Cognitive Warfare: The New Frontline of Administrative Hardening & The CommandEleven Methodology
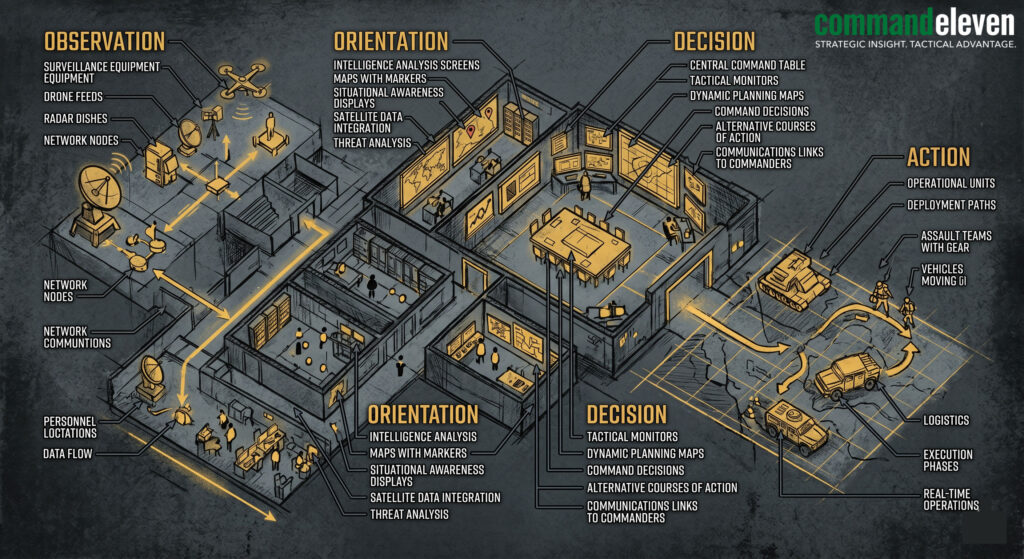
Clinical white paper on neutralizing DaaS and cognitive incursions using the #72/48 Resilience Protocol, Hardware Truth, and Mosaic Defense architectures.
The “Hardware Truth” of the Transnational Border Void
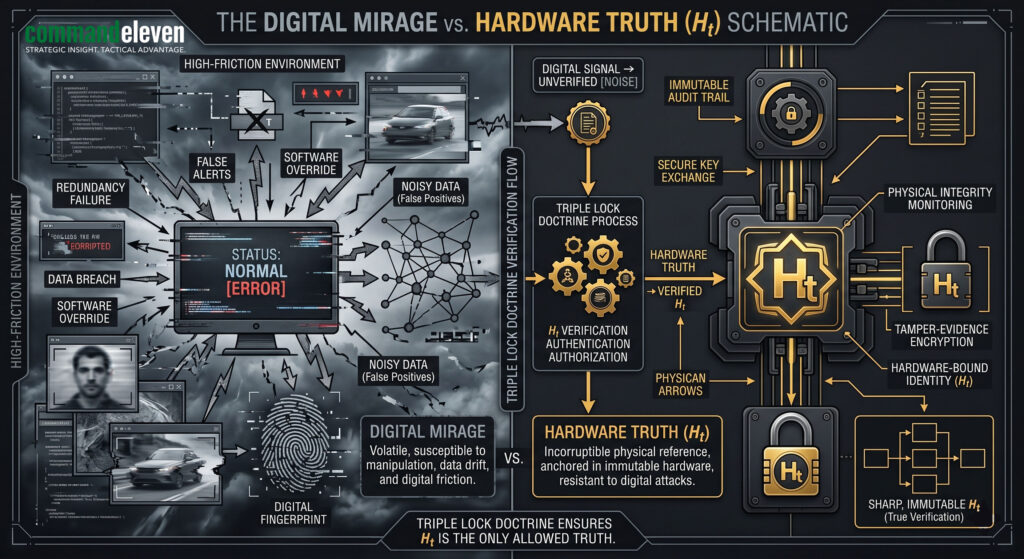
Clinical audit of the Afghan-Pakistan borderlands. Analysis of Digital Mirages, Conflict Clusters, and the #72/48 Resilience Protocol in the “Void.”
The Successive Capitulation of the Indus Logistical Corridor
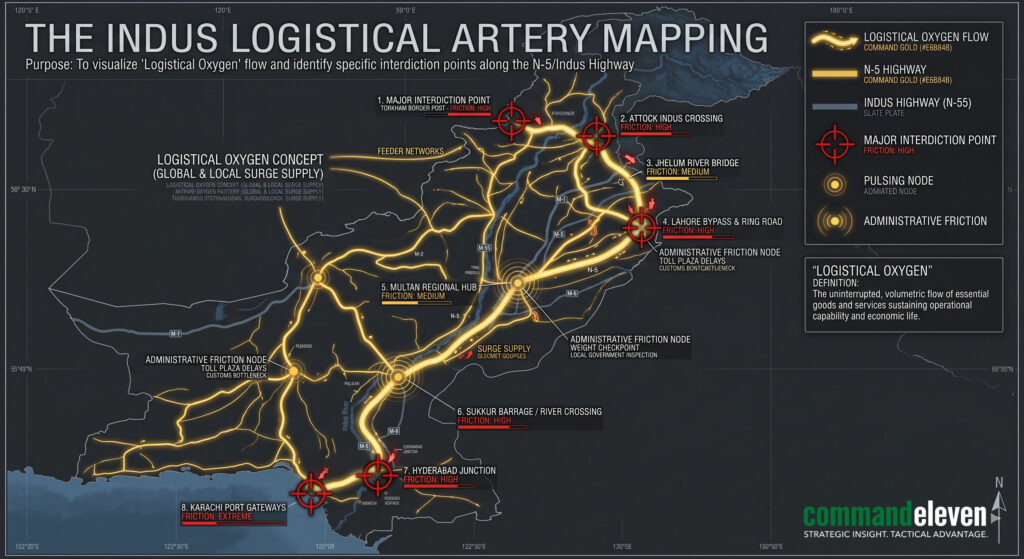
A clinical audit of the Indus Highway (N-5) vulnerability. Analysis of the Bamako Blueprint, Administrative Asymmetry, and the Sukkur Protocol in Pakistan’s logistical core.
