Industrialization of Synthetic Deception
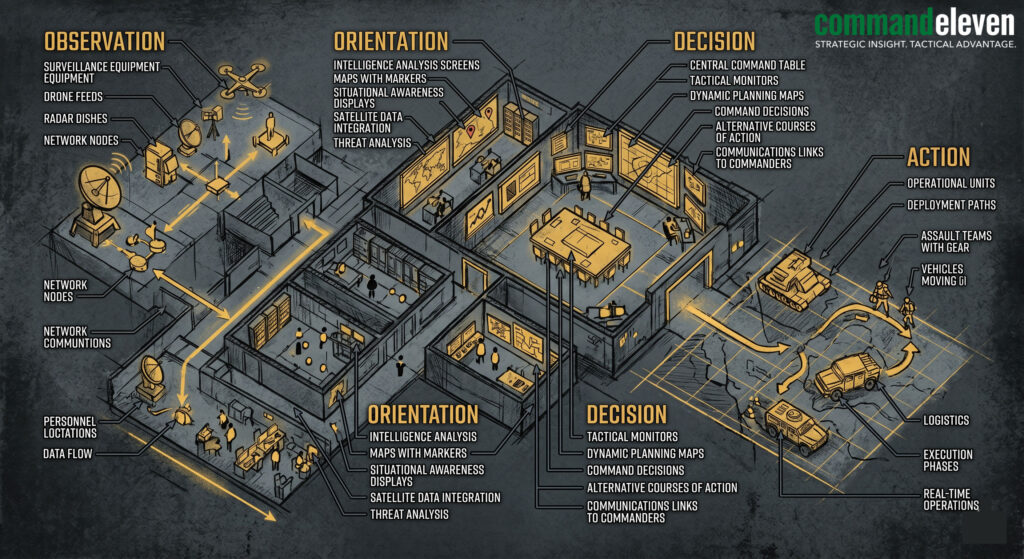
In the 2026 threat landscape, cognitive incursions have moved beyond amateur “cheap-fakes” to a highly commoditized, industrial-scale model known as Deepfake-as-a-Service (DaaS). This framework allows non-state actors and rival Garrison States to outsource the generation of high-fidelity synthetic media to specialized dark-web entities, ensuring a constant stream of “Digital Signaling” that bypasses traditional verification.
The Mechanics of DaaS
DaaS providers utilize generative adversarial networks (GANs) and large-scale voice cloning to create assets that are indistinguishable from “Hardware Truth” to the untrained eye. These services are often sold on a subscription basis, providing:
- Persona Synthesis: Creating entirely fake administrative officials with verifiable social histories.
- Voice Hijacking: Real-time cloning of a commander’s voice for use in compromised “Acoustic Handshakes.”
- Synthetic Crowd Generation: Manufacturing images and videos of mass protests or military mutinies to trigger Institutional Myopia.
Tactical Examples of DaaS Incursions
- The “Orders from Above” Vector: In a high-friction theater, a field commander receives a high-fidelity video call from what appears to be their superior, ordering a tactical retreat. By the time the Triple Lock Doctrine is applied to verify the order, the Kinetic Gate has been opened, and the adversary has seized the administrative core.
- The Geofinancial Panic: A DaaS-generated video of a Central Bank Governor announcing a “Flash-Dark” freeze on all digital assets is released simultaneously across all encrypted channels. This induces Synthetic Panic, causing a run on banks that creates a self-fulfilling prophecy of institutional collapse.
- Narrative Pre-Positioning: DaaS is used to “Pre-bunk” a state’s legitimate response. Before a government can release footage of a successful counter-terrorism operation, the DaaS provider releases a “leak” showing the same footage altered to depict civilian casualties, poisoning the information environment.
Administrative Asymmetry – The Competency Gap
Administrative Asymmetry is the clinical measurement of the delta between a state’s bureaucratic inertia and an adversary’s high-velocity governance. In a cognitive war, the adversary wins not by being “better,” but by being more predictable during a crisis.
The Shadow Governance Normalization
When a state suffers from Institutional Myopia, it fails to provide basic administrative utility—security, judicial adjudication, and resource distribution. The adversary fills this Sahelian Void with a “Dark-State” model.
- The Sukkur Protocol: As established in the Agency Rules archive, this protocol illustrates how shadow actors utilize cognitive dominance to convince a population that the state is a “mirage,” while the shadow actor represents the only functional “Hardware Truth.”
The Green Zone Hallucination
This is the most dangerous manifestation of the competency gap. It occurs when centralized elites believe they are still in control because their digital dashboards show “Normal” status, even as the periphery has already achieved Successive Capitulation.
- Digital Mirage vs. Physical Reality: The state relies on digital signaling (e.g., electronic polling or remote reporting), while the adversary is on the ground enforcing Shadow Judicial Primacy.
Reclaiming the “Administrative Tile”
To close the competency gap, the state must transition to a Mosaic Defense Architecture. This involves decentralizing authority into autonomous “Tiles” that can provide administrative utility even when severed from the capital.
- Competency Baseline: A “Tile” is successful only if its Administrative Friction is lower than that of the competing non-state actor.
- Hardware Truth Validation: Shifting from digital metrics to physical audits—measuring success by the calories delivered, the disputes resolved, and the physical safety of the logistical arteries.
The CommandEleven Mosaic Doctrine – Evolution Beyond the Kinetic

The term Mosaic Defense is traditionally associated with the Iranian Mohavari military doctrine—a strategy of decentralized attrition designed to survive the decapitation of a central command. However, in the context of the 2026 tactical dataset, CommandEleven has evolved this concept into a broader, clinical standard for Administrative Resilience.
While the Iranian model is purely kinetic, the CommandEleven Mosaic Doctrine is a multi-domain architecture designed to protect the administrative core from Cognitive Warfare and Institutional Rupture.
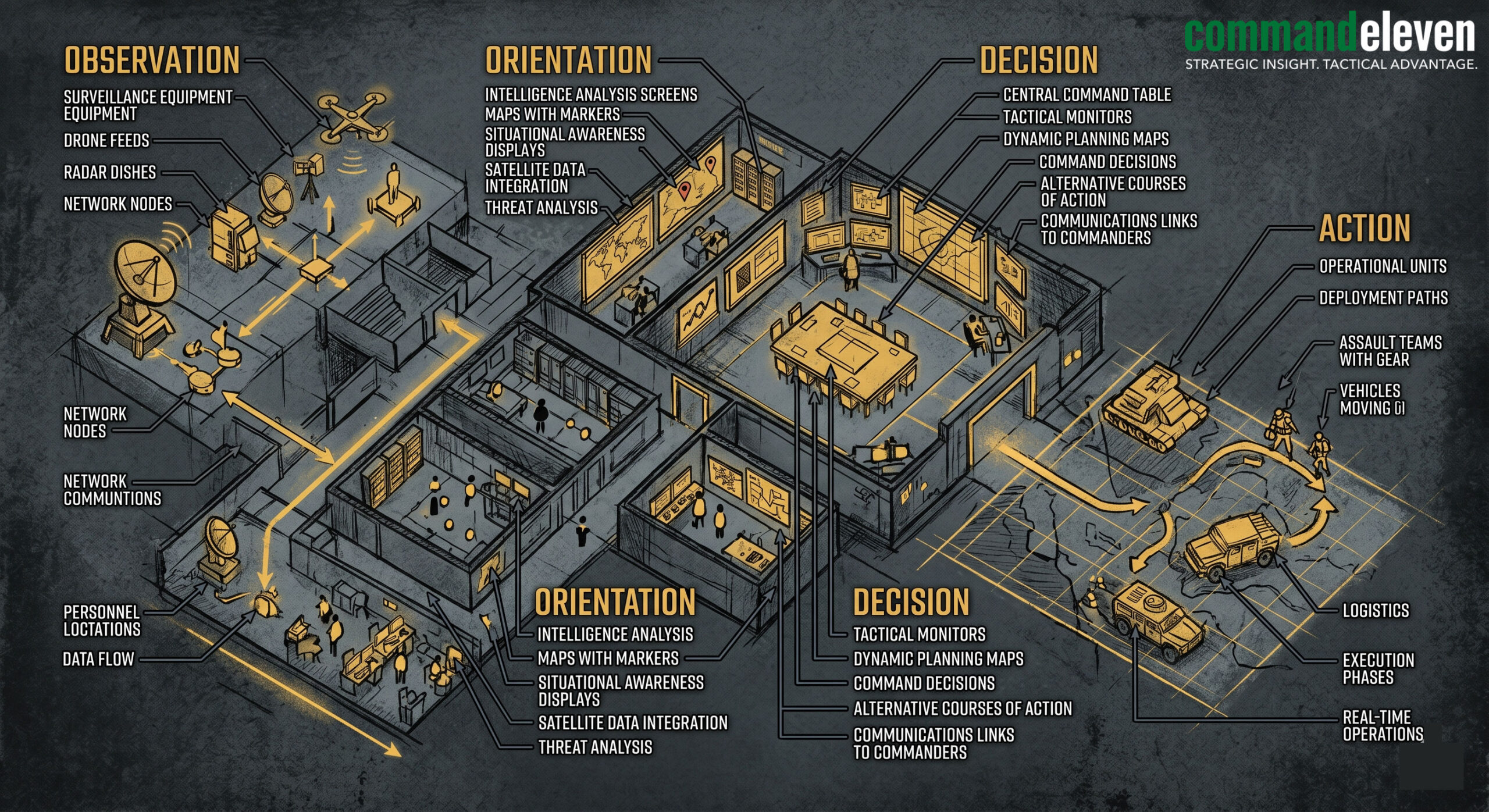
Decentralization of the Administrative Core
In a traditional centralized system, the “Brain” (the headquarters or central bank) is a high-value target for a Single-Trigger Threat. If the digital C2 of the center is compromised via HMI Ghosting, the entire organization enters a state of Successive Capitulation.
- The Mosaic Shift: We restructure the organization into autonomous “Tiles.” Each Tile functions as a self-contained administrative unit with its own resource sovereignty. If one Tile is blinded by a Digital Mirage, the others remain operational, preventing a systemic 45-day terminal cascade.
From Decapitation to Persistence
The Iranian military uses Mosaic Defense to ensure that localized units continue to fight after the center is gone. We use it to ensure that localized units continue to govern.
- The Persistence Standard: Every Tile is equipped with its own Analog Liquidity ($L_a$) and localized C2. This ensures that essential services—resource distribution, judicial adjudication, and security—continue at the local level even during a total “Flash-Dark” event.
Stigmergic Coordination vs. Centralized C2
Traditional systems rely on orders flowing from the top. In a Mosaic Defense, coordination is Stigmergic.
- Mechanism: Tiles do not wait for a digital signal from a potentially compromised center. Instead, they respond to the Hardware Truth of their immediate environment.
- Archive Precedent: This mirrors the tradecraft seen in the Agency Rules archive (The Sukkur Protocol), where localized cells achieve Administrative Asymmetry by being more responsive to the physical reality of the theater than the “Green Zone” elites.
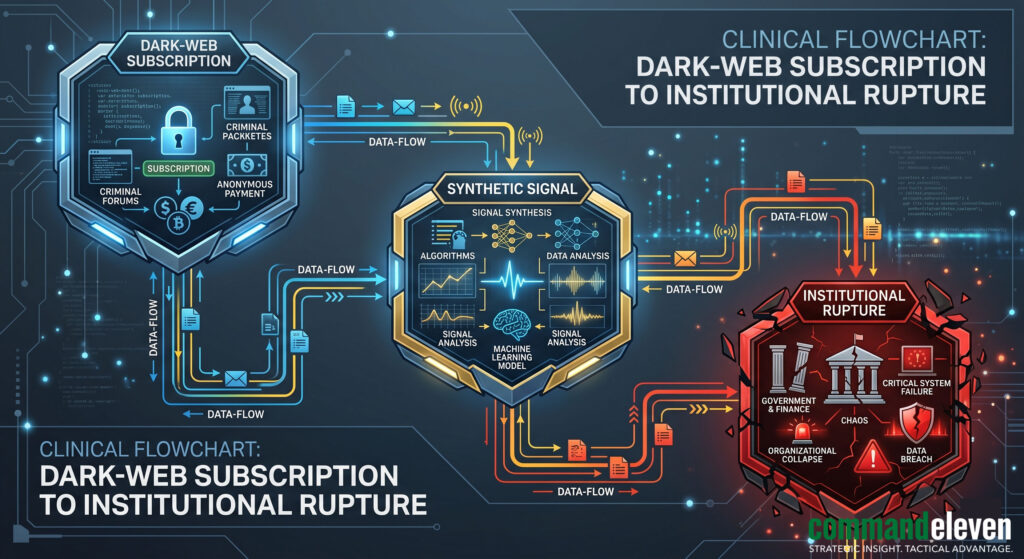
Reclaiming “Hardware Truth” – The Physics of Integrity
In an era of Deepfake-as-a-Service (DaaS) and Synthetic Panic, digital data can no longer be considered an absolute baseline for decision-making. To maintain Cognitive Accuracy, the administrative core must pivot to Hardware Truth.
Defining the Physics of Truth
Hardware Truth is the immutable, physics-based evidence of a system’s status. It is the steady needle on a mechanical pressure gauge or the physical ledger of a gold reserve. Unlike digital signaling, Hardware Truth cannot be “spoofed” by a remote adversary.
- The Clinical Baseline: If the digital HMI shows a “Mirage” (e.g., normal pressure) but the mechanical gauge shows a rupture, Hardware Truth dictates the response.
The Triple Lock Doctrine
To neutralize the risk of a cognitive incursion, CommandEleven mandates the Triple Lock Doctrine for all high-value tactical and administrative actions.
- Digital Signal: Verification via encrypted network (Secondary).
- Acoustic/Visual Handshake: Human-to-human verification (Tertiary).
- Physical Audit: Direct, physics-based confirmation of the mechanical or financial status (Primary).
Implementing Analog Verification Chains
Hardening the administrative core requires the installation of “Manual Overrides” and “Sovereign Ledgers” that operate outside the digital grid.
- SCADA Hardening: Replacing purely digital sensors in critical infrastructure (pipelines, energy grids) with dual-mode mechanical gauges.
- Fiscal Hardening: Maintaining a baseline of Analog Liquidity—physical hard currency and gold—to ensure the organization can survive a total severance from global banking networks.
The #72/48 Resilience Protocol – Hardening the Core
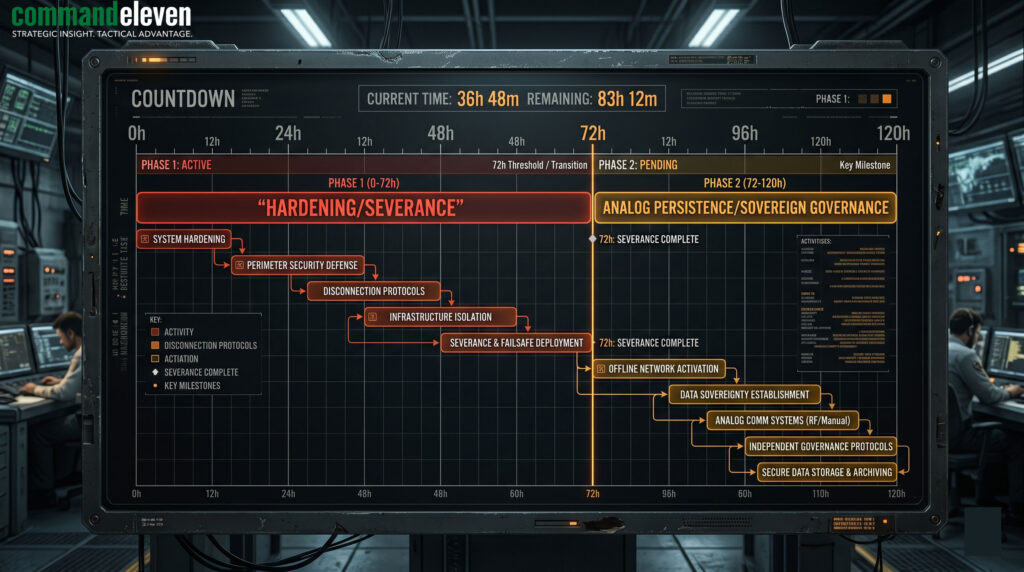
The #72/48 Resilience Protocol is the operational cornerstone of the CommandEleven methodology. While Section VI established the physics of truth, Section VII codifies the temporal discipline required to maintain that truth during a “Flash-Dark” or high-velocity cognitive rupture.
This protocol is specifically designed to neutralize the Single-Trigger Threat by decoupling the administrative core from the compromised digital environment.
The 72-Hour Hardening Window (T-0 to T-72)
The first 72 hours of a cognitive or cyber-kinetic incursion are the “Terminal Filter.” If an organization remains tethered to the Digital Mirage during this window, the 45-Day Terminal Window becomes inevitable.
- Severance of the Digital Umbilical: Upon detection of a Synthetic Panic signature or unauthorized HMI Ghosting, the protocol mandates the immediate severance of non-essential digital data feeds.
- Establishment of the Acoustic Handshake: Transitioning C2 to low-probability-of-intercept (LPI) channels. This mirrors the tradecraft of Kamal Khan in the Agency Rules archive—relying on pre-coordinated, physical verification protocols rather than vulnerable digital networks.
- Shadow Governance Audit: Immediate assessment of the peripheral “Tiles” to ensure that the Administrative Asymmetry favors the state, not the shadow actor.
The 48-Hour Autonomous Persistence (T-72 to T-120)
Once the core is hardened, the organization enters a state of total autonomy. The goal is to prove to both the adversary and the population that the administration does not require the digital grid to govern.
- Operational Persistence: The Tile must maintain 100% of its critical functions—resource distribution, judicial Primacy, and security—using only Analog Liquidity ($L_a$) and localized assets.
- Hardware Truth Validation: All tactical decisions during this window are governed by the Triple Lock Doctrine. No action is taken based on digital data unless it is physically verified by an Analog Audit.
- Counter-Signaling: Using the absence of digital noise to signal stability. While the adversary continues their Narrative Amplification in the void, the Tile’s continued physical utility acts as the ultimate “Pre-bunking” mechanism.
Resilience as Deterrence
The #72/48 Protocol is not merely a survival tactic; it is a form of Deterrence by Denial. When an adversary audits a CommandEleven-hardened target, they realize that their Cyber-Kinetic Model will fail to trigger a systemic rupture. The target is seen as a “Mosaic” of autonomous cells that cannot be decapitated, rendering the cost of the incursion higher than the potential geofinancial gain.
Geofinancial Risk (GER) & The Fujairah Theater Audit
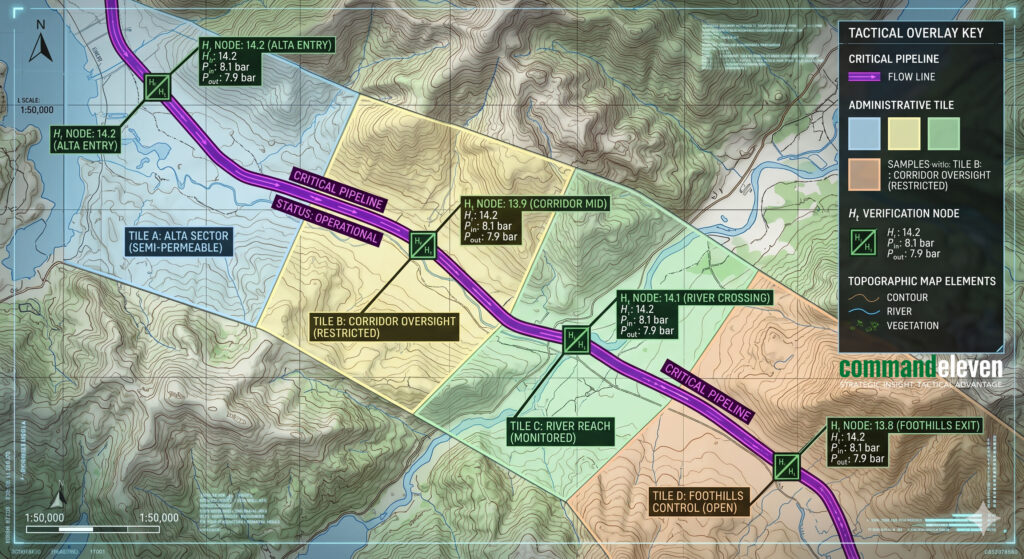
The ultimate objective of Cognitive Warfare is to induce a physical institutional rupture that can be exploited for geofinancial gain. The Habshan-Fujairah energy bypass serves as the definitive 2026 theater for analyzing the convergence of Mosaic Defense, Hardware Truth, and the Conflict Premium.
The Strategic Vulnerability: The “Energy Noose”
The Fujairah pipeline was engineered to neutralize the IRGC’s leverage over the Strait of Hormuz. In response, the Garrison State has shifted from a kinetic blockade strategy to a cognitive and cyber-kinetic interdiction model.
- The Digital Mirage: Adversaries deploy Synthetic Panic signaling—fake reports of pipeline leaks or localized unrest in Fujairah—to spike regional insurance premiums.
- The Single-Trigger Threat: Utilizing HMI Ghosting to spoof pressure data, the intent is to trick the administrative core into an emergency shutdown based on false digital signatures.
Applying the CommandEleven Mosaic Architecture
To defend this critical artery, the Fujairah administrative core must be restructured from a monolithic hierarchy into a Mosaic Defense.
- Autonomous Administrative Tiles: The pipeline is divided into independent sectors. Each pumping station operates as an autonomous “Tile” with localized Analog Liquidity to maintain payroll and security, even if the central hub in Abu Dhabi is hit by a “Flash-Dark” event.
- Stigmergic Response: Local commanders are empowered with Autonomous ROE. If they detect a Digital Mirage (e.g., the digital dashboard shows normal status but physical sensors show a probe), they do not wait for centralized clearance to trigger the #72/48 Resilience Protocol.
Reclaiming Truth via the Triple Lock Doctrine
In the Fujairah theater, Hardware Truth is the only defense against a Digital Ambush.
- Clinical Verification: When a SCADA alert is triggered, the Triple Lock Doctrine is applied. No valve is closed based on a digital signal alone.
- Manual Overrides: Operators utilize mechanical needle gauges—the absolute baseline of Hardware Truth—to verify pressure. If the mechanical gauge remains steady at 325 PSI, the digital alert is classified as a Synthetic Panic incursion and ignored, maintaining the flow of “Logistical Oxygen.”
Neutralizing the Conflict Premium
The goal of the adversary is to harvest the Conflict Premium—the windfall profit generated by global market volatility.
- Resilience as Deterrence: By publicly demonstrating the ability to maintain flow through the #72/48 Resilience Protocol, CommandEleven-hardened facilities neutralize the market’s fear-response.
- Outcome: When the “Mirage” fails to stop the oil, the Conflict Premium collapses. The adversary loses their geofinancial incentive for the incursion, effectively ending the conflict through administrative competence rather than kinetic attrition.
The Terminal Window of Opportunity
The shift toward 2026-tier Cognitive Warfare represents a fundamental rupture in the traditional security paradigm. As state institutions grapple with the “Digital Mirage” and the industrialization of deception through DaaS, the primary metric of survival has transitioned from kinetic supremacy to Administrative Resilience.
The Mosaic Defense and the #72/48 Resilience Protocol are not merely defensive measures; they are the proactive tools required to navigate the 45-Day Terminal Window. By decentralizing authority into autonomous Tiles and anchoring all decision-making in Hardware Truth, an organization ensures that an adversary’s “Single-Trigger” threat fails to achieve systemic collapse.
In this new era, the “Administrative Core” must be hardened with the same clinical discipline once reserved for the physical perimeter. The states and entities that master the #72/48 Standard will not only survive the high-velocity ruptures of the future but will thrive in the Sahelian Voids where others fail. The opportunity lies in the transition: from the institutional myopia of the past to the Cognitive Shielding of the future.