Summary
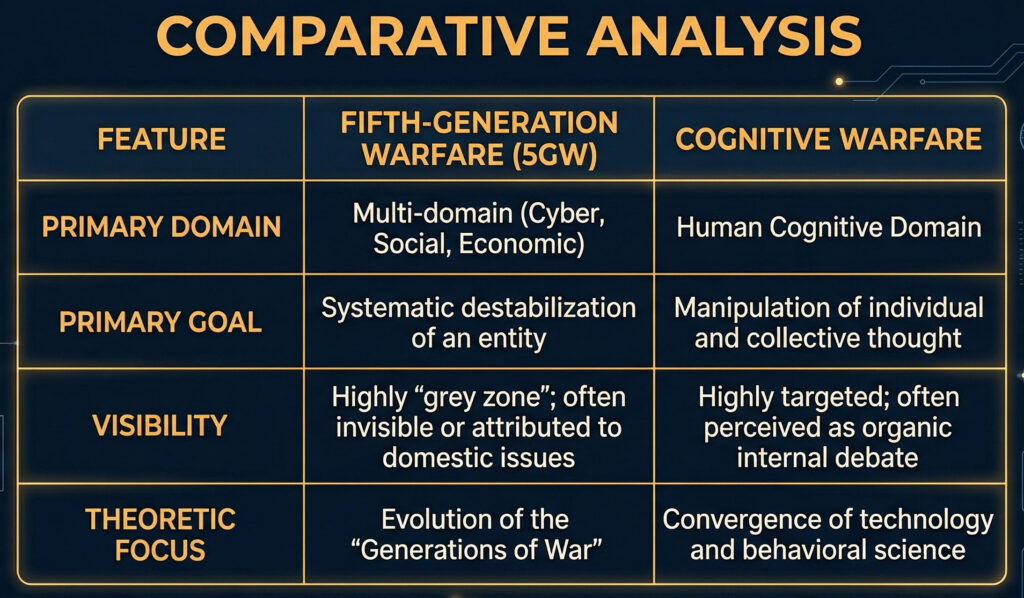
This assessment details the doctrinal shift from Fifth-Generation Warfare (5GW) to Cognitive Warfare (CW). While 5GW focuses on systemic destabilization through multi-domain “grey zone” tactics, Cognitive Warfare weaponizes neurobiology and AI-led deceptive architectures to target human decision-making. By exploiting the “Cognitive Kill Chain,” adversaries can bypass physical defenses to achieve “dopaminergic capture” and “synaptic re-wiring.” Defense requires transitioning from traditional cybersecurity to Cognitive Security (CogSec), anchored in Human-Verified Ground Truth (HVGT) and the proactive exhaustion of enemy analytical bandwidth.
Modern conflict has evolved beyond the “Omni-Domain Fog” of 5GW into the “Bio-Digital Siege” of Cognitive Warfare. The battlespace is no longer just cyber or economic; it is the human brain. To survive, organizations must adopt CogSec protocols – hardening the “human wetware” through pre-bunking and bias awareness while projecting synthetic realities to drain adversary resources.
5 Key Takeaways
- Target Shift: 5GW targets the infrastructure and systems of a state; CW targets the synapse and executive function of the individual.
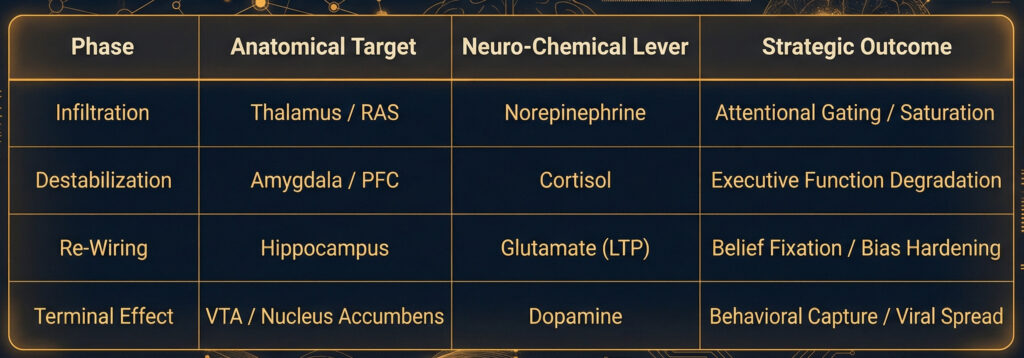
- The Cognitive Kill Chain: A four-phase biological siege (Infiltration, Destabilization, Re-Wiring, Terminal Effect) designed to strip a target of strategic autonomy.
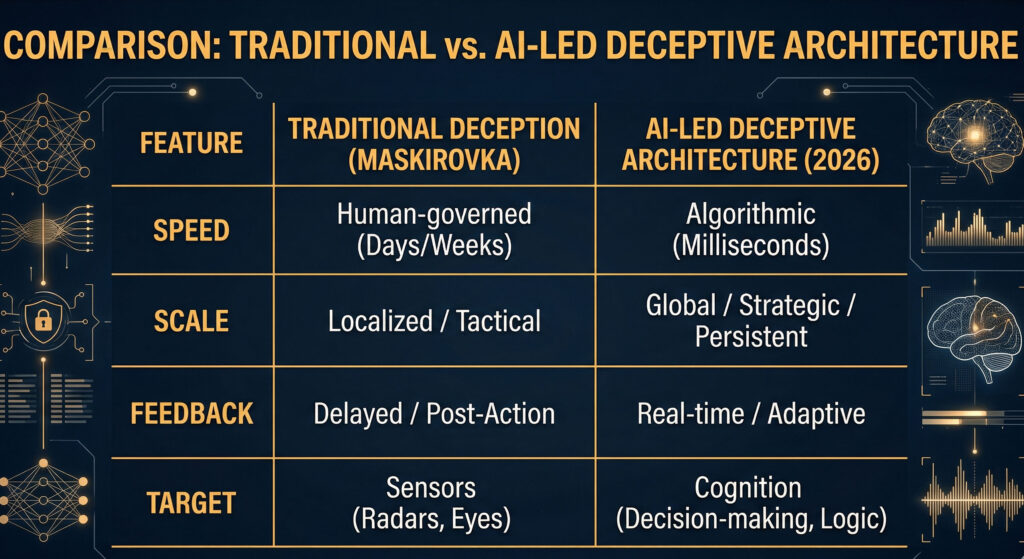
- AI-Led Deceptive Architecture: The use of synthetic realities and “agentic” AI to create a recursive feedback loop that induces decision paralysis in commanders.
- Operational Supremacy: CW is superior to 5GW because it seizes the “Orient” phase of the OODA loop, making adversary responses predetermined rather than merely delayed.
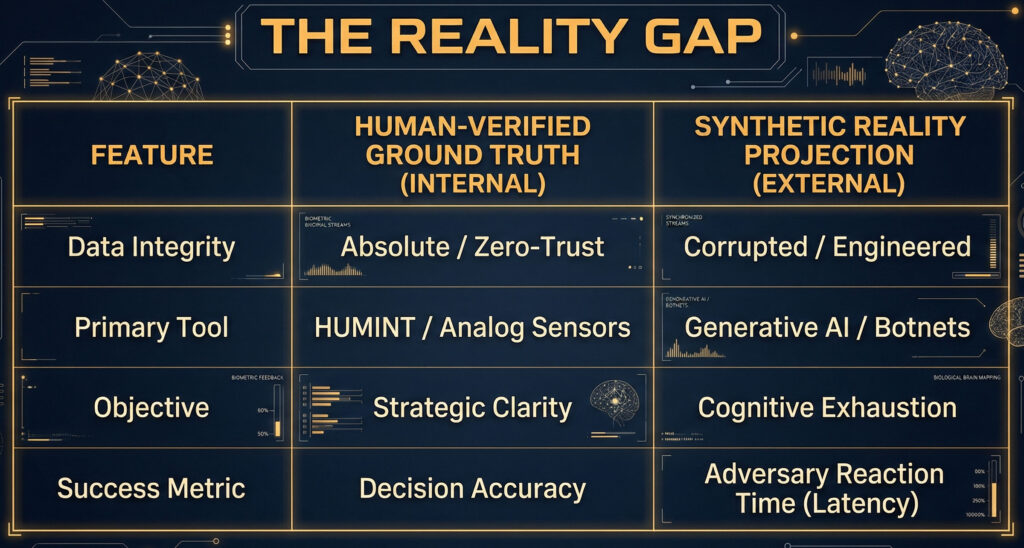
- The HVGT Mandate: In a world of 99.9% fidelity deepfakes, “Human-Verified Ground Truth” is the only viable method to maintain an unassailable internal reality.
Transition from 5GW to Cognitive Dominance
Defining the Operational Parameters
Fifth-Generation Warfare: The Omni-Domain Fog
5GW is characterized by the total blurring of lines between kinetic and non-kinetic, military and civilian, and state and non-state actors. It is “warfare by a thousand cuts,” utilizing highly decentralized networks to achieve strategic effects without a formal declaration of hostilities. In 5GW, the battlefield is everywhere and nowhere; the objective is the systemic destabilization of an adversary’s socio-political infrastructure.
Cognitive Warfare: The Bio-Digital Siege
Cognitive Warfare is the systematic engineering of the human “wetware.” It transcends Information Operations (IO) and Psychological Operations (PSYOP) by integrating neurobiology, psychology, and high-frequency data analytics to manipulate the very processes of perception and reasoning. While 5GW targets the system, CW targets the synapse. It seeks to turn the individual’s own mind into a weapon against their state, community, and self.
Comparative Analysis of Methodology and Use Cases
5GW: Systemic Paralysis (Case: The “Grey Zone” in Eastern Europe)
The 2014 annexation of Crimea remains the textbook 5GW application. It utilized “Little Green Men” (deniable kinetic actors), economic leverage, cyber disruptions of power grids, and a heavy layer of misinformation to paralyze the decision-making cycles of both the target state and international observers.
- Uses: Destabilizing regional alliances, seizing territory via ambiguity, and eroding the sovereignty of “near-abroad” states.
- Impacts: Creates a state of perpetual “grey zone” conflict where the threshold for Article 5 or collective defense is never quite met.
- Benefits: High deniability and low cost compared to traditional 3GW maneuvers.
CW: Perception Hijacking (Case: Algorithmic Polarization in the Indo-Pacific)
The weaponization of social algorithms to exacerbate ethnic or political fissures represents the vanguard of CW. By utilizing AI-driven “bots” and micro-targeted content, an aggressor triggers physiological stress responses in a population, leading to mass-scale behavioral changes – riots, bank runs, or the collapse of public trust.
- Uses: Manipulating election outcomes, triggering domestic insurgency, and degrading a nation’s “will to fight” before a single physical asset is deployed.
- Impacts: Long-term “cognitive scarring” where a population loses the ability to distinguish between organic and engineered reality.
- Benefits: Operates at the speed of light, bypassing physical defenses to target the commander’s internal logic.
The Supremacy of the Cognitive Warfare Model
In the hierarchy of modern conflict, Cognitive Warfare is the superior model to 5GW for three critical reasons.
The End of the OODA Loop Contention
5GW seeks to disrupt the adversary’s OODA loop. Cognitive Warfare, however, seizes the loop entirely. When you control the “Orient” phase by manipulating biological and psychological biases, the “Decide” and “Act” phases become predetermined.
Permanent Strategic Effect vs. Temporal Destabilization
5GW targets systems that can be rebuilt. Cognitive Warfare targets the foundational reality of a society. Once a population’s epistemic foundation—their shared understanding of truth—is destroyed, the state ceases to exist as a functional unit.
Force Multiplier via “Human-Centric” Precision
CW is surgical. With LLMs and neural-mapping, we no longer target “the masses”; we target the specific fears, biases, and neuro-chemical triggers of the individual decision-maker.
The Cognitive Kill Chain
The Cognitive Kill Chain (CKC) is the operationalized sequence of a cognitive strike. It is a bio-digital siege that treats the human brain as the final tactical objective.
Phase 1: Infiltration (Sensory Gatekeepers)
Targets the thalamus.
- Mechanism: Attentional Gating. By flooding digital environments with high-salience stimuli, an adversary forces the thalamus to prioritize hostile data over legitimate intelligence.
- Neuro-Target: The Reticular Activating System (RAS) is kept in hyper-arousal.
Phase 2: Destabilization (Amygdala Hijacking)
Bypasses the Prefrontal Cortex (PFC) to speak directly to the amygdala.
- Mechanism: Engineering “Existential Stressors” to trigger a chronic Cortisol
- Impact: High cortisol “throttles” the PFC, inducing Cognitive Tunneling and binary, survival-based thinking.
Phase 3: Re-Wiring (Synaptic Plasticity)
A long-term campaign to achieve Long-Term Potentiation (LTP).
- Mechanism: Narrative Synchronization reinforces specific neural pathways (the biological basis of Confirmation Bias).
- Impact: The brain physically prunes away connections associated with dissenting information.
Phase 4: Terminal Effect (Dopaminergic Capture)
Captures the Ventral Tegmental Area (VTA) and reward circuitry.
- Mechanism: Social validation (likes, tribal belonging) provides a Dopamine hit, turning the target into a voluntary vector for the strike.
- Result: The target becomes “self-syncing,” seeking out disinformation for neuro-chemical pleasure.
Intelligence Note: In the 2026 battlespace, the “Kill” in the Cognitive Kill Chain is not the death of the person, but the death of their autonomy. An adversary who successfully completes this chain no longer needs to destroy your army; they simply command your mind to surrender.
AI-led Deceptive Architecture
The integration of AI-led Deceptive Architecture represents the operational convergence of 5GW and Cognitive Warfare. In the 2026 battlespace, deception is no longer a static camouflage or a single false radio transmission. It is a dynamic, agentic environment that adapts in real-time to the observer’s cognitive state.
At CommandEleven, we define Deceptive Architecture as the use of Agentic AI to create a “corrupted hall of mirrors” that saturates the adversary’s sensors and decision-making nodes.
The Architecture of Synthetic Realities
Modern deceptive architecture utilizes generative models to construct entire digital and electromagnetic ecosystems that mimic reality with 99.9% fidelity.
- Persistent Synthetic Personas: AI agents manage thousands of interconnected social accounts, each with unique linguistic histories, emotional triggers, and social circles. These are not “bots”; they are digital sleeper cells that simulate grassroots movements or internal dissent to mask strategic maneuvers.
- Environmental Deepfakes: Beyond human faces, AI-led architecture generates synthetic satellite imagery, SIGINT (Signals Intelligence) noise, and thermal signatures. An adversary’s automated ISR (Intelligence, Surveillance, and Reconnaissance) systems may “see” a division-sized element where only a single 3D-printed transmitter exists.
Recursive Deception: The “Feedback Loop”
The true lethality of AI-led architecture is its adaptability.
- Sensing: AI monitors the adversary’s reaction to a deceptive stimulus (e.g., how quickly they redirect drone assets or change their communication frequency).
- Analysis: The system calculates the adversary’s internal “Certainty Metric.”
- Adjustment: If the adversary shows skepticism, the AI automatically generates “supporting evidence” from a different, seemingly unrelated source to confirm the initial lie – effectively performing a “Double-Cross” at machine speed.
Integration into the OODA Loop
For the intelligence professional, AI-led architecture serves as a Cognitive Jammer. It functions at each stage of the decision cycle:
- Observe: Saturation with “Signal-Noise” makes it impossible to distinguish the needle from the hay.
- Orient: AI-tailored narratives exploit the commander’s known personal biases (identified through deep-data harvesting), ensuring they “interpret” the deception exactly as intended.
- Decide: By introducing “Attribution Ambiguity,” the architecture induces Decision Paralysis. If a commander cannot be 100% sure of the source or nature of a threat, they will hesitate—providing the window for a kinetic or high-level cognitive strike.
Strategic “Lawfare” and Plausible Deniability
In 2026, the EU AI Act and similar global frameworks have attempted to mandate the labeling of synthetic content. However, deceptive architecture is designed to bypass these filters by using “Hybrid Generation”—mixing authentic human data with synthetic prompts. This provides state actors with Plausible Deniability, allowing them to influence foreign elections or military morale while claiming the content is organic “citizen-led” expression.
CommandEleven Assessment
Deceptive Architecture is the “invisible terrain” of the modern battlespace. In 2026, the commander who trusts their raw digital feed has already lost. Superiority now belongs to the actor who can anchor their intelligence in Human-Verified Ground Truth while simultaneously projecting a synthetic reality that consumes the adversary’s cognitive bandwidth.
Human-Verified Ground Truth
To achieve cognitive dominance in the 2026 battlespace, an organization must operate on a dual-track reality: maintaining an unassailable internal “Common Operational Picture” while externally projecting a high-fidelity synthetic environment. This is the ultimate application of the CommandEleven strategy – Information Asymmetry through Cognitive Overload.
Establishing Human-Verified Ground Truth (The “Blue” Reality)
In an era of AI-led deception, digital data is inherently untrustworthy. Human-Verified Ground Truth (HVGT) is the process of anchoring strategic decisions in physical, analog, and “Zero-Trust” verification.
The Triad of Verification
- HUMINT-Primary Validation: Shifting back to high-side, “off-grid” Human Intelligence. Before any digital signal is accepted as truth, it must be cross-referenced with physical observation from assets on the ground who are trained in detecting cognitive anomalies.
- Analog Redundancy: Utilizing non-digital communication and observation methods (e.g., optical signaling, physical runners, or “dead-drop” intelligence) that are immune to algorithmic manipulation or cyber-injection.
- Cryptographic Provenance: Implementing “Chain of Custody” for every data point. Every image or report must be cryptographically signed by a verified human source at the point of origin, ensuring the data has not been “hallucinated” or altered by an intermediary AI.
Projecting the Synthetic Reality (The “Red” Projection)
While the internal organization operates on HVGT, the external projection uses Synthetic Reality (SR) to consume the adversary’s cognitive bandwidth. The goal is to force the adversary to spend 90% of their processing power on “ghosts,” leaving them unable to react to the 10% that is the real threat.
Mechanisms of Cognitive Consumption
- The “Labyrinth” Effect: Using AI to generate thousands of plausible, high-priority “leads” for the adversary’s intelligence analysts. These leads are designed to be just credible enough to require investigation, effectively “DDOSing” the adversary’s human analytical capacity.
- Multi-Modal Deception: Synchronizing synthetic data across all domains. If the adversary checks satellite imagery, they see a convoy. If they intercept SIGINT, they hear the convoy’s radio chatter. If they monitor social media, they see “leaked” videos of the convoy from “local citizens.”
- Induced Pareidolia: Designing patterns in the synthetic noise that trigger the adversary’s specific cognitive biases. If an adversary commander is known to be paranoid about a “flank attack,” the SR will subtly project indicators of a flanking maneuver, forcing them to divert real resources to counter a phantom.
The Operational Loop: “The Reality Gap”
The “Reality Gap” is the delta between what is actually happening (HVGT) and what the adversary perceives (SR).
Strategic Execution
The Commander operates within a “Clean Room” of verified data. Simultaneously, the organization’s AI “Deception Engine” maps the adversary’s sensor network and injects tailored synthetic realities into their nodes. By the time the adversary realizes they are chasing a digital mirage, the real kinetic or political objective has already been secured via the HVGT track.
CommandEleven’s Assessment
In the 2026 multi-domain battlespace, Truth is a resource to be hoarded, and Reality is a weapon to be projected. The actor who can maintain their own cognitive integrity while systematically dissolving their opponent’s will always hold the strategic high ground.
Combating Cognitive Warfare
The defense against cognitive warfare (CW) requires a shift from traditional cybersecurity to Cognitive Security (CogSec). While 5GW defenses focus on infrastructure, CW defense focuses on the integrity of human decision-making and the biological substrate of the brain.
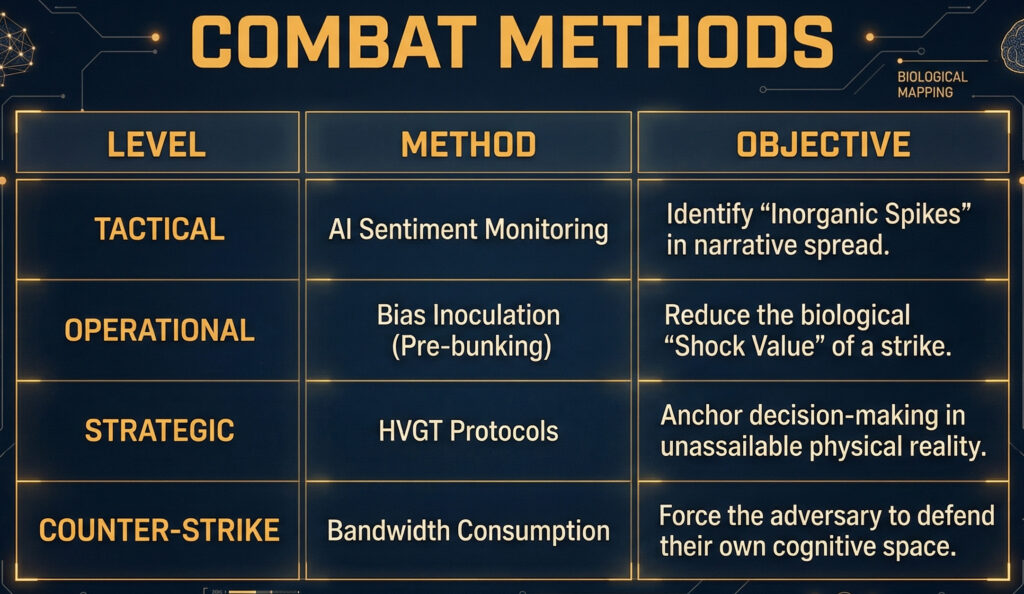
At CommandEleven, we categorize these methods into three operational layers: Detection, Hardening, and Counter-Offensive Adaptation.
Detection: Identifying the Cognitive Incursion
Detecting a CW attack is difficult because the “indicators” are often indistinguishable from organic social shifts. We utilize Behavioral Signal Analysis to flag engineered anomalies.
- Inorganic Sentiment Velocity: AI-driven monitors track the speed at which a narrative spreads. Organic movements grow incrementally; CW strikes often show a “step-function” spike—simultaneous, multi-platform activation that indicates a coordinated “Push” rather than a pull.
- Narrative Path-Mapping: Using Large Language Models (LLMs) to identify the “Genetic Signature” of a narrative. Adversaries often use specific linguistic “tells” or templates. If a narrative appearing in the Indian Sub-continent shares 90% of its structural DNA with a campaign previously run in Eastern Europe, it is flagged as a state-sponsored strike.
- Physiological Telemetry (Internal): For high-level decision-makers, we monitor for “Stress Anomalies.” If a commander’s biometric data (heart-rate variability, cortisol markers) spikes in perfect sync with a specific information feed, it indicates an Amygdala Hijack
Hardening: Building “Cognitive Armor”
Hardening involves pre-emptively strengthening the target to resist the Cognitive Kill Chain.
- Pre-bunking (Inoculation): Just as a vaccine introduces a weakened virus to build immunity, “pre-bunking” exposes a population to a weakened version of a deceptive narrative before the actual strike. By explaining the tactic (e.g., “The adversary will try to use this specific fear to divide you”), the biological impact of the real strike is neutralized.
- Bias Awareness Training: Training operators to recognize their own “Neural Backdoors”—specifically confirmation bias and the availability heuristic. Operators use Red Teaming of Self, where they are forced to argue the exact opposite of their current intelligence assessment to identify where their reasoning has been compromised.
- Zero-Trust Information Protocols: Transitioning from “Trust but Verify” to “Verify, then Trust.” No digital signal—be it a video of a world leader or a field report—is actionable until it has been validated via Human-Verified Ground Truth (HVGT) or cryptographic provenance.
Counter-Offensive: Cognitive Maneuver
Defense alone is insufficient; an adversary must be forced to abandon the cognitive battlespace through Resource Exhaustion.
- Mirroring and Echoing: When a hostile AI-driven narrative is detected, we deploy “Mirror Agents” that reflect the narrative back at the adversary’s own domestic population. This forces the adversary to divert their offensive resources to internal “firefighting.”
- Information Sandboxing: Isolating a suspected cognitive strike within a controlled digital environment. We allow the “virus” to think it is succeeding while we observe its tactics, effectively using the adversary’s own attack as a training manual for our defensive AIs.
- Cognitive Decoys: Projecting Synthetic Realities to lead the adversary’s cognitive assets into “dead ends.” By flooding the adversary’s sensors with high-priority mirages, we consume their analytical bandwidth until their offensive OODA loop collapses from fatigue.
CommandEleven Final Assessment
The most effective defense against cognitive warfare is skepticism as a default. In 2026, if a piece of information makes you feel an immediate, intense emotion (anger, fear, or validation), you must assume you are inside an adversary’s kill chain.
OPERATIONAL INSIGHT: To evaluate the technical frameworks CommandEleven utilizes to mitigate these specific risks, view our Operational Architecture, or our broader Sector Assessment portfolio.


