BLUF (BOTTOM LINE UP FRONT)
The United States is currently experiencing a sustained, low-intensity aerial siege of its domestic military infrastructure. Since the late 2024 New Jersey “swarm” events and the escalation of Operation Epic Fury in February 2026, foreign adversaries have successfully mapped the response times, sensor gaps, and legal hesitations of the U.S. defense establishment. Current Counter-UAS (C-UAS) deployment is reactive and hampered by 18th-century “posse comitatus” constraints applied to 21st-century electronic threats. Unless domestic Rules of Engagement (ROE) are overhauled, the National Capital Region (NCR) and strategic nuclear sites remain “glass houses” to anyone with a $3,000 off-the-shelf drone and a customized flight controller.
Key Points
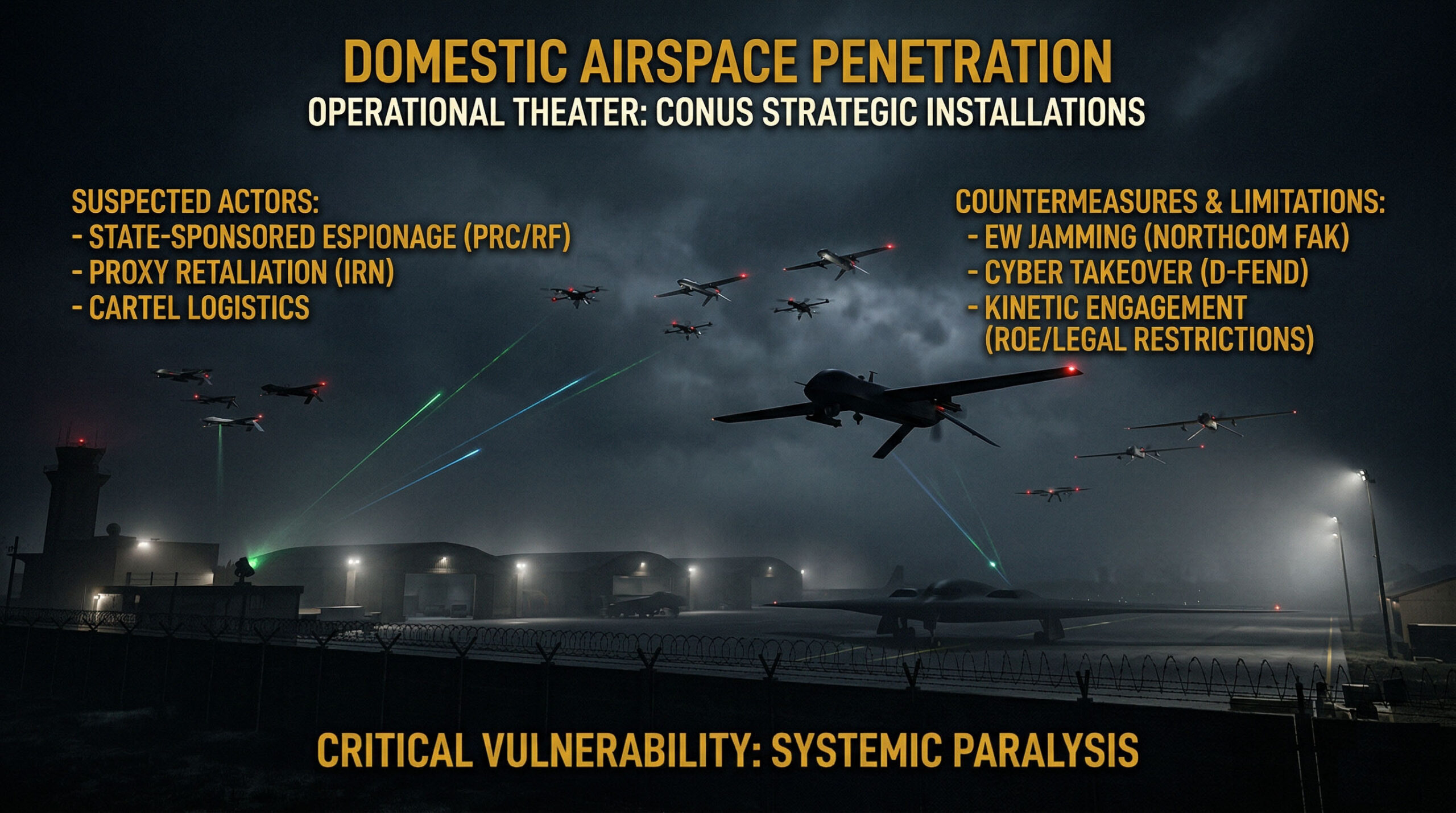
- Persistent Breach of Sovereignty: Unidentified small Unmanned Aerial Systems (sUAS) have transitioned from sporadic nuisances to coordinated, nightly incursions over Tier-1 assets, including Langley AFB, Fort McNair, and Naval Station Norfolk.
- Attribution Ambiguity: While tactical signatures suggest state-sponsored electronic warfare (EW) capabilities, the legal and kinetic “gray zone” allows adversaries – likely Chinese or Iranian-linked – to operate with near-total impunity on U.S. soil.
- Systemic Paralysis: The failure to neutralize these threats is not a technological deficit but a regulatory and jurisdictional deadlock between the Department of War, FAA, and DHS, preventing the employment of kinetic or electronic countermeasures in domestic “non-combat” zones.
Situational Assessment: The New Normal
Over the last 18 months, the frequency and sophistication of drone sightings over U.S. bases have moved beyond “hobbyist” behavior.
The Langley Incursions (2024-2026):
Beginning in December 2023 and escalating through the spring of 2026, Langley-Eustis – home to the F-22 Raptor – was probed for 17 consecutive nights by craft exceeding 20 feet in length, flying at 100+ mph at altitudes of 4,000 feet. These are not “Costco drones.” These are high-speed, fixed-wing assets capable of bypassing standard Aegis-linked radar that was historically calibrated to filter out birds.
The Washington Perimeter (March 2026):
Within the last 10 days, unidentified swarms were detected over Fort McNair, specifically loitering over the residences of Secretary of State Marco Rubio and Secretary of Defense Pete Hegseth. The intent is clear: psychological signaling.
If the command structure cannot secure its own breakfast tables, it cannot project power in the Persian Gulf.
Threat Actors and Attribution
CommandEleven identifies three primary categories of actors responsible for these incursions, categorized by their tactical “footprint”:
State-Sustained Espionage (China/Russia)
The primary suspect for the Langley and Norfolk incursions is the People’s Republic of China (PRC). The 2024 arrest of Fengyun Shi – a Chinese national caught photographing Navy dry docks with a drone – was the tip of the spear.
- Signature: High-altitude, long-endurance (HALE) platforms acting as “motherships” for smaller swarms.
- Objective: Signature Intelligence (SIGINT) collection. They are sniffing the F-22’s electronic emissions to crack stealth encryptions.
Proxy Retaliation (Iran/Operation Epic Fury)
Following the February 28, 2026, launch of Operation Epic Fury, Iranian-linked “sleeper” cells or sympathizers within CONUS have increased sUAS activity over Barksdale AFB (Global Strike Command).
- Signature: Low-cost, “attritable” drones designed to trigger Force Protection Level (FPCON) Charlie/Delta, exhausting security personnel and disrupting flight schedules.
Non-State Facilitators (Cartels/Proxies)
Cartels have utilized sUAS for years along the Southern Border. Intelligence indicates a “technology transfer” where cartel-managed logistics are being used by foreign intelligence services to “dry-run” payload delivery (explosives or chemical agents) over domestic bases.
The Technology Gap: Detection vs. Neutralization
The US military is not “blind,” but it is “handcuffed.”
Current Detection Capabilities
The U.S. is deploying a “Layered Defense” ecosystem:
- Radar Adaptation: Systems like Echodyne and Robin Radar have been integrated to differentiate between a DJI Mavic and a Canadian Goose.
- RF Scanning: Tools such as Aaronia AG and the Ninja family of sensors can “listen” for the control signals of drones.
The Countermeasures (The “Hardware”)
- Electronic Jamming: The Northcom “Flyaway Kit” (FAK) is the current primary defense. It severs the link between the operator and the drone.
- Cyber Takeover: Systems like D-Fend Solutions’ EnforceAir allow the military to “hack” the drone mid-air and force it to land.
- Kinetic/Directed Energy: High-power microwaves (HPM) and lasers (HEL) are being tested at Joint Base Andrews, but they are rarely fired domestically due to the risk of “collateral electronic damage” to civilian Wi-Fi, cell towers, and medical equipment.
Why the US Hasn’t Stopped Them: The “Legal Black Hole”
The most common question from our clients is: “Why don’t they just shoot them down?”
The answer lies in the U.S. Code Title 10 vs. Title 18 vs. Title 49 deadlock.
- Airspace Ownership: The FAA (Title 49) views every drone as an “aircraft.” Shooting down a drone – even over a military base – is technically a federal crime equivalent to shooting down a Boeing 737.
- Privacy & Civil Liberties: DHS and DOJ are restricted by privacy laws that prevent the widespread “sniffing” of encrypted signals in domestic areas. To jam a drone in New Jersey is to potentially jam the 911 calls of three neighboring townships.
- The “Hostile Intent” Threshold: Commanders have the authority to engage if there is “hostile intent.” However, how do you prove intent at 3:00 AM? If the drone is just hovering, it is “unauthorized,” not “hostile.” Current ROE requires a “gun or a bomb” to be visible, which is impossible at 4,000 feet in the dark.
CommandEleven Strategic Recommendations
The current reactive posture is an invitation for a “Pearl Harbor” event via sUAS. CommandEleven advises the following:
- Designated “Kill Zones”: The Department of War must designate immediate 5-mile kinetic intercept zones around Tier-1 bases where any unidentified sUAS is engaged with Directed Energy (lasers) immediately upon entry, bypassing FAA coordination.
- Signal Blackout Authority: Legally insulate commanders from civil liability for “collateral signal interference” during C-UAS engagements.
- Aggressive Attribution: The U.S. must treat these incursions not as “FAA violations” but as Violations of Sovereignty. If a drone is traced to a specific consulate or “cultural center,” the response must be diplomatic expulsion or mirrored activity over the adversary’s capital.
Conclusion
The drones over US bases are the “white balloons” of 2026. They are testing American resolve and red tape. The technology to stop them exists in warehouses; the courage to use it is currently missing from US courtrooms.
OPERATIONAL INSIGHT: To evaluate the technical frameworks CommandEleven utilizes to mitigate these specific risks, view our Protective Operational Architecture or explore our broader Government and Defense portfolio.