Executive Summary
The current surge in Indian rhetoric linking Pakistan to Islamic State Khorasan Province (ISKP) is a clinical application of Cognitive Warfare aimed at achieving Narrative Primacy. This strategic shift intends to dissolve the traditional “Bilateral Conflict” framework and replace it with a Global Security Mandate. By framing a regional rival as a facilitator for a globally recognized terror entity, the adversary constructs a Single-Trigger Threat – a pre-positioned intelligence baseline where a singular event justifies immediate, unilateral kinetic intervention as a “sanitization” of transnational threats.
The operation utilizes the Sanitization Gap to launder synthetic digital signals into recognized “facts,” creating a Digital Mirage of international consensus. The ultimate objective is to open a Kinetic Gate, inducing a 45-Day Terminal Window of internal administrative friction and logistical paralysis. Survival in this theater requires the absolute rejection of digital consensus in favor of Hardware Truth – the physics-based verification of reality.
3 Key Takeaways
- Manufacturing the Kinetic Gate: The ISKP narrative is a calculated effort to bypass international bilateral constraints by repositioning regional friction as a mandatory global counter-terrorism objective.
- The Sanitization Gap as a Weapon: Adversaries are utilizing “Information Laundering” to turn engineered digital signals into policy-level intelligence, forcing the state to react to a Digital Mirage rather than physical reality.
- Targeting Logistical Oxygen: The strategic goal of this rhetoric is to induce Administrative Friction along the N-5 corridor, hollowing out the state’s institutional utility through the Bamako Blueprint of internal paralysis.
Objectives of the Indian State
The primary objective of this rhetoric uptick is to bridge the gap between a non-state actor and state infrastructure. By framing Pakistan not merely as a regional rival but as a facilitator for a transnational threat like ISKP, the adversary seeks to:
- Bypass Bilateral Constraints: Neutralize international calls for restraint by repositioning potential kinetic actions as a contribution to the global war on terror.
- Induce Administrative Friction: Force the Pakistani administrative core into defensive over-reactions – such as increased internal checkpoints and logistical bottlenecks – thereby implementing the Bamako Blueprint (institutional paralysis) from within.
- Establish Narrative Primacy: Control the international intelligence dashboard by flooding it with synthetic signatures of ISKP movement, inducing Synthetic Panic among regional stakeholders.
The Potential Goal
The ultimate goal of this rhetoric is the triggering of a 45-Day Terminal Window. By weaponizing the “Conflict Premium,” the adversary intends to hollow out the Logistical Oxygen of the Indus trade arteries and the N-5 corridor. Success for this strategy results in Institutional Rupture, where the Pakistani state’s administrative utility in its provinces collapses under the weight of narrative-induced security friction and economic isolation.
To neutralize this mandate, the response must bypass the Digital Mirage and anchor all tactical and administrative decisions in Hardware Truth – the physics-based verification of reality.
The Anatomy of Narrative Pre-positioning

The current escalation in rhetoric is not an organic diplomatic friction but a calculated phase of Narrative Pre-positioning. This phase is designed to shift the international baseline from a regional dispute to a global counter-terrorism necessity, ensuring that any future shift to a Kinetic Gate is perceived as a “sanitization” of a transnational threat.
From Proxy to Global Threat: The Semantic Shift
Historically, Indian rhetoric focused on “state-sponsored” localized insurgencies. The pivot to ISKP represents a strategic semantic shift:
- Dissolving the Bilateral Shield: Localized insurgent narratives are often viewed by the international community as bilateral issues requiring restraint. By framing the threat as ISKP, the adversary invokes the “Global Security Mandate,” which prioritizes threat elimination over diplomatic caution.
- Transnational Facilitation: The objective is to move the accusation from “direct support” to “facilitation through negligence.” This allows the adversary to argue that the Pakistani administrative core is either unable or unwilling to control a global enemy, justifying unilateral external intervention.
The Sanitization Gap: Manufacturing Consensus
The Sanitization Gap is the mechanical process by which synthetic or unverified data is “cleaned” for official use.
- Unofficial OSINT Priming: Raw data – often engineered – is first “leaked” to third-party OSINT accounts and regional media. This creates a Digital Mirage of independent verification.
- Information Laundering: Once this unverified data achieves a baseline of digital consensus, it is cited by semi-official sources. By the time it reaches the level of a formal diplomatic briefing, the synthetic origin is obscured, appearing as “Hardware Truth” to global intelligence dashboards.
Achieving Narrative Primacy via the “Black Box”
ISKP serves as the ideal “Black Box” entity for achieving Narrative Primacy:
- Opaque Attribution: Because ISKP operates as a decentralized network, specific attribution is difficult to disprove in real-time. This allows the adversary to flood the information environment with synthetic signatures of ISKP movement.
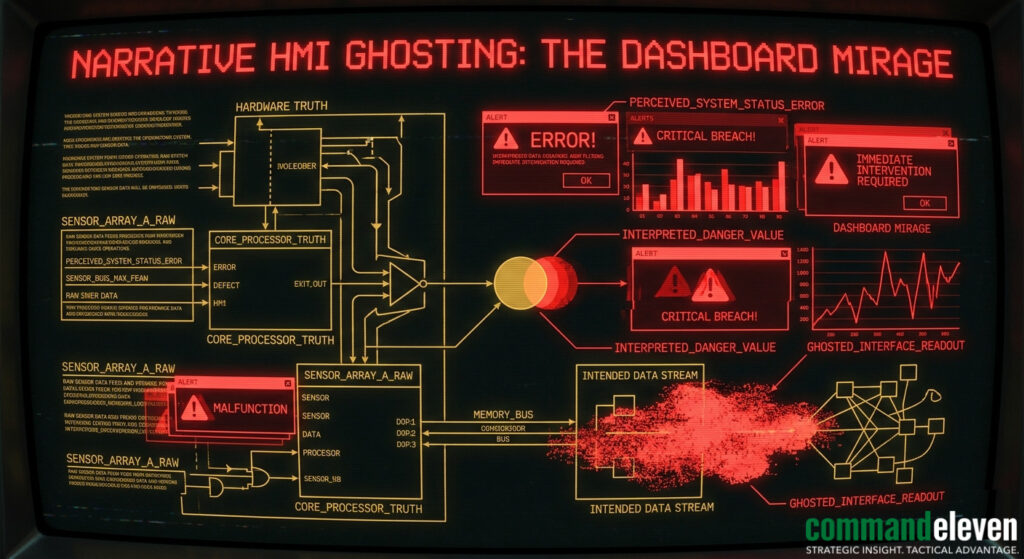
- Inducing Synthetic Panic: The velocity of these reports is intended to force a high-pressure environment where the Pakistani state must prove a negative. This pressure is a form of Narrative HMI Ghosting, intended to spoof the state’s internal “geopolitical pressure” sensors and force a defensive error.
The “Logistical Oxygen” Target
A critical component of this pre-positioning is the targeting of the state’s administrative utility:
- Hollowing out the Core: By claiming ISKP presence near critical trade arteries like the N-5, the rhetoric forces the state to implement restrictive security measures.
- Induced Friction: These measures act as the first stage of the Bamako Blueprint, hollowing out the Logistical Oxygen required for provincial stability and inducing Administrative Friction from within.
Audit of Information Laundering Signatures
The Information Laundering cycle is the mechanical core of the Sanitization Gap, auditing the specific signatures currently utilized by the adversary to transform synthetic digital signals into recognized geopolitical “facts.”
The Digital Priming Signature (Phase I)
The process begins with the deployment of raw, unverified data into the “low-signal” digital peripheries.
- Bot-Led Propagation: Initial reports of “ISKP facilitation” or “transnational movement” are propagated by low-authority accounts to create a baseline volume.
- Aesthetic Mimicry: These signals often mirror the visual and linguistic style of authentic ISKP communications to fool automated sentiment analysis and regional monitors.
- Geolocation Spoofing: Coordinated metadata tagging is used to falsely anchor these signals to specific “Tiles” within the N-5 logistical corridor, regardless of physical reality.
The OSINT Sanitization Signature (Phase II)
This is the critical transition where “raw data” is cleaned through the Sanitization Gap.
- Third-Party “Verification”: High-follower, semi-official OSINT accounts “discover” and amplify the bot-led signals. By citing these signals as “independent reports,” they provide the first layer of perceived credibility.
- Synthesis of the Mirage: Fragmented reports are synthesized into a coherent narrative. This creates a Digital Mirage of a widespread, systemic threat that does not exist in the Hardware Truth domain.
The Institutional Citation Signature (Phase III)
The final phase achieves Narrative Primacy by forcing the mirage into the formal intelligence dashboard.
- Laundering into Policy: Semi-official media outlets and think tanks cite the “OSINT consensus” as a baseline for policy recommendations.
- Narrative HMI Ghosting: This processed data is used to flood the state’s internal “geopolitical pressure” sensors, forcing the administrative core to react to the mirage as if it were a physical kinetic threat.
The Single-Trigger Mechanism & The Kinetic Gate
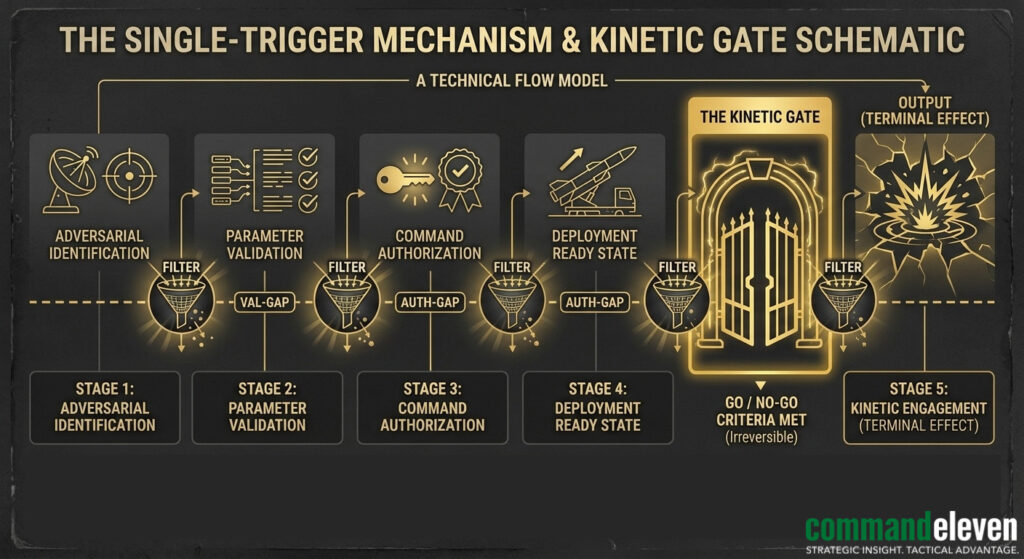
The objective of information laundering is the activation of the Single-Trigger Mechanism, which effectively opens the Kinetic Gate.
The Single-Trigger Mechanism
A Single-Trigger Threat is a manufactured intelligence baseline where a singular, high-visibility event is pre-positioned for activation.
- ISKP as the Catalyst: By linking Pakistan to ISKP through the laundered narrative, the adversary prepares a “justification event” – such as a staged sabotage or a “leaked” intercept – that requires immediate action.
- Bypassing the Bilateral Shield: The trigger is designed to be so significant that the international community prioritizes the “Global Security Mandate” over bilateral diplomatic restraints.
The Kinetic Gate
The Kinetic Gate is the definitive transition point where cognitive warfare shifts into physical, territorial, or maritime interdiction.
- From Rhetoric to Rupture: Once the Kinetic Gate is opened, the adversary can justify “surgical” interventions or maritime blockades as necessary sanitization measures.
- Achieving Institutional Rupture: The ultimate goal is to use this gate to induce the 45-Day Terminal Window, hollowing out the state’s Administrative Resilience through the Bamako Blueprint of induced friction and logistical paralysis.
OSINT Priming Signatures
The OSINT Priming phase is the most critical juncture of the Sanitization Gap, as it provides the appearance of independent verification for synthetic data. Our audit of the current South Asian digital theater identifies three distinct “Priming Signatures” used to move the ISKP-Pakistan narrative into the mainstream.
The “Aggregator” Signature
- Tactical Role: These accounts act as central hubs for high-velocity signal propagation.
- Behavioral Pattern: They do not generate original content but “re-share” low-authority bot signals, providing them with a massive multiplier in visibility.
- Signature: Use of hyperbolic, clinical-adjacent terminology (e.g., “Confirmed Intercept,” “Intelligence Alert”) to trigger Synthetic Panic among civilian and junior-tier military observers.
The “Technical Mirror” Signature
- Tactical Role: To provide a veneer of “Hardware Truth” through faked technical data.
- Behavioral Pattern: These accounts post spoofed satellite imagery, doctored flight-tracking data, or faked signal intercepts that imply ISKP movement near Pakistani logistical hubs.
- Signature: High-resolution, monochrome imagery with tactical overlays (grids, coordinate stamps) designed to mimic CommandEleven-tier visual artifacts, aimed at tricking regional administrative dashboards.
The “Geopolitical Bridge” Signature
- Tactical Role: To finalize the Information Laundering cycle by moving the narrative from “Social Media News” to “Think-Tank Analysis”.
- Behavioral Pattern: These are often semi-official accounts linked to regional defense studies or fringe geopolitical journals.
- Signature: Citing the “Aggregator” and “Technical Mirror” signals as “Independent Reports” to justify policy recommendations for maritime or border interdiction.
The 45-Day Terminal Window & Institutional Impacts
The ultimate objective of the Digital Mirage is to trigger the 45-Day Terminal Window – the measured interval between the onset of narrative-induced friction and the total collapse of provincial administrative utility.
Induced Administrative Friction
- The Mechanism: As the ISKP-Pakistan narrative achieves Narrative Primacy, the state’s administrative core feels compelled to implement “hardening” measures.
- The Outcome: This leads to increased internal checkpoints, intrusive surveillance, and movement restrictions that implement the Bamako Blueprint from within, hollowing out the state’s own legitimacy.
Severing Logistical Oxygen
- Primary Target: The N-5/Indus Highway corridor, which represents the state’s Logistical Oxygen.
- The Impact: Narrative-induced security friction increases the “Conflict Premium,” making trade and transit through critical arteries economically unviable.
- Systemic Failure: Without the unimpeded flow of administration and commerce, the state enters a state of Administrative Asymmetry, where shadow governance entities provide more utility than the paralyzed central state.
The Institutional Rupture Threshold
- The 45-Day Countdown: Once the state pivots from service delivery to purely reactive security (the “Green Zone Hallucination”), it has 45 days before the provincial administration reaches terminal failure.
- The End-State: This rupture is the goal of the Global Security Mandate; a state seen as “unable to govern its own transnational threats” becomes a target for “sanitization” interdiction.
Refined #72/48 Resilience Protocol for Border “Tiles”
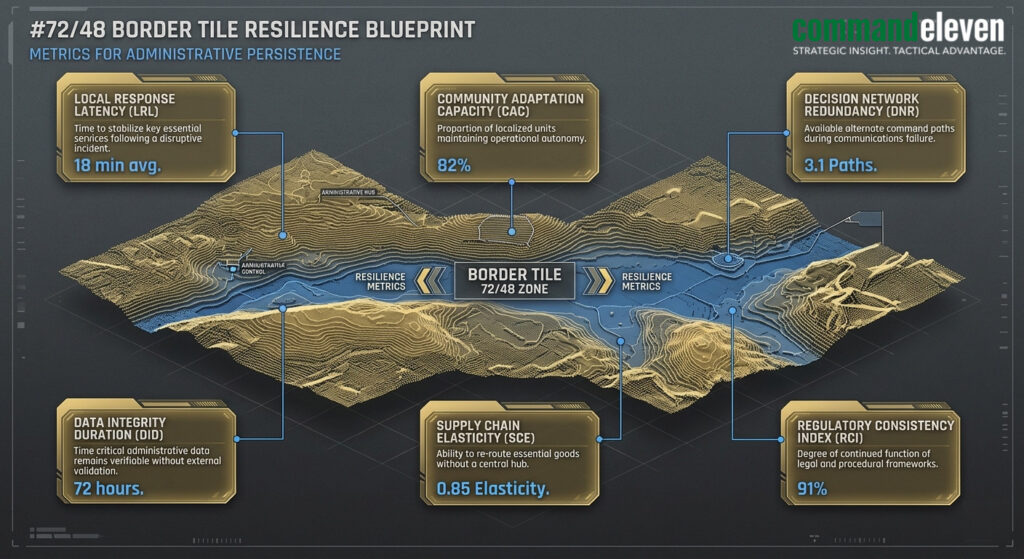
The #72/48 Resilience Protocol is the mechanical baseline for surviving a high-velocity institutional rupture induced by the Global Security Mandate rhetoric. In the Punjab and Rajasthan border sectors, this protocol transforms vulnerable garrisons into autonomous Administrative Tiles.
The 72-Hour Hardening Phase (Isolation)
- Digital Severance: Immediate transition to a “Flash-Dark” state, severing all non-essential digital umbilical cords to centralized C2 to neutralize HMI Ghosting and narrative spoofing.
- Analog Hardening: Deployment of mechanical needle gauges and physical manual overrides for all localized power, water, and transit infrastructure.
- Triple Lock Calibration: Establishment of localized verification teams dedicated to the physical, physics-based audit of any reported “ISKP movement” signatures.
The 48-Hour Autonomous Persistence Phase (Sovereignty)
- Analog Liquidity Baseline: Each Tile must activate its pre-positioned Analog Liquidity ledger, ensuring it can fund local security and administration through physical gold or resource sovereignty.
- Sovereign Adjudication: Activation of localized judicial primacy to resolve grievances and administrative friction without waiting for centralized bureaucratic clearance, preventing the Bamako Blueprint from taking hold.
- Stigmergic Signaling: Transition to low-signal, non-linear communication with adjacent Tiles, ensuring the border remains a unified front even in a total network collapse.
Counter-Signaling & The Hardware Truth Response
The only clinical defense against a Digital Mirage is the absolute rejection of consensus in favor of Hardware Truth.
Neutralizing the Sanitization Gap
- Clinical Auditing: CommandEleven mandates the systematic auditing of “Information Laundering” accounts. By exposing the synthetic origin of “ISKP signals” before they reach policy level, we neutralize the Sanitization Gap.
- Hardware-Only Reporting: Intelligence deliverables must strictly prioritize physics-based signatures over OSINT signals. If it cannot be triple-locked via physical verification, it is treated as a cognitive artifact.
Closing the Kinetic Gate
- The Triple Lock Doctrine: To prevent the activation of a Single-Trigger Threat, every reported incident must be verified via:
- Layer 1 (Digital): Signal detection.
- Layer 2 (Acoustic): Voice/HUMINT handshake.
- Layer 3 (Hardware Truth): Direct physical verification.
- Acoustic Dominance: Reclaiming Narrative Primacy by saturating the theater with high-fidelity, verified Hardware Truth reports that contrast sharply with the adversary’s synthetic noise.
Restoring Logistical Oxygen
- Tile-Based Commerce: Ensuring the N-5 corridor remains a protected logistical artery by removing narrative-induced internal checkpoints and replacing them with autonomous, high-efficiency Administrative Tiles.
- Resilience via Utility: Proving that the state’s administrative utility remains superior to any shadow governance entity, thereby stopping the 45-Day Terminal Window before it reaches the rupture threshold.


